A newly created platform allows users to access a Linux endpoint. When users click to connect, nothing happens.
Which piece of the platform is missing?
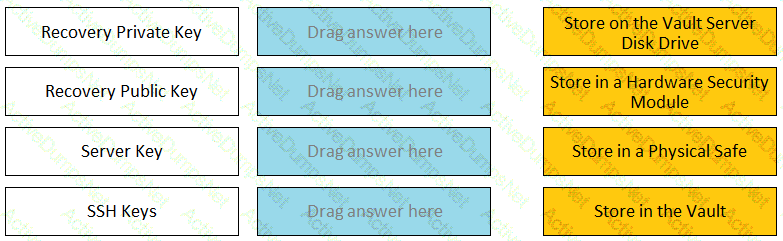
When managing SSH keys, the CPM stored the Private Key
You are creating a new Rest API user that utilizes CyberArk Authentication.
What is a correct process to provision this user?
Your customer, ACME Corp, wants to store the Safes Data in Drive D instead of Drive C.
Which file should you edit?
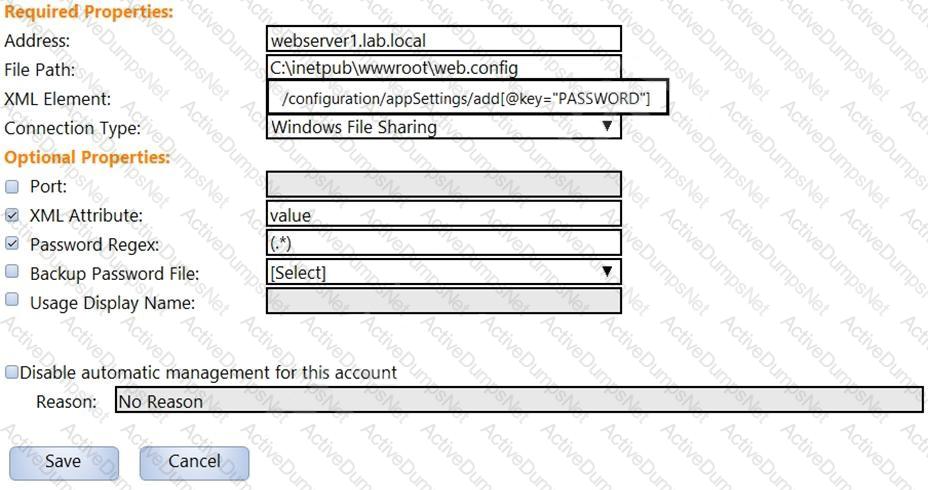
In the screenshot displayed, you just configured the usage in CyberArk and want to update its password.
What is the least intrusive way to accomplish this?
All of your Unix root passwords are stored in the safe UnixRoot. Dual control is enabled for some of the accounts in that safe. The members of the AD group UnixAdmins need to be able to use the show, copy, and connect buttons on those passwords at any time without confirmation. The members of the AD group Operations Staff need to be able to use the show, copy and connect buttons on those passwords on an emergency basis, but only with the approval of a member of Operations Managers never need to be able to use the show, copy or connect buttons themselves.
Which safe permission do you need to grant Operations Staff? Check all that apply.
How do you create a cold storage backup?
Where can you assign a Reconcile account? (Choose two.)
The vault supports Role Based Access Control.
Match each key to its recommended storage location.
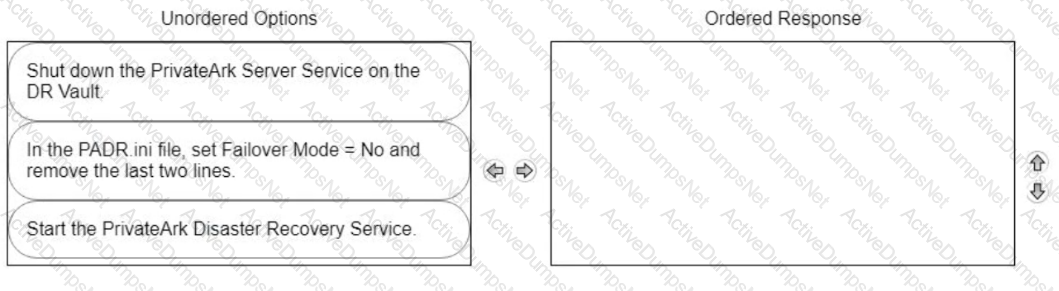
ADR Vault became active due to a failure of the primary Vault. Service on the primary Vault has now been restored. Arrange the steps to return the DR vault to its normal standby mode in the correct sequence.
Which methods can you use to add a user directly to the Vault Admin Group? (Choose three.)
Which values are acceptable in the address field of an Account?
A logon account can be specified in the platform settings.
Which permissions are needed for the Active Directory user required by the Windows Discovery process?
What does the Export Vault Data (EVD) utility do?
What is the primary purpose of Dual Control?
You are configuring CyberArk to use HTML5 gateways exclusively for PSM connections.
In the PVWA, where do you set DefaultConnectionMethod to HTML5?
CyberArk recommends implementing object level access control on all Safes.
Where can PTA be configured to send alerts? (Choose two.)
What is the purpose of the HeadStartlnterval setting m a platform?
A user is receiving the error message “ITATS006E Station is suspended for User jsmith” when attempting to sign into the Password Vault Web Access (PVWA). Which utility would a Vault administrator use to correct this problem?
Which of the following properties are mandatory when adding accounts from a file? (Choose three.)
Which service should NOT be running on the DR Vault when the primary Production Vault is up?
What is the primary purpose of One Time Passwords?
You are logging into CyberArk as the Master user to recover an orphaned safe.
Which items are required to log in as Master?
Which PTA sensors are required to detect suspected credential theft?
Which user(s) can access all passwords in the Vault?
Vault admins must manually add the auditors group to newly created safes so auditors will have sufficient access to run reports.
You want to build a connector that connects to a website through the Web applications for PSM framework.
Which default connector do you duplicate and modify?
You are concerned about the Windows Domain password changes occurring during business hours.
Which settings must be updated to ensure passwords are only rotated outside of business hours?
Match each PTA alert category with the PTA sensors that collect the data for it.

Which Cyber Are components or products can be used to discover Windows Services or Scheduled Tasks that use privileged accounts? Select all that apply.
The password upload utility must run from the CPM server
You have associated a logon account to one your UNIX cool accounts in the vault. When attempting to [b]change [/b] the root account’s password the CPM will…..
Which CyberArk utility allows you to create lists of Master Policy Settings, owners and safes for output to text files or MSSQL databases?
What is the purpose of a linked account?
A user requested access to view a password secured by dual-control and is unsure who to contact to expedite the approval process. The Vault Admin has been asked to look at the account and identify who can approve their request.
What is the correct location to identify users or groups who can approve?
CyberArk implements license limits by controlling the number and types of users that can be provisioned in the vault.
Refer to the exhibit.
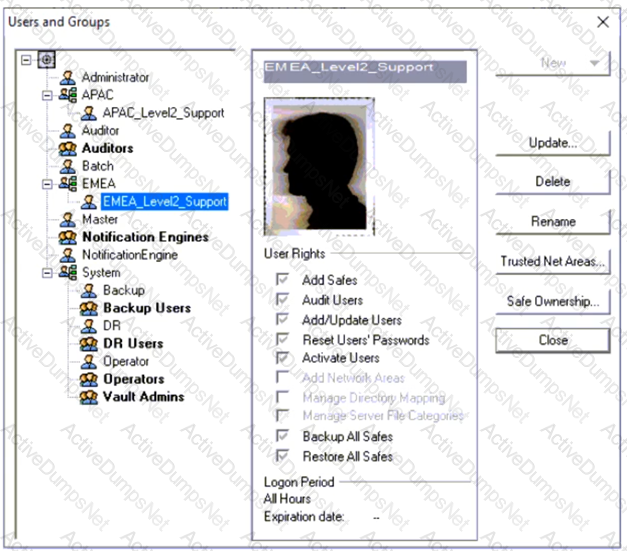
Why is user "EMEALevel2Support" unable to change the password for user "Operator"?
The Active Directory User configured for Windows Discovery needs which permission(s) or membership?
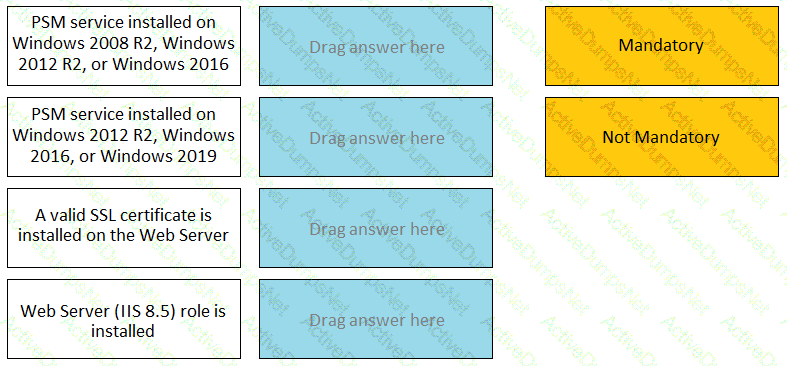
For each listed prerequisite, identify if it is mandatory or not mandatory to run the PSM Health Check.
During a High Availability node switch you notice an error and the Cluster Vault Manager Utility fails back to the original node.
Which log files should you check to investigate the cause of the issue? (Choose three.)
According to CyberArk, which issues most commonly cause installed components to display as disconnected in the System Health Dashboard? (Choose two.)
Which built-in report from the reports page in PVWA displays the number of days until a password is due to expire?
You received a notification from one of your CyberArk auditors that they are missing Vault level audit permissions. You confirmed that all auditors are missing the Audit Users Vault permission.
Where do you update this permission for all auditors?
You created a new safe and need to ensure the user group cannot see the password, but can connect through the PSM.
Which safe permissions must you grant to the group? (Choose two.)
Which master policy settings ensure non-repudiation?
To manage automated onboarding rules, a CyberArk user must be a member of which group?
A user has successfully conducted a short PSM session and logged off. However, the user cannot access the Monitoring tab to view the recordings.
What is the issue?
You are creating a Dual Control workflow for a team’s safe.
Which safe permissions must you grant to the Approvers group?
As long as you are a member of the Vault Admins group you can grant any permission on any safe.
Which is the primary purpose of exclusive accounts?
What is the chief benefit of PSM?
Which statement is correct concerning accounts that are discovered, but cannot be added to the Vault by an automated onboarding rule?
How much disk space do you need on a server to run a full replication with PAReplicate?
Which parameter controls how often the CPM looks for Soon-to-be-expired Passwords that need to be changed.
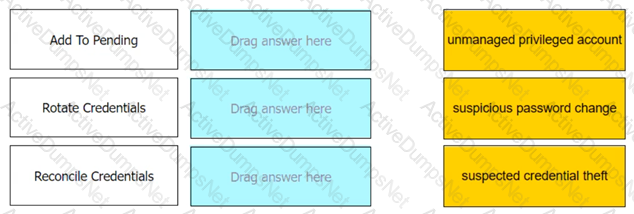
Match each automatic remediation to the correct PTA security event.
Which change could CyberArk make to the REST API that could cause existing scripts to fail?
Which CyberArk group does a user need to be part of to view recordings or live monitor sessions?
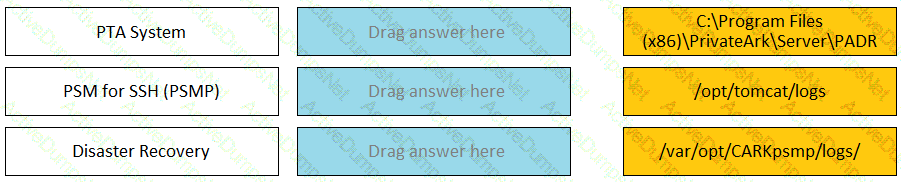
Match each component to its respective Log File location.
Select the best practice for storing the Master CD.
In order to connect to a target device through PSM, the account credentials used for the connection must be stored in the vault?
As long as you are a member of the Vault Admins group, you can grant any permission on any safe that you have access to.
If the AccountUploader Utility is used to create accounts with SSH keys, which parameter do you use to set the full or relative path of the SSH private key file that will be attached to the account?
Which processes reduce the risk of credential theft? (Choose two.)
What is the purpose of the PrivateArk Server service?
Customers who have the ‘Access Safe without confirmation’ safe permission on a safe where accounts are configured for Dual control, still need to request approval to use the account.
You have been asked to create an account group and assign three accounts which belong to a cluster. When you try to create a new group, you receive an unauthorized error; however, you are able to edit other aspects of the account properties.
Which safe permission do you need to manage account groups?
What is the purpose of the Interval setting in a CPM policy?
You are onboarding 5,000 UNIX root accounts for rotation by the CPM. You discover that the CPM is unable to log in directly with the root account and will need to use a secondary account.
How should this be configured to allow for password management using least privilege?
Which report shows the accounts that are accessible to each user?