Microsoft SC-200 Microsoft Security Operations Analyst Exam Practice Test
Microsoft Security Operations Analyst Questions and Answers
The issue for which team can be resolved by using Microsoft Defender for Office 365?
You need to recommend a solution to meet the technical requirements for the Azure virtual machines. What should you include in the recommendation?
You need to remediate ac tive attacks to meet the technical requirements.
What should you include in the solution?
You need to create an advanced hunting query to i nvestigate the executive team issue.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to complete the query for failed sign-ins to meet the technical requirements.
Where can you find the column name to complete the where clause?
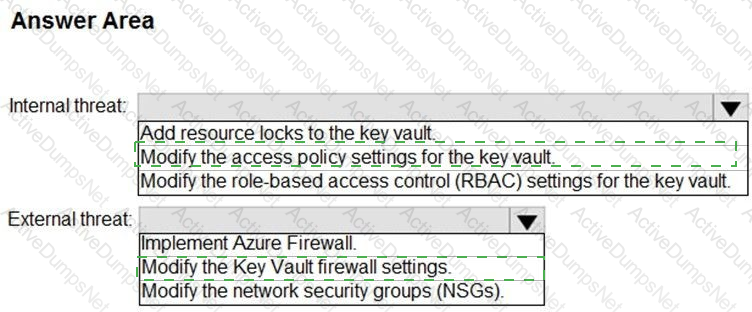
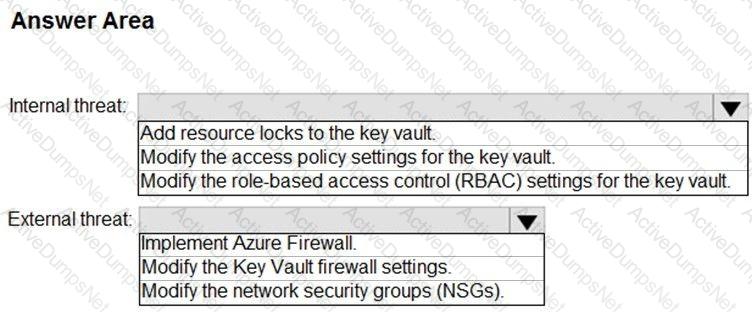
You need to recommend remediation actions for the Azure Defender alerts for Fabrikam.
What should you recommend for each threat? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
The issue for which team can be resolved by using Microsoft Defender for Endpoint?
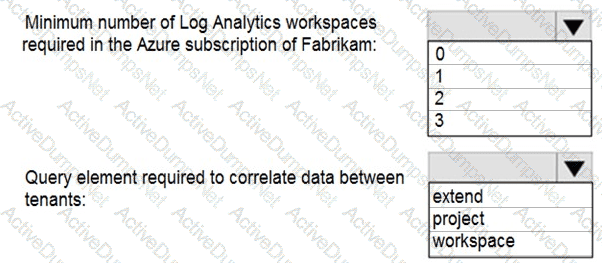
You need to implement Azure Sentinel queries for Contoso and Fabrikam to meet the technical requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area .
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint
You need to create a query that will link the Alertlnfo, AlertEvidence, and DeviceLogonEvents tables. The solution must return all the rows in the tables.
Which operator should you use?
Your company has a single office in Istanbul and a Microsoft 365 subscription.
The company plans to use conditional access policies to enforce multi-factor authentication (MFA).
You need to enforce MFA for all users who work remotely.
What should you include in the solution?
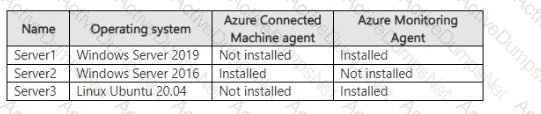
Your on-premises network contains a Hyper-V cluster. The cluster contains the virtual machines shown in the following table.
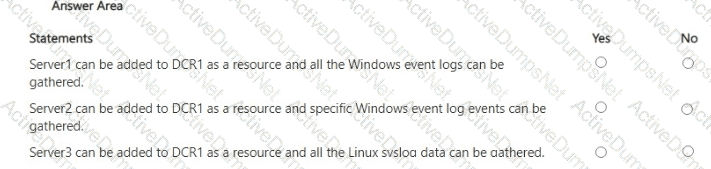
You have a Microsoft Sentinel workspace named SW1.
You have a data collection rule (OCR) that has the following configurations:
• Name: DCR1
• Destination: SW1
• Platform type: All
• Data collection endpoint: None
• Data source: Windows event logs, Linux syslog
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have an Azure Storage account that will be accessed by multiple Azure Function apps during the development of an application.
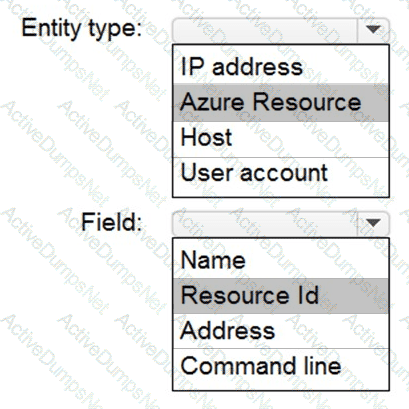
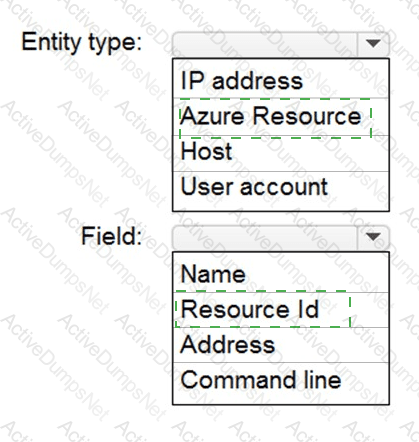
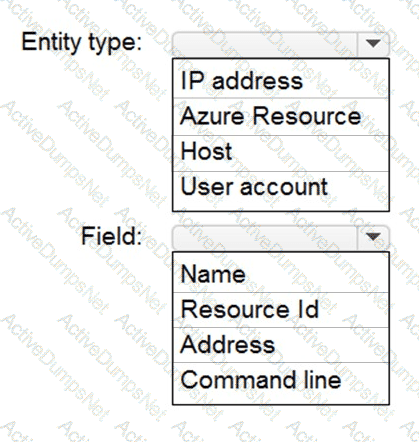
You need to hide Azure Defender alerts for the storage account.
Which entity type and field should you use in a suppression rule? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft Sentinel workspace that contains the following i ncident.
Brute force attack against Azure Portal analytics rule has been triggered.
You need to identify the geolocation information that corresponds to the incident.
What should you do?
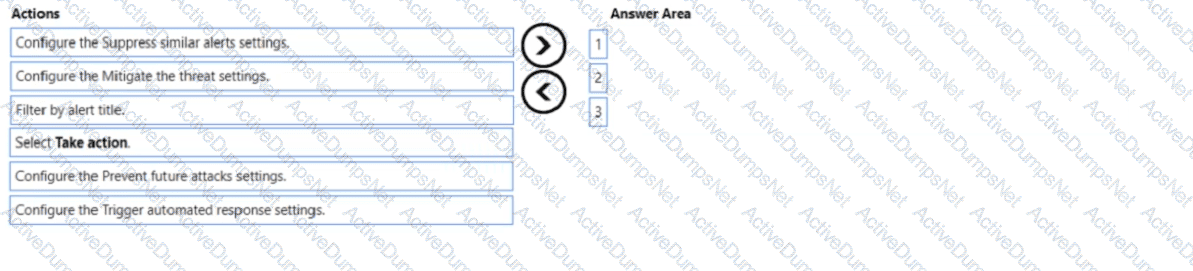
You have a Microsoft subscription that has Microsoft Defender for Cloud enabled You configure the Azure logic apps shown in the following table.
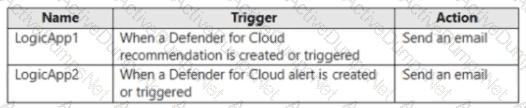
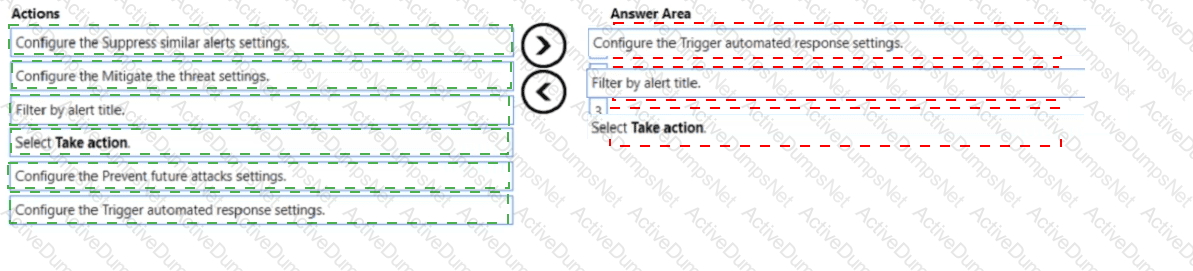
You need to configure an automatic action that will run if a Suspicious process executed alert is triggered. The solution must minimize administrative effort.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
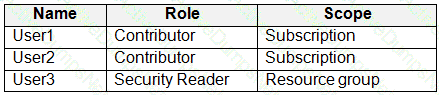
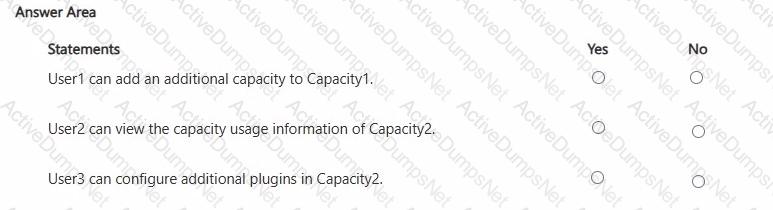
You have an Azure subscription that contains the users shown in the following table.
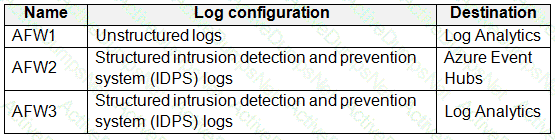
The subscription contains instances of Azure Firewall as shown in the following table.
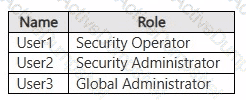
You have a Microsoft 365 E5 subscription that uses Microsoft Copilot for Security. You have the Copilot for Security role assignments shown in the following table.
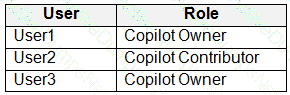
E ach user runs a Copilot for Security session.
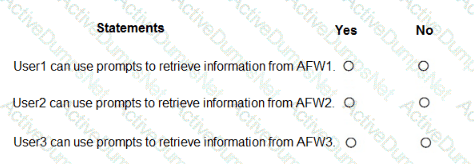
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
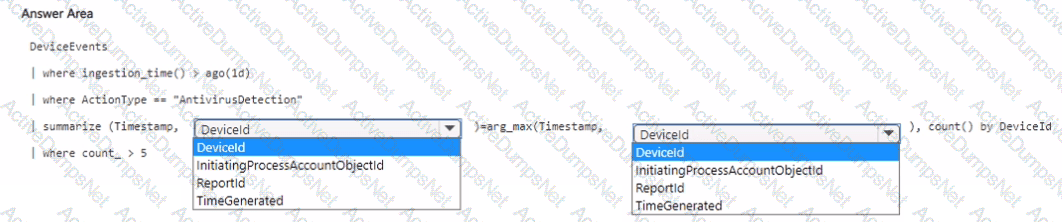
You have a Microsoft 365 subscription. You have the following KQL query.
DeviceEvents
| where ActionType == " AntivirusDetection*
You need to ensure that you can create a Microsoft Defender XDR custom detection rule by using the query.
What should you add to the query?
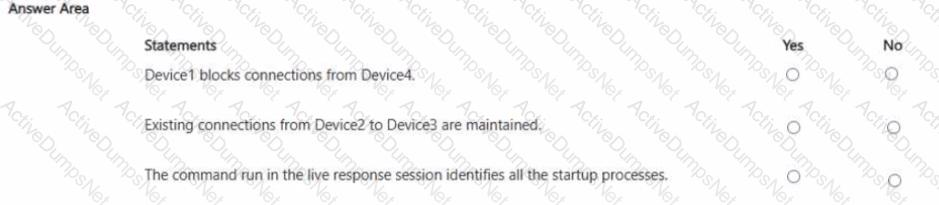
You have a Microsoft 365 subscription that uses Microsoft Defender XDR and Microsoft Defender for Endpoint. The subscription contains the devices shown in the following table.
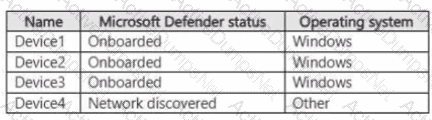
You discover the following forensic data:
• During the startup of Device1, a connection is established to Device2 via port 5555.
• Device2 connects to Device3 by using port 5555.
• Device4 connects to Device! by using port 5555.
You perform the following actions:
• Initiate a live response session on Device1 and run the processes command.
• From Devices in the Microsoft Defender portal, isolate Devicel and Device2.
For each of the following statements, select Yes if True. Otherwise select No.
NOTE: Each correct selection is worth one point.
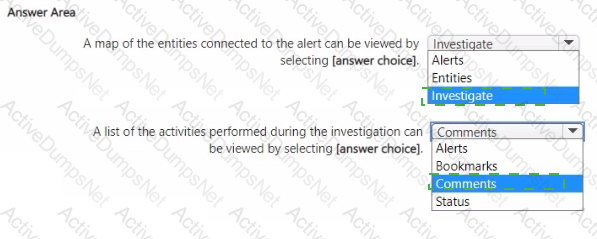
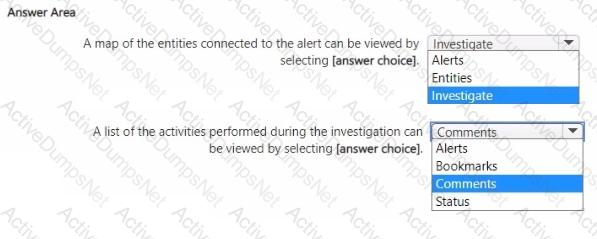
You have a Microsoft Sentinel workspace.
A Microsoft Sentinel incident is generated as shown in the following exhibit.
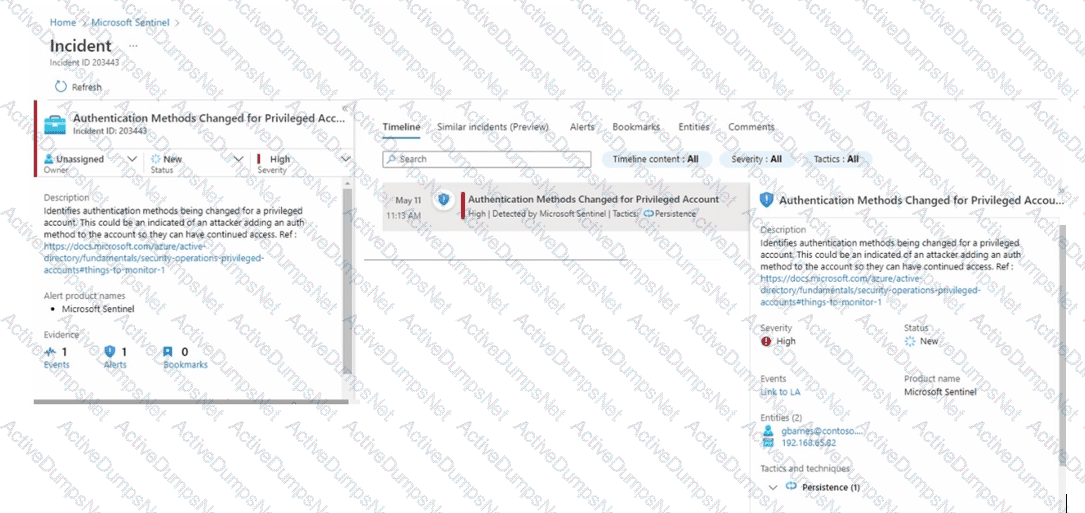
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in [the graphic.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that uses Microsoft Defender for Cloud.
You have a GitHub account named Account1 that contains 10 repositories.
You need to ensure that Defender for Cloud can assess the repositories in Account1.
What should you do first in the Microsoft Defender for Cloud portal?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have Linux virtual m achines on Amazon Web Services (AWS).
You deploy Azure Defender and enable auto-provisioning.
You need to monitor the virtual machines by using Azure Defender.
Solution: You manually install the Log Analytics agent on the virtual machines.
Does this me et the goal?
You have a Microsoft Sentinel workspace.
You receive multiple alerts for failed sign in attempts to an account.
You identify that the alerts are false positives.
You need to prevent additional failed sign-in alerts from being generated for the account. The solution must meet the following requirements.
• Ensure that failed sign-in alerts are generated for other accounts.
• Minimize administrative effort
What should do?
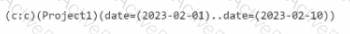
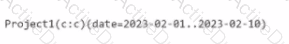
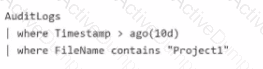
You have a Microsoft 365 subscription that uses Microsoft Purview and Microsoft Teams.
You have a team named Team1 that has a project named Project 1.
You need to identify any Project1 files that were stored on the team site of Team1 between February 1, 2023, and February 10, 2023.
Which KQL query should you run?
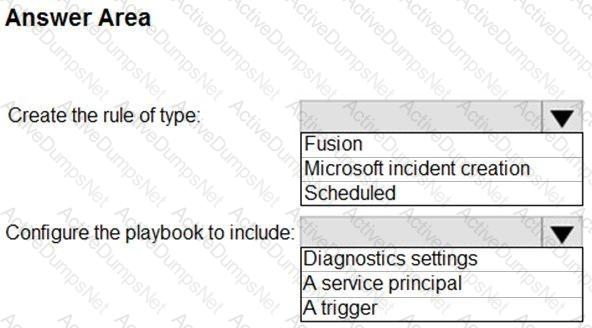
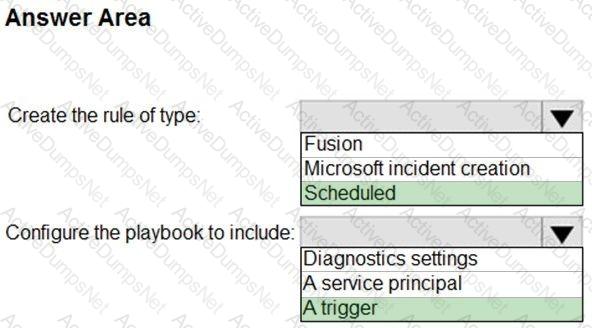
A company uses Azure Sentinel.
You need to create an automated threat response.
What should you use?
You have a Microsoft 365 subscription that uses Microsoft 365 Defender.
You need to identify all the entities affected by an incident.
Which tab should you use in the Microsoft 365 Defender portal?
You use Azure Defender.
You have an Azure Storage account that contains sensitive information.
You need to run a PowerShell script if someone accesses the storage account fr om a suspicious IP address.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
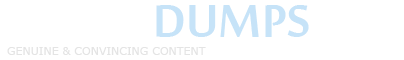
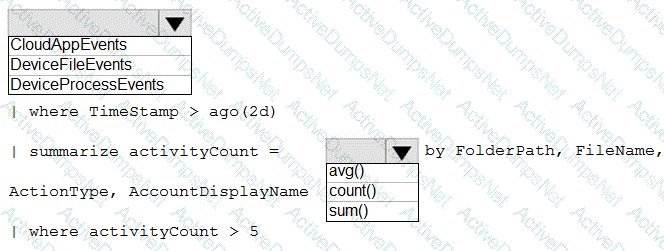
You have a Microsoft 365 subscription that uses Microsoft Defender XDR.
You need to create a custom detection rule that will identify devices that had more than five antivirus detections within the last 24 hours.
how should you complete the query? To answer, select the appropriate options in the answer area.
NOTE Each correct selection is worth one point.
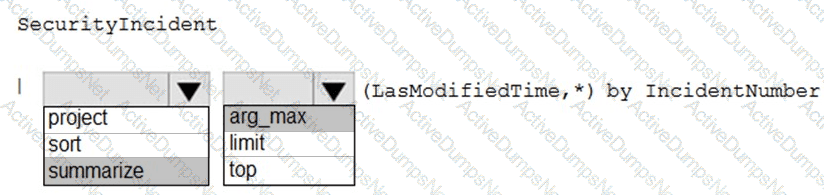
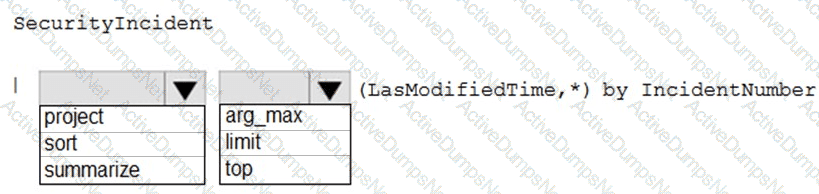
You need to create a query for a workbook. The query must meet the following requirements:
List all incidents by in cident number.
Only include the most recent log for each incident.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have the Azure subscriptions shown in the following table.
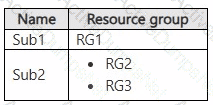
You have a Microsoft Entra tenant that contains the users shown in the following table.
The users have the Azure roles shown in the following table.
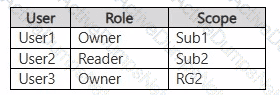
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
You have 500 on-premises Windows 11 devices that use Microsoft Defender for Endpoint
You enable Network device discovery.
You need to create a hunting query that will identify discovered network devices and return the identity of the onboarded device that discovered each network device.
Which built-in function should you use?
You need to configure event monitoring for Server1. The solution must meet the Microsoft Sentinel requirements. What should you create first?
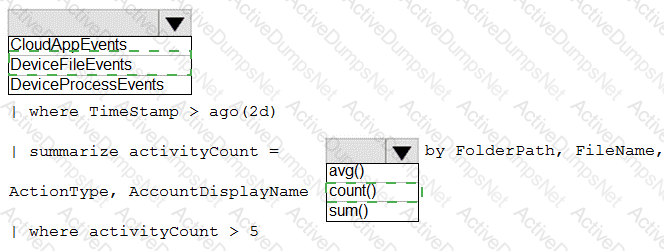
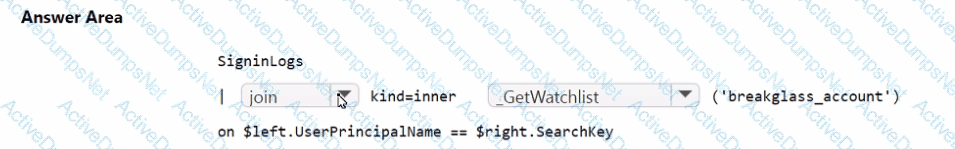
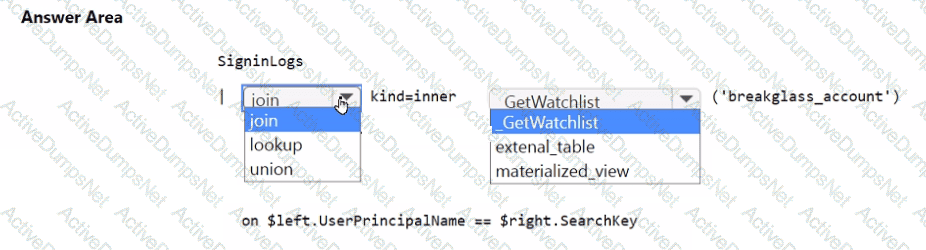
You need to implement the Microsoft Sentinel NRT rule for monitoring the designated break glass account. The solution must meet the Microsoft Sentinel requirements.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
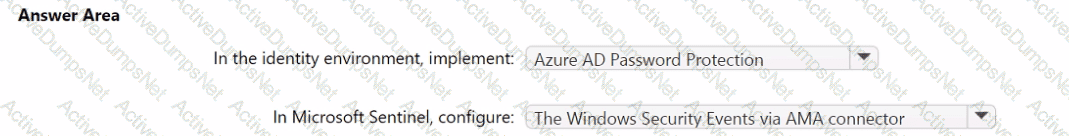
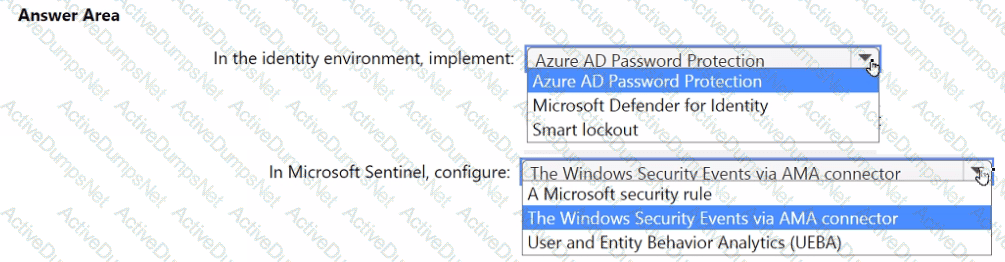
You need to monitor the password resets. The solution must meet the Microsoft Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that the configuration of HuntingQuery1 meets the Microsoft Sentinel requirements.
What should you do?
You need to implement the Defender for Cloud requirements.
What should you configure for Server2?
You need to ensure that the Group1 members can meet the Microsoft Sentinel requirements.
Which role should you assign to Group1?
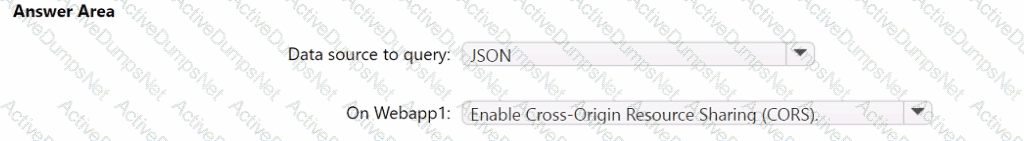
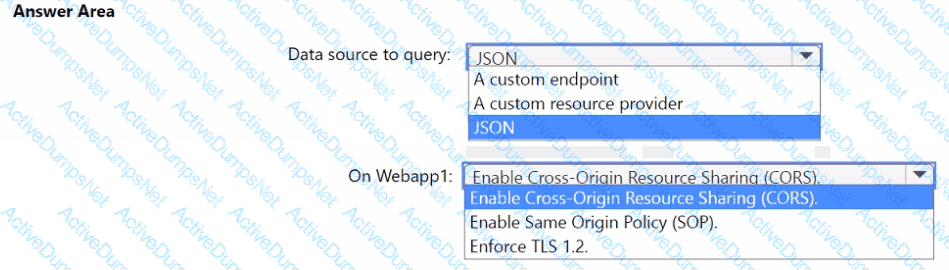
You need to implement the query for Workbook1 and Webapp1. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
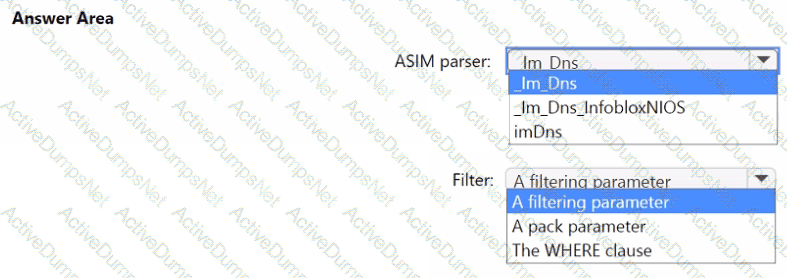
You need to implement the ASIM query for DNS requests. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to implement the Defender for Cloud requirements.
Which subscription-level role should you assign to Group1?
You need to ensure that the processing of incidents generated by rulequery1 meets the Microsoft Sentinel requirements.
What should you create first?
You need to implement the scheduled rule for incident generation based on rulequery1.
What should you configure first?
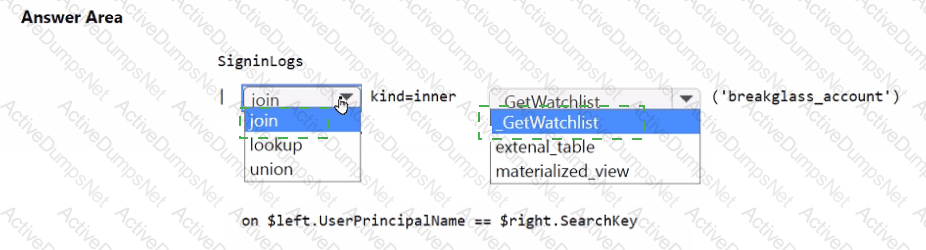
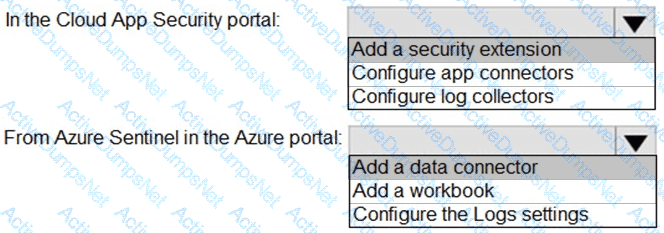
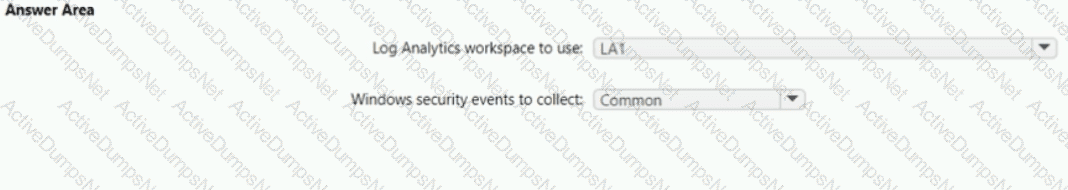
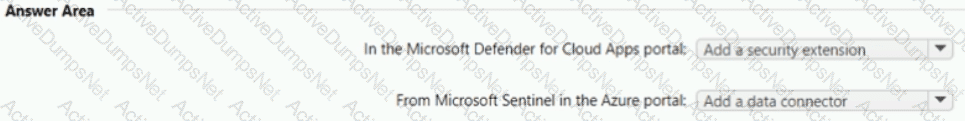
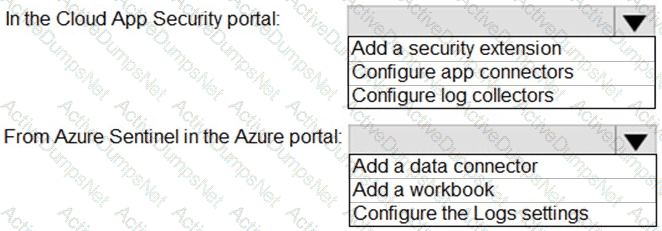
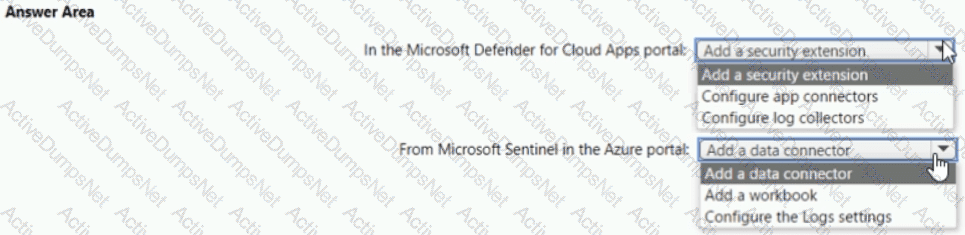
You need to configure the Azure Sentinel integration to meet the Azure Senti nel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to implement the Azure Information Protection requirements. What should you configure first?
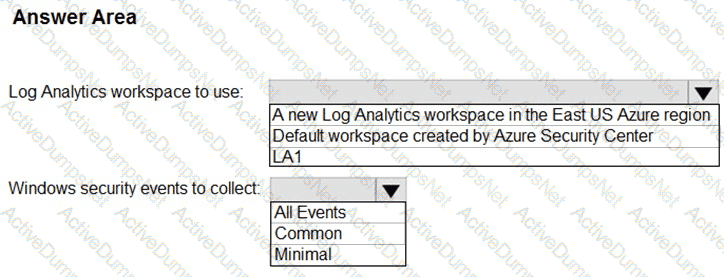
You need to implement Microsoft Defender for Cloud to meet the Microsoft Defender for Cloud requirements and the business requirements. What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Which rule setting should you configure to meet the Microsoft Sentinel requirements?
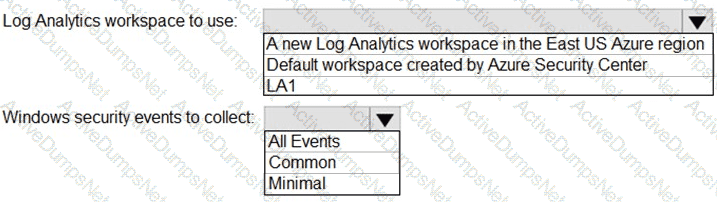
You need to implement Azure Defender to meet the Azure Defender requirements and the business requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to modify the anomaly detection policy settings to meet the Cloud App Security requirements. Which policy should you modify?
You need to create the test rule to meet the Azure Sentinel requirements. What should you do when you create the rule?
You need to restrict cloud apps running on CUENT1 to meet the Microsoft Defender for Endpoint requirements. Which two configurations should you modify? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
You need to restrict cloud apps running on CLIENT1 to meet the Microsoft Defender for Endpoint requirements.
Which two configurations should you modify? Each correct answ er present part of the solution.
NOTE: Each correct selection is worth one point.
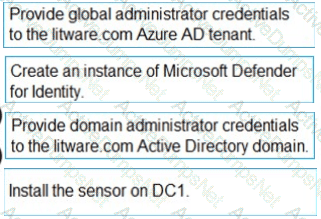
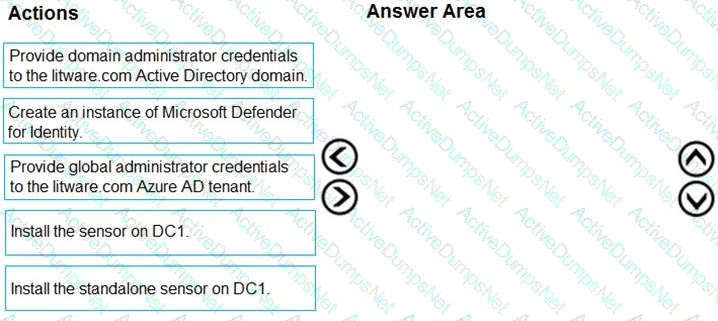
You need to configure DC1 to meet the business requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to configure the Microsoft Sentinel integration to meet the Microsoft Sentinel requirements. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
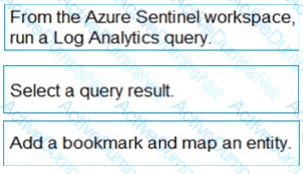
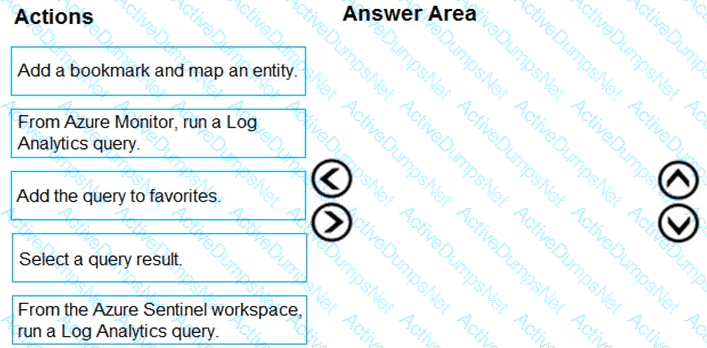
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the answer area and arrange them in the correct order.
You need to assign a role-based access control (RBAC) role to admin1 to meet the Azure Sentinel requirements and the business requirements.
Which role should you assign?
You need to modify the anomaly detection policy settings to meet the Microsoft Defender for Cloud Apps requirements and resolve the reported problem.
Which policy should you modify?