Huawei H12-711_V4.0 HCIA-Security V4.0 Exam Exam Practice Test
HCIA-Security V4.0 Exam Questions and Answers
A Web server is deployed in an enterprise intranet to provide Web access services to Internet users, and in order to protect the access security of the server, it should be divided into the _____ area of the firewall.
Which of the following attacks can be detected through intrusion prevention?
Which of the following is not the matching mode of the firewall security protection whitelist rules?
Which of the following problems cannot be solved using PKI?
Which of the following types of packets cannot be filtered by a packet filtering firewall?
Which of the following statements are correct about the status of the firewall VGMP group?
The following description of IDS, which items are correct
The IDS cannot be linked to the firewall.
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
Which type of NAT translates both addresses and port numbers and uses the public IP address of the outbound interface as the post-NAT address?
While working for a company, Tom receives an email with an attachment. Which of the following operations is correct?
What is the protocol number of the GRE protocol?
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?
Which of the following packets is controlled by a firewall's security policy by default?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
Which layer of the protocol stack does SSL provide end-to-end encrypted transmission services?
Which of the following statements is correct about security zones on a Huawei firewall?
Which of the following is not a type of Windows log event?
Which of the following is not an encryption algorithm in a VPN?
Which of the following attack methods is to construct special SQL statements and submit sensitive information to exploit program vulnerabilities
Which of the following statements are correct about firewall security zones?
Information security aims to protect data in hardware, software, and their systems on information networks to prevent data damage, tampering, or breach due to occasional or malicious reasons and ensure proper system running and non-stop information services.
Devices that need to provide network services externally, such as WWW servers and FTP servers, can be placed in the DMZ.
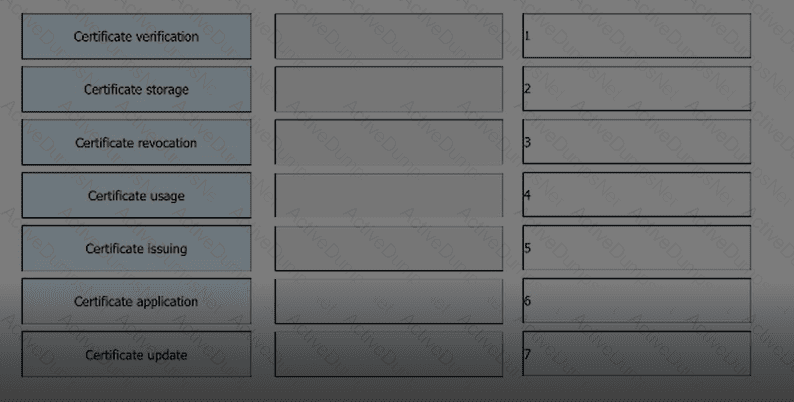
Arrange the following processes in the correct order based on the PKI lifecycle.
When using passive mode to establish an FTP connection, the control channel uses port 20 and the data channel uses port 21.
The trigger authentication method for firewall access user authentication does not include which of the following?
____- The goal is to provide a rapid, composed and effective response in emergency situations, thereby enhancing the ability of the business to recover immediately from a disruptive event.[fill in the blank]*
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution. 1. Inhibition stage, 2. recovery phase, 3. Detection stage, 4. eradication phase[fill in the blank]*
Which of the following are antivirus response actions of the firewall?
In the automatic backup mode of hot standby on the second machine, which of the following sessions is backed up?
Which of the following characteristics does a denial-of-service attack include?
What is the security level of the Untrust zone in Huawei firewalls?
Which of the following statements are correct about the PKI system structure?
Which of the following descriptions about the heartbeat interface is wrong ( )?
The keys used by the IPSec encryption and authentication algorithms can be configured manually or dynamically negotiated via the ____ protocol. (abbreviation, all uppercase).
The initial priority of the USG9500VGMP group is related to which of the following factors ( )? *
The shard cache technology will wait for the arrival of the first shard packet, and then reassemble and decrypt all the packets, and then do subsequent processing by the device to ensure that the session can proceed normally in some application scenarios.
In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
What type of ACL does ACL number 3001 correspond to?
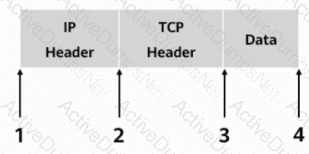
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
Social engineering is a means of harm such as deception, harm, etc. through psychological traps such as psychological weaknesses, instinctive reactions, curiosity, trust, and greed of victims ( )
Which of the following statements are incorrect about the differences between routers and Layer 2 switches?
Which of the following are the backup items that HRP can provide?
In the PKI certificate revocation process, a user needs to send a signed and encrypted email to the RA to apply for certificate revocation.
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
Which of the following is the numbering range of Layer 2 ACLs?