- Home
- The SecOps Group
- Security Practitioner
- CNSP
- CNSP - Certified Network Security Practitioner (CNSP)
The SecOps Group CNSP Certified Network Security Practitioner (CNSP) Exam Practice Test
Certified Network Security Practitioner (CNSP) Questions and Answers
Which of the following is an example of a SUID program?
Options:
/bin/ls
/usr/bin/curl
/usr/bin/passwd
None of the above
Answer:
CExplanation:
In Linux/Unix, theSUID (Set User ID)bit allows a program to execute with the owner’s permissions, typically root, rather than the caller’s. It’s denoted by an s in the user execute field (e.g., -rwsr-xr-x). Common SUID programs perform privileged tasks requiring temporary elevation.
Analysis:
C. /usr/bin/passwd:
Purpose: Updates user passwords in /etc/shadow (root-owned, 0600 perms).
Permissions: Typically -rwsr-xr-x, owned by root. The SUID bit lets non-root users modify shadow securely.
Command: ls -l /usr/bin/passwd confirms SUID (s in user execute).
A. /bin/ls:
Purpose: Lists directory contents, no privileged access needed.
Permissions: -rwxr-xr-x (no SUID).Runs as the calling user.
B. /usr/bin/curl:
Purpose: Transfers data over HTTP/FTP, no root privileges required by default.
Permissions: -rwxr-xr-x (no SUID).
Technical Details:
SUID Bit: Set via chmod u+s
Security: SUID binaries are audited (e.g., find / -perm -u=s) due to escalation risks if writable or poorly coded (e.g., buffer overflows).
Security Implications:CNSP likely highlights SUID as an attack vector (e.g., CVE-1996-0095 exploited passwd flaws). Hardening removes unnecessary SUID bits.
Why other options are incorrect:
A, B:Lack SUID; no privileged operations.
D:Incorrect, as /usr/bin/passwd is a SUID example.
Real-World Context:SUID on /bin/su or /usr/bin/sudo similarly enables privilege escalation, often targeted in exploits.References:CNSP Official Documentation (Linux Security); Linux File Permissions Guide.
The application is showing a TLS error message as a result of a website administrator failing to timely renew the TLS certificate. But upon deeper analysis, it appears that the problem is brought on by the expiration of the TLS certificate. Which of the following statements is correct?
Options:
The communication between the browser and the server is now no longer over TLS.
The communication between the browser and the server is still over TLS.
Answer:
AExplanation:
TLS (Transport Layer Security)secures communication (e.g., HTTPS) using certificates, per RFC 8446. A certificate includes:
Validity Period:Start and end dates (e.g., "Not After: March 8, 2025").
Purpose:Authenticates the server and encrypts the session.
Scenario:An expired TLS certificate (e.g., past "Not After" date). Modern browsers (e.g., Chrome, Firefox) validate certificates during the handshake:
ClientHello:Browser initiates TLS.
ServerHello:Server sends its certificate.
Validation:Browser checks expiration, CA trust, etc.
If expired, browsers reject the handshake, displaying errors (e.g., "NET::ERR_CERT_DATE_INVALID"). No session key is negotiated, andcommunication doesn’t proceed over TLS. Users may bypass warnings (e.g., "Advanced > Proceed"), but this is unencrypted or uses a fallback (not standard TLS), breaking security guarantees.
Security Implications:Expired certificates expose sites to MITM attacks, as trust is lost. CNSP likely emphasizes certificate management (e.g., automation with Let’s Encrypt) to avoid this.
Why other options are incorrect:
B. The communication is still over TLS:False; an expired certificate halts the TLS handshake in compliant browsers. Legacy systems might negotiate insecurely, but this isn’t "TLS" per standards.
Real-World Context:The 2019 Equifax breach partially stemmed from expired certificates missing vulnerabilities.References:CNSP Official Study Guide (TLS/SSL Security); RFC 8446 (TLS 1.3).
If you find the 111/TCP port open on a Unix system, what is the next logical step to take?
Options:
Run "rpcinfo -p
Telnet to the port to look for a banner.
Telnet to the port, send "GET / HTTP/1.0" and gather information from the response.
None of the above.
Answer:
AExplanation:
Port 111/TCP is the default port for the RPC (Remote Procedure Call) portmapper service on Unix systems, which registers and manages RPC services.
Why A is correct:Running rpcinfo -p
Why other options are incorrect:
B. Telnet to the port to look for a banner:Telnet might connect, but RPC services don’t typically provide a human-readable banner, making this less effective than rpcinfo.
C. Telnet to the port, send "GET / HTTP/1.0" and gather information from the response:Port 111 is not an HTTP service, so an HTTP request is irrelevant and will likely fail.
D. None of the above:Incorrect, as A is a valid and recommended step.
References:CNSP "Unix Service Enumeration" (Section on RPC Services) highlights rpcinfo -p as the standard tool for probing port 111/TCP.
Which of the following services do not encrypt its traffic by default?
Options:
DNS
SSH
FTPS
All of these
Answer:
AExplanation:
Encryption ensures confidentiality and integrity of network traffic. Analyzing defaults:
A. DNS (Domain Name System):
Default: Unencrypted (UDP/TCP 53), per RFC 1035. Queries/responses (e.g., “google.com → 142.250.190.14”) are plaintext.
Modern Options: DNS over HTTPS (DoH, TCP 443) or DNS over TLS (DoT, TCP 853) encrypt, but aren’t default in most systems (e.g., pre-2020 Windows).
B. SSH (Secure Shell):
Default: Encrypted (TCP 22), per RFC 4251. Uses asymmetric (e.g., RSA) and symmetric (e.g., AES) crypto for all sessions.
C. FTPS (FTP Secure):
Default: Encrypted (TCP 21 control, dynamic data ports). Extends FTP with SSL/TLS (e.g., RFC 4217), securing file transfers.
Technical Details:
DNS: Plaintext exposes queries to eavesdropping (e.g., ISP snooping) or spoofing (e.g., cache poisoning).
SSH/FTPS: Encryption is baked into their standards; disabling it requires explicit misconfiguration.
Security Implications:Unencrypted DNS risks privacy and integrity (e.g., Kaminsky attack). CNSP likely pushes DoH/DoT adoption.
Why other options are incorrect:
B, C:Encrypt by default.
D:False, as only DNS lacks default encryption.
Real-World Context:The 2013 Snowden leaks exposed DNS monitoring; DoH uptake (e.g., Cloudflare 1.1.1.1) counters this.References:CNSP Official Study Guide (Protocol Security); RFC 1035 (DNS), RFC 4251 (SSH).
What is the response from a closed TCP port which is not behind a firewall?
Options:
ICMP message showing Port Unreachable
A FIN and an ACK packet
A RST and an ACK packet
A SYN and an ACK packet
Answer:
CExplanation:
TCP uses a structured handshake, and its response to a connection attempt on a closed port follows a specific protocol when unobstructed by a firewall.
Why C is correct:A closed TCP port responds with a RST (Reset) and ACK (Acknowledgment) packet to terminate the connection attempt immediately. CNSP highlights this as a key scanning indicator.
Why other options are incorrect:
A:ICMP Port Unreachable is for UDP, not TCP.
B:FIN/ACK is for closing active connections, not rejecting new ones.
D:SYN/ACK indicates an open port during the TCP handshake.
References:CNSP "TCP Scanning" (Section on Port Responses) details RST/ACK as the standard closed-port response.
What kind of files are "Dotfiles" in a Linux-based architecture?
Options:
Library files
Driver files
System files
Hidden files
Answer:
DExplanation:
In Linux, file visibility is determined by naming conventions, impacting how files are listed or accessed in the file system.
Why D is correct:"Dotfiles" are files or directories with names starting with a dot (e.g., .bashrc), making them hidden by default in directory listings (e.g., ls requires -a to show them). They are commonly used for user configuration, as per CNSP’s Linux security overview.
Why other options are incorrect:
A:Library files (e.g., in /lib) aren’t inherently hidden.
B:Driver files (e.g., kernel modules in /lib/modules) aren’t dotfiles by convention.
C:System files may or may not be hidden; "dotfiles" specifically denotes hidden status.
References:CNSP "Linux File System Security" (Section on File Types) defines dotfiles as hidden configuration files.
How would you establish a null session to a Windows host from a Windows command prompt?
Options:
net use \hostname\c$ "" /u:NULL
net use \hostname\c$ "" /u:""
net use \hostname\ipc$ "" /u:""
net use \hostname\ipc$ "" /u:NULL
Answer:
CExplanation:
A null session in Windows is an unauthenticated connection to certain administrative shares, historically used for system enumeration. The net use command connects to a share, and the IPC$ (Inter-Process Communication) share is the standard target for null sessions, allowing access without credentials when configured to permit it.
Why C is correct:The command net use \\hostname\ipc$ "" /u:"" specifies the IPC$ share and uses empty strings for the password (first "") and username (/u:""), establishing a null session. This syntax is correct for older Windows systems (e.g., XP or 2003) where null sessions were more permissive, a topic covered in CNSP for legacy system vulnerabilities.
Why other options are incorrect:
A:Targets the c$ share (not typically used for null sessions) and uses /u:NULL, which is invalid syntax; the username must be an empty string ("").
B:Targets c$ instead of ipc$, making it incorrect for null session establishment.
D:Uses ipc$ correctly but specifies /u:NULL, which is not the proper way to denote an empty username.
References:CNSP "Windows Security Basics" (Section on Null Session Exploitation) details the use of net use with IPC$ for enumeration, noting syntax and historical vulnerabilities.
If a hash begins with $2a$, what hashing algorithm has been used?
Options:
Blowfish
SHA256
MD5
SHA512
Answer:
AExplanation:
The prefix $2a$ identifies thebcrypthashing algorithm, which is based on the Blowfish symmetric encryption cipher (developed by Bruce Schneier). Bcrypt is purpose-built for password hashing, incorporating:
Salt:A random string (e.g., 22 Base64 characters) to thwart rainbow table attacks.
Work Factor:A cost parameter (e.g., $2a$10$ means 2^10 iterations), making it computationally expensive to brute-force.
Format:$2a$[cost]$[salt][hash]
Example: $2a$10$N9qo8uLOickgx2ZMRZoMyeIjZAgcfl7p92ldGxad68LJZdL17lhWy
$2a$: Bcrypt variant (original is $2$; $2a$ fixes a minor bug).
$10$: 1024 iterations.
Next 22 characters: Salt.
Remaining: Hashed password.
Used in /etc/shadow on Linux, bcrypt’s adaptive nature ensures it remains secure as hardware improves. CNSP likely includes it in cryptography modules for its strength over older algorithms like MD5.
Why other options are incorrect:
B. SHA256:Part of the SHA-2 family, outputs a 64-character hexadecimal string (e.g., e3b0c442...), no $ prefix. It’s faster, less suited for passwords.
C. MD5:Produces a 32-character hex string (e.g., d41d8cd9...), no prefix. It’s cryptographically broken (collisions found).
D. SHA512:SHA-2 variant, 128-character hex (e.g., cf83e135...), no $ prefix, not salted by default.
Real-World Context:Bcrypt protects SSH keys and web app passwords (e.g., in PHP’s password_hash()).References:CNSP Official Documentation (Cryptography); Bcrypt Specification, RFC 1321 (MD5).
What is the response from a closed TCP port which is behind a firewall?
Options:
A FIN and an ACK packet
RST and an ACK packet
A SYN and an ACK packet
No response
Answer:
DExplanation:
TCP (Transmission Control Protocol) uses a three-way handshake (SYN, SYN-ACK, ACK) toestablish connections, as per RFC 793. When a client sends a SYN packet to a port:
Open Port:The server responds with SYN-ACK.
Closed Port (no firewall):The server sends an RST (Reset) packet, often with ACK, to terminate the attempt immediately.
However, when afirewallis present, its configuration dictates the response. Modern firewalls typically operate instealth mode, using a "drop" rule for closed ports rather than a "reject" rule:
Drop:Silently discards the packet without replying, resulting inno response. The client experiences a timeout (e.g., 30 seconds), as no feedback is provided.
Reject:Sends an RST or ICMP "Port Unreachable," but this is less common for security reasons, as it confirms the firewall’s presence.
For a closed TCP port behind a firewall, "no response" (drop) is the standard behavior in secure configurations, minimizing information leakage to attackers. This aligns with CNSP’s focus on firewall best practices to obscure network topology during port scanning (e.g., with Nmap).
Why other options are incorrect:
A. A FIN and an ACK packet:FIN-ACK is used to close anestablishedTCP connection gracefully (e.g., after data transfer), not to respond to an initial SYN on a closed port.
B. RST and an ACK packet:RST-ACK is the host’s response to a closed port without a firewall. A firewall’s drop rule overrides this by silently discarding the packet.
C. A SYN and an ACK packet:SYN-ACK indicates an open port accepting a connection, the opposite of a closed port scenario.
Real-World Context:Tools like Nmap interpret "no response" as "filtered" (firewall likely present) vs. "closed" (RST received), aiding in firewall detection.References:CNSP Official Study Guide (Firewall Operations and TCP/IP); RFC 793 (TCP).
What is the response from a closed UDP port which is not behind a firewall?
Options:
ICMP message showing Destination Unreachable
A RST packet
No response
None of the above
Answer:
AExplanation:
UDP is a connectionless protocol, and its behavior when a packet reaches a port depends on whether the port is open or closed. Without a firewall altering the response, the standard protocol applies.
Why A is correct:When a UDP packet is sent to a closed port, the host typically responds with an ICMP Type 3 (Destination Unreachable), Code 3 (Port Unreachable) message, indicating no service is listening. CNSP notes this as a key indicator in port scanning.
Why other options are incorrect:
B:RST packets are TCP-specific, not used in UDP.
C:No response occurs for open UDP ports unless an application replies, not closed ports.
D:A is correct, so "none of the above" is invalid.
References:CNSP "Network Scanning Techniques" (Section on UDP Responses) confirms ICMP Port Unreachable as the standard response for closed UDP ports.
In the context of a Unix-based system, where does a daemon process execute in the memory?
Options:
Kernel space
User space
Answer:
BExplanation:
In Unix-based systems, memory is divided into two primary regions: kernel space and user space, each serving distinct purposes for process execution and system stability.
Why B is correct:Daemon processes are background services (e.g., sshd, cron) that run with elevated privileges but operate in user space. User space is the memory area allocated for user applications and processes, isolated from kernel space to prevent direct hardware access or system crashes. CNSP highlights that daemons run in user space to maintain system integrity, interacting with the kernel via system calls.
Why other option is incorrect:
A. Kernel space:Kernel space is reserved for the operating system kernel and device drivers, which have unrestricted access to hardware. Running daemons in kernel space would pose significant security and stability risks, and it is not the standard practice in Unix systems.
References:CNSP "Unix Process Management" (Section on Memory Spaces) explains the separation of kernel and user space, noting that daemons execute in user space for security reasons.
A system encrypts data prior to transmitting it over a network, and the system on the other end of the transmission media decrypts it. If the systems are using a symmetric encryption algorithm for encryption and decryption, which of the following statements is true?
Options:
A symmetric encryption algorithm uses the same key to encrypt and decrypt data at both ends of the transmission media.
A symmetric encryption algorithm uses different keys to encrypt and decrypt data at both ends of the transmission media.
A symmetric encryption algorithm does not use keys to encrypt and decrypt data at both ends of the transmission media.
A symmetric encryption algorithm is an insecure method used to encrypt data transmitted over transmission media.
Answer:
AExplanation:
Symmetric encryption is a cryptographic technique where the same key is used for both encryption and decryption processes. In the context of network security, when data is encrypted prior to transmission and decrypted at the receiving end using a symmetric encryption algorithm (e.g., AES or Triple-DES), both the sender and receiver must share and utilize an identical secret key. This key is applied by the sender to transform plaintext into ciphertext and by the receiver to reverse the process, recovering the original plaintext. The efficiency of symmetric encryption makes it ideal for securing large volumes of data transmitted over networks, provided the key is securely distributed and managed.
Why A is correct:Option A accurately describes the fundamental property of symmetric encryption—using a single shared key for both encryption and decryption. This aligns with CNSP documentation, which emphasizes symmetric encryption’s role in securing data in transit (e.g., via VPNs or secure file transfers).
Why other options are incorrect:
B:This describes asymmetric encryption (e.g., RSA), where different keys (public and private) are used for encryption and decryption, not symmetric encryption.
C:Symmetric encryption inherently relies on keys; the absence of keys contradicts its definition and operational mechanism.
D:Symmetric encryption is not inherently insecure; its security depends on key strength and management practices, not the algorithm itself. CNSP highlights that algorithms like AES are widely regarded as secure when implemented correctly.
References:CNSP documentation on "Cryptographic Fundamentals" (Section on Symmetric Encryption Algorithms) explains the use of a single key and contrasts it with asymmetric methods, emphasizing secure key exchange challenges.
Which of the following protocols is not vulnerable to address spoofing attacks if implemented correctly?
Options:
UDP
ARP
TCP
IP
Answer:
CExplanation:
Address spoofingfakes a source address (e.g., IP, MAC) to impersonate or amplify attacks. Analyzing protocol resilience:
C. TCP (Transmission Control Protocol):
Mechanism: Three-way handshake (SYN, SYN-ACK, ACK) verifies both endpoints.
Client SYN (Seq=X), Server SYN-ACK (Seq=Y, Ack=X+1), Client ACK (Ack=Y+1).
Spoofing Resistance: Spoofer must predict the server’s sequence number (randomized in modern stacks) and receive SYN-ACK, impractical without session hijacking or MITM.
Correct Implementation: RFC 793-compliant, with anti-spoofing (e.g., Linux tcp_syncookies).
A. UDP:
Connectionless (RFC 768), no handshake. Spoofed packets (e.g., source IP 1.2.3.4) are accepted if port is open, enabling reflection attacks (e.g., DNS amplification).
B. ARP (Address Resolution Protocol):
No authentication (RFC 826). Spoofed ARP replies (e.g., fake MAC for gateway IP) poison caches, enabling MITM (e.g., arpspoof).
D. IP:
No inherent validation at Layer 3 (RFC 791). Spoofed source IPs pass unless filtered (e.g., ingress filtering, RFC 2827).
Security Implications:TCP’s handshake makes spoofing harder, though not impossible (e.g., blind spoofing with sequence prediction, mitigated since BSD 4.4). CNSP likely contrasts this with UDP/IP’s vulnerabilities in DDoS contexts.
Why other options are incorrect:
A, B, D:Lack handshake or authentication, inherently spoofable.
Real-World Context:TCP spoofing was viable pre-1990s (e.g., Mitnick attack); modern randomization thwarts it.References:CNSP Official Documentation (Protocol Security); RFC 793 (TCP), RFC 2827 (BCP 38).
What is the response from an open TCP port which is not behind a firewall?
Options:
A FIN and an ACK packet
A SYN packet
A SYN and an ACK packet
A RST and an ACK packet
Answer:
CExplanation:
TCP’sthree-way handshake, per RFC 793, establishes a connection:
Client → Server:SYN (Synchronize) packet (e.g., port 80).
Server → Client:SYN-ACK (Synchronize-Acknowledge) packet if the port is open and listening.
Client → Server:ACK (Acknowledge) completes the connection.
Scenario:Anopen TCP port(e.g., 80 for HTTP) with no firewall. When a client sends a SYN to an open port (e.g., via telnet 192.168.1.1 80), the server responds with aSYN-ACKpacket, indicating willingness to connect. No firewall means no filtering alters this standard response.
Packet Details:
SYN-ACK: Sets SYN and ACK flags in the TCP header, with a sequence number and acknowledgment number.
Example: Client SYN (Seq=100), Server SYN-ACK (Seq=200, Ack=101).
Security Implications:Open ports responding with SYN-ACK are easily detected (e.g., Nmap “open” state), inviting exploits if unneeded (e.g., Telnet on 23). CNSP likely stresses port minimization and monitoring.
Why other options are incorrect:
A. A FIN and an ACK packet:FIN-ACK closes an established connection, not a response to a new SYN.
B. A SYN packet:SYN initiates a connection from the client, not a server response.
D. A RST and an ACK packet:RST-ACK rejects a connection (e.g., closed port), not an open one.
Real-World Context:SYN-ACK from SSH (22/TCP) confirms a server’s presence during reconnaissance.References:CNSP Official Documentation (TCP/IP Fundamentals); RFC 793 (TCP).
Which SMB (Server Message Block) network protocol versions are vulnerable to the EternalBlue (MS17-010) Windows exploit?
Options:
SMBv1 only
SMBv2 only
SMBv3 only
Both SMBv1 and SMBv2
Answer:
AExplanation:
EternalBlue(MS17-010) is an exploit targeting a buffer overflow in Microsoft’s SMB (Server Message Block) implementation, leaked by the Shadow Brokers in 2017. SMB enables file/printer sharing:
SMBv1 (1980s):Legacy, used in Windows NT/XP.
SMBv2 (2006, Vista):Enhanced performance/security.
SMBv3 (2012, Windows 8):Adds encryption, multichannel.
Vulnerability:
EternalBlue exploits a flaw inSMBv1’s SRVNET driver (srv.sys), allowing remote code execution via crafted packets. Microsoft patched it in March 2017 (MS17-010).
Affected OS: Windows XP to Server 2016 (pre-patch), if SMBv1 enabled.
Proof: WannaCry/NotPetya used it, targeting port 445/TCP.
Version Scope:
SMBv1 Only:The bug resides in SMBv1’s packet handling (e.g., TRANS2 requests). SMBv2/v3 rewrote this code, immune to the specific overflow.
Microsoft: Post-patch, SMBv1 is disabled by default (Windows 10 1709+).
Security Implications:CNSP likely stresses disabling SMBv1 (e.g., via Group Policy) and patching, as EternalBlue remains a threat in legacy environments.
Why other options are incorrect:
B, C:SMBv2/v3 aren’t vulnerable; the flaw is SMBv1-specific.
D:SMBv2 isn’t affected, only SMBv1.
Real-World Context:WannaCry’s 2017 rampage hit unpatched SMBv1 systems (e.g., NHS), costing billions.References:CNSP Official Documentation (Windows Exploits); Microsoft MS17-010 Bulletin.
According to the screenshot below, which of the following statements are correct?
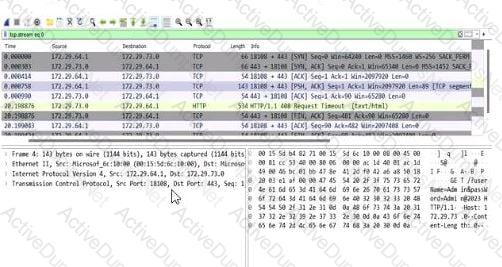
Options:
The application is running on port 443 and the HTTPS protocol.
The credentials have been submitted over the HTTP protocol.
The credentials have been submitted over the HTTPS protocol.
The application is running on port 80 and the HTTP protocol.
Answer:
AExplanation:
The screenshot is from Wireshark, a network protocol analyzer, displaying captured network traffic. The relevant columns include the source and destination IP addresses, ports, protocol, and additional information about the packets. Let’s break down the details:
Destination Port Analysis:The screenshot shows multiple packets with a destination port of 443 (e.g., in the "Destination" column, entries like "172.72.61.9:443"). Port 443 is the default port for HTTPS (HTTP Secure), which is HTTP traffic encrypted using SSL/TLS. This indicates that the application is communicating over HTTPS.
Protocol Analysis:The "Protocol" column lists "TLSv1.2" for most packets (e.g., frame numbers 2000084, 2000086). TLS (Transport Layer Security) is the cryptographic protocol used by HTTPS to secure HTTP communications. This confirms that the traffic is HTTPS, not plain HTTP.
Packet Details:The "Info" column provides additional context, such as "Application Data" for TLS packets, indicating encrypted application-layer data (typical of HTTPS). There are also HTTP packets (e.g., frame 2000088), but these are likely part of the HTTPS session (e.g., HTTP/2 over TLS, as noted by "HTTP2").
Now, let’s evaluate the options:
Option A: "The application is running on port 443 and the HTTPS protocol."This is correct. The destination port 443 and the use of TLSv1.2 confirm that the application is using HTTPS. HTTPS is the standard protocol for secure web communication, and port 443 is its designated port. CNSP documentation emphasizes that HTTPS traffic on port 443 indicates a secure application-layer protocol, often used for web applications handling sensitive data.
Option B: "The credentials have been submitted over the HTTP protocol."This is incorrect. HTTP typically uses port 80, but the screenshot shows traffic on port 443 with TLS, indicating HTTPS. Credentials submitted over this connection would be encrypted via HTTPS, not sent in plaintext over HTTP. CNSP highlights the security risks of HTTP for credential submission due to lack of encryption, which isn’t the case here.
Option C: "The credentials have been submitted over the HTTPS protocol."While this statement could be true (since HTTPS is in use, any credentials would likely be submitted securely), the question asks for the "correct" statement based on the screenshot. The screenshot doesn’t explicitly show credential submission (e.g., a POST request withform data); it only shows the protocol and port. Option A is more directly supported by the screenshot as it focuses on the application’s protocol and port, not the specific action of credential submission. CNSP notes that HTTPS ensures confidentiality, but this option requires more specific evidence of credentials.
Option D: "The application is running on port 80 and the HTTP protocol."This is incorrect. Port 80 is the default for HTTP, but the screenshot clearly shows port 443 and TLS, indicating HTTPS. CNSP documentation contrasts HTTP (port 80, unencrypted) with HTTPS (port 443, encrypted), making this option invalid.
Conclusion:Option A is the most accurate and comprehensive statement directly supported by the screenshot, confirming the application’s use of port 443 and HTTPS. While Option C might be true in a broader context, it’s less definitive without explicit evidence of credential submission in the captured packets.
References:CNSP "Network Traffic Analysis" (Section on Protocol Identification) explains that port 443 with TLS indicates HTTPS, and contrasts it with HTTP on port 80. The "Wireshark Analysis" section further details how to interpret destination ports and protocol fields for identifying application-layer protocols.
On a Microsoft Windows Operating System, what does the following command do?
net localgroup administrators
Options:
List domain admin users for the current domain
Displays the local administrators group on the computer
Answer:
BExplanation:
The net command in Windows is a legacy tool for managing users, groups, and network resources. The subcommand net localgroup
net localgroup administrators lists all members (users and groups) of the local Administrators group on the current computer.
The local Administrators group grants elevated privileges (e.g., installing software, modifying system files) on that machine only, not domain-wide.
Output Example:
Alias name administrators
Comment Administrators have complete and unrestricted access to the computer
Members
-------------------------------------------------------------------------------
Administrator
Domain Admins
The command completed successfully.
Technical Details:
Local groups are stored in the Security Accounts Manager (SAM) database (e.g., C:\Windows\System32\config\SAM).
This differs from domain groups (e.g., Domain Admins), managed via Active Directory.
Security Implications:Enumerating local admins is a reconnaissance step in penetration testing (e.g., to escalate privileges). CNSP likely covers this command for auditing and securing Windows systems.
Why other options are incorrect:
A. List domain admin users for the current domain:This requires net group "Domain Admins" /domain, which queries the domain controller, not the local SAM. net localgroup is strictly local.
Real-World Context:Attackers use this command post-compromise (e.g., via PsExec) to identify privilege escalation targets.References:CNSP Official Documentation (Windows Security Commands); Microsoft Windows Command-Line Reference.
What will be the subnet mask for 192.168.0.1/18?
Options:
255.255.255.0
255.225.225.0
255.255.192.0
255.225.192.0
Answer:
CExplanation:
An IP address with a/18prefix (CIDR notation) indicates 18 network bits in the subnet mask, leaving 14 host bits (32 total bits - 18). For IPv4 (e.g., 192.168.0.1):
Binary Mask:First 18 bits are 1s, rest 0s.
1st octet: 11111111 (255)
2nd octet: 11111111 (255)
3rd octet: 11000000 (192)
4th octet: 00000000 (0)
Decimal:255.255.192.0
Calculation:
Bits: /18 = 2^14 hosts (16,384), minus 2 (network/broadcast) = 16,382 usable.
Range: 192.168.0.0–192.168.63.255 (3rd octet: 0–63, as 192 = 11000000 covers 6 bits).
Technical Details:
Subnet masks align on octet boundaries or mid-octet (e.g., 192 = 2^7 + 2^6).
Contrast: /24 = 255.255.255.0 (256 hosts), /16 = 255.255.0.0 (65,536 hosts).
Security Implications:Larger subnets (e.g., /18) increase broadcast domains, risking amplification attacks. CNSP likely teaches subnetting for segmentation (e.g., VLANs).
Why other options are incorrect:
A. 255.255.255.0:/24 (8 host bits), not /18.
B. 255.225.225.0:Invalid mask (225 = 11100001, non-contiguous 1s).
D. 255.225.192.0:Invalid (225 breaks binary sequence).
Real-World Context:Subnetting 192.168.0.0/18 isolates departments in enterprise networks.References:CNSP Official Documentation (IP Addressing); RFC 1918 (Private IP).
Unlock CNSP Features
- CNSP All Real Exam Questions
- CNSP Exam easy to use and print PDF format
- Download Free CNSP Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
Questions & Answers PDF Demo
- CNSP All Real Exam Questions
- CNSP Exam easy to use and print PDF format
- Download Free CNSP Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet