A Linux administrator has defined a systemd script docker-repository.mount to mount a volume for use by the Docker service. The administrator wants to ensure that the Docker service does not start until the volume is mounted. Which of the following configurations needs to be added to the Docker service definition to best accomplish this task?
A systems administrator is investigating a service that is not starting up. Given the following information:
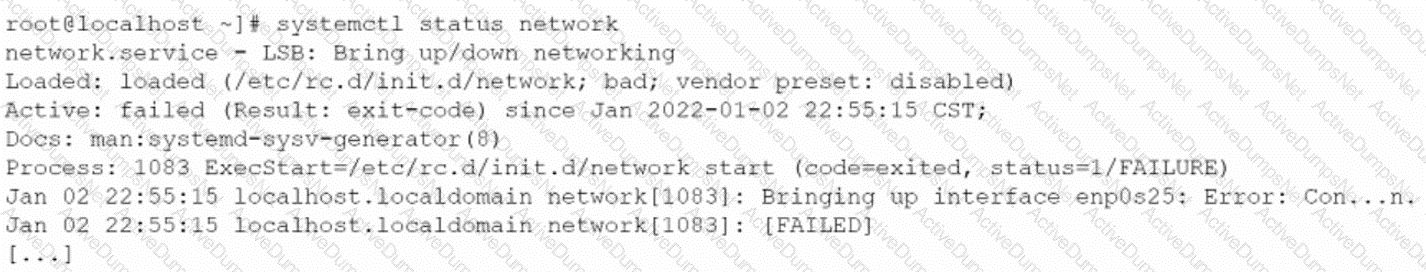
Which of the following systemd commands should the administrator use in order to obtain more details about the failing service?
A systems administrator receives reports that several virtual machines in a host are responding slower than expected. Upon further investigation, the administrator obtains the following output from one of the affected systems:
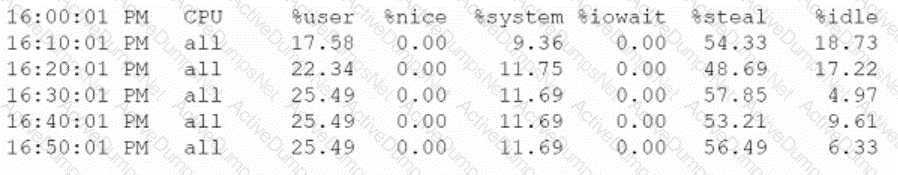
Which of the following best explains the reported issue?
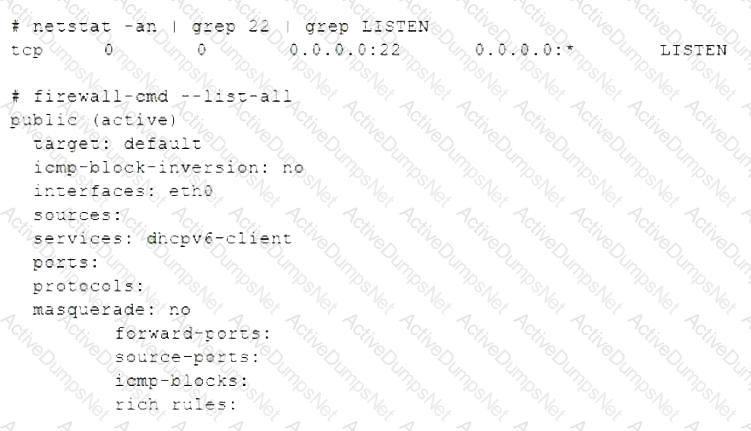
An administrator changed the default port of an SSH server to 2222 on myhost, and clients are not able to connect. The administrator runs some commands and receives the following output:
vbnet
Copy code
$ ssh -p 2222 myhost
ssh:connect to host myhost on port 2222: No route to host
Which of the following commands should be run on myhost?
A Linux systems administrator is working to obtain the installed kernel version of several hundred systems. Which of the following utilities should the administrator use for this task?
A Linux engineer is removing a previously created firewall rule. Which of the following commands will help the administrator accomplish this task?
An administrator is running a web server in a container named web, but none of the error output is not showing. Which of the following should the administrator use to generate the errors on the container?
The administrator comptia is not able to perform privileged functions on a newly deployed system. Given the following command outputs:
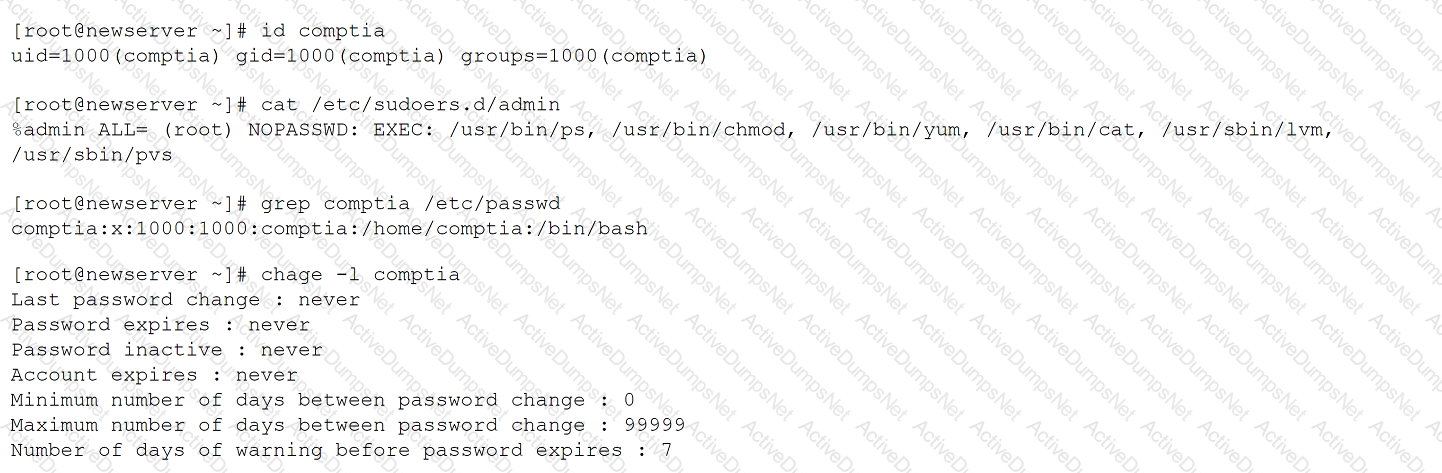
Which of the following is the reason that the administrator is unable to perform the assigned duties?
An administrator started a long-running process in the foreground that needs to continue without interruption. Which of the following keystrokes should the administrator use to continue running the process in the background?
Which of the following commands should a technician use to create an administrative account for the username Joe?
A hardened physical Linux system allows regular, unprivileged users to remotely connect to the server using SSH only. No sudo tool has been installed. Which of the following should the Linux administrator use to perform administrative tasks on this host? (Select two).
The journald entries have filled a Linux machine’s /var volume. Which of the following is the best command for a systems administrator to use to free up the disk space occupied by these entries?
An administrator is provisioning an Apache web server. When the administrator visits the server website, the browser displays a message indicating the website cannot be reached. Which of the following commands should the administrator use to verify whether the service Is running?
Which of the following directories contains binaries that only a root user should run?
Users are experiencing high latency when accessing a web application served by a Linux machine. A systems administrator checks the network interface counters and sees the following:
Which of the following is the most probable cause of the observed latency?
A Linux administrator logs in to a system and identifies that an important backup has been started. The backup process is consuming a considerable amount of CPU time but needs to continue. Which of the following should the administrator use to reduce the impact this process has on other services?
A junior systems administrator recently installed an HBA card in one of the servers that is deployed for a production environment. Which of the following
commands can the administrator use to confirm on which server the card was installed?
A systems administrator wants to list all local account names and their respective UIDs. Which of the following commands will provide output containing this information?
NO: 41:
A systems administrator needs to install the file installer_0.17-41.2_amd64.deb. Which of the following commands should the administrator use?
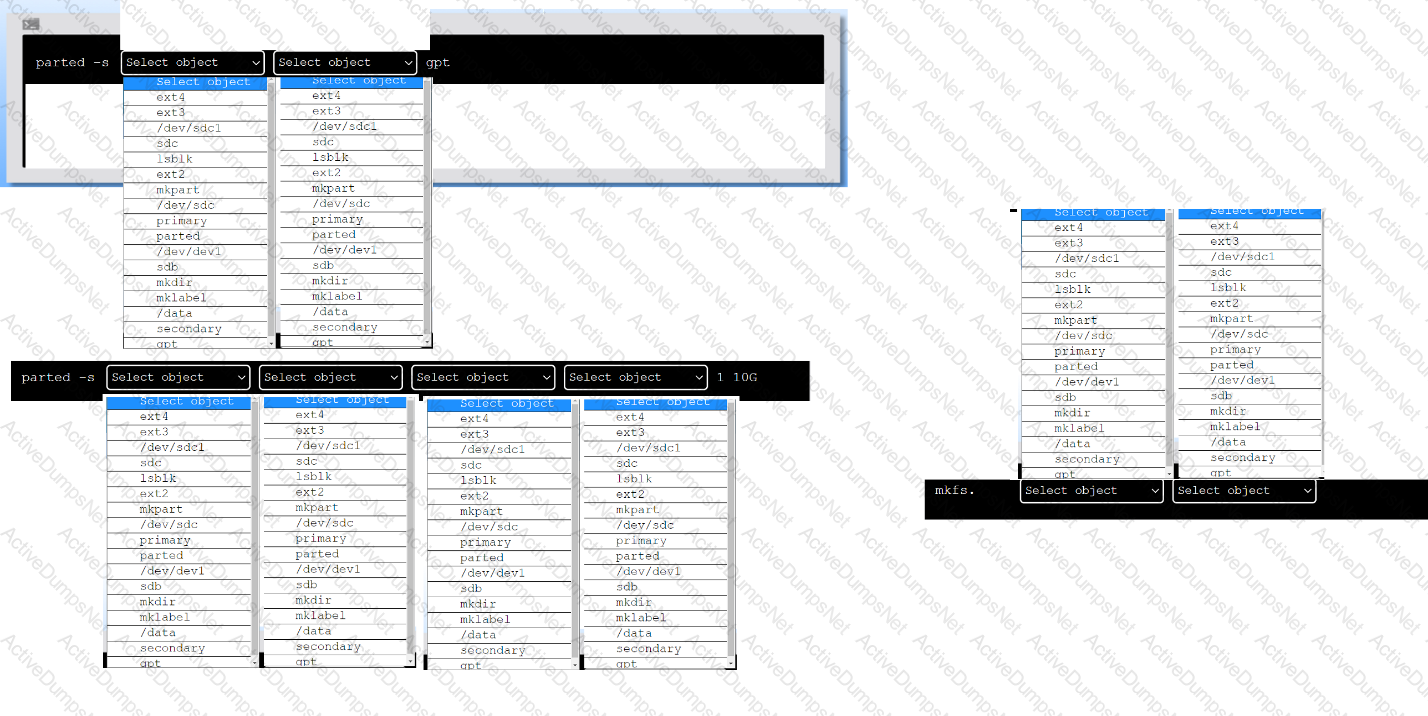
A new drive was recently added to a Linux system. Using the environment and tokens provided, complete the following tasks:
• Create an appropriate device label.
• Format and create an ext4 file system on the new partition.
The current working directory is /.
The MySQL database process that was running on a Linux server suddenly stopped, and the process was killed. Which of the following commands can help identify whether this issue was produced by the OOM killer?
An administrator is running a web server in a container named WEB, but none of the error output is showing. Which of the following should the administrator use to generate the errors on the container?
A Linux systems administrator needs to add additional code to code that resides within a repository without changing the original code. Once completed, the additional code will be merged into the main branch. Which of the following commands should the administrator use first?
A DevOps engineer is working on a local copy of a Git repository. The engineer would like to switch from the main branch to the staging branch but notices the staging branch does not exist. Which of the following Git commands should the engineer use to perform this task?
A systems administrator is receiving complaints about slow performance and system crashes. The administrator suspects memory and CPU issues. Which of the following is the first action the administrator should take to troubleshoot and resolve these issues?
A systems engineer deploys a new application server, but the server cannot communicate with the back-end database hostname. The engineer confirms that the application server can ping the database server's IP address. Which of the following is the most likely cause of the issue?
A systems administrator is configuring a Linux system so that network traffic from the internal network 172.17.0.0/16 going out through the eth0 interface would appear as if it was sent directly from this interface. Which of the following commands will accomplish this task?
A Linux administrator has defined a systemd script docker-repository.mount to mount a volume for use by the Docker service. The administrator wants to ensure that Docker
service does not start until the volume is mounted. Which of the following configurations needs to be added to the Docker service definition to best accomplish this task?
An administrator is investigating why a Linux workstation is not resolving a website. The output of dig and nslookup shows that IPv4 resolution is working, but IPv6 resolution fails.
The administrator executes:
nslookup -querytype=AAAA www.comptia.org
Can't find www.comptia.org: No answer
The workstation has a static entry in /etc/hosts:
CopyEdit
104.18.99.101 www.comptia.org
Which of the following is the most likely cause?
A Linux administrator wants to prevent the httpd web service from being started both manually and automatically on a server. Which of the following should the administrator use to accomplish this task?
A Linux administrator is troubleshooting an SSHD issue on a server. Users are receiving error messages stating the connection is refused. Which of the following commands should be used to verify whether the service is listening?
NO: 60:
A Linux administrator is creating a directory called CompTIA_doc, and it needs to switch to another location to perform some system-related tasks. Which of the following commands should the administrator use for this task?
A systems administrator created a new directory with specific permissions. Given the following output:
# file: comptia
# owner: root
# group: root
user: : rwx
group :: r-x
other: :---
default:user :: rwx
default:group :: r-x
default:group:wheel: rwx
default:mask :: rwx
default:other ::-
Which of the following permissions are enforced on /comptia?
An administrator would like to list all current containers, regardless of their running state. Which of the following commands would allow the administrator to accomplish this task?
Application code is stored in Git. Due to security concerns, the DevOps engineer does not want to keep a sensitive configuration file, app . conf, in the
repository. Which of the following should the engineer do to prevent the file from being uploaded to the repository?
An administrator needs to increase the system priority of a process with PID 2274. Which of the following commands should the administrator use to
accomplish this task?
A Linux engineer needs to get information from the foo.com domain mail servers. Which of the following network tools should the engineer use?
A Linux administrator encounters the following error in the Apache log files:
css
SQLSTATE[HY000] [2002] Permission denied
Which of the following commands should the administrator run to safely fix this issue?
While troubleshooting server issues, a Linux systems administrator obtains the following output:
yaml
total used free shared buff/cache available
Mem: 3736 3538 33 2 48 25
Swap: 2047 1824 223
Which of the following best describes the state of the system?
An operations engineer is planning to start a container running a PostgreSQL database. The engineer wants the container to start automatically at system startup, mount the /home/db directory as /var/lib/postgresql inside the container, and expose port 5432 to the OS. Which of the following commands should the engineer run to achieve this task?
A development team asks an engineer to guarantee the persistency of journal log files across system reboots. Which of the following commands would accomplish this task?
Users have been unable to save documents to /home/tmp/temp and have been receiving the following error:
Path not found
A junior technician checks the locations and sees that /home/tmp/tempa was accidentally created instead of /home/tmp/temp. Which of the following commands should the technician use to fix this issue?
A Linux user reported the following error after trying to connect to the system remotely:
ssh: connect to host 10.0.1.10 port 22: Resource temporarily unavailable
The Linux systems administrator executed the following commands in the Linux system while trying to diagnose this issue:
Which of the following commands will resolve this issue?
A Linux systems administrator receives a notification that one of the server’s filesystems is full. Which of the following commands would help the administrator to identify this filesystem?
A Linux administrator modified the SSH configuration file. Which of the following commands should be used to apply the configuration changes?
Which of the following commands is used to configure the default permissions for new files?
A Linux engineer receives reports that files created within a certain group are being modified by users who are not group members. The engineer wants to reconfigure the server so that only file owners and group members can modify new files by default. Which of the following commands would accomplish this task?
Using AD Query, the security gateway connections to the Active Directory Domain Controllers using what protocol?
A systems administrator wants to check for running containers. Which of the following commands can be used to show this information?
A Linux administrator has physically added a new RAID adapter to a system. Which of the following commands should the Linux administrator run to confirm that the device has been recognized? (Select TWO).
A Linux system is failing to boot. The following error is displayed in the serial console:
[[1;33mDEPEND[Om] Dependency failed for /data.
[[1;33mDEPEND[Om] Dependency failed for Local File Systems
...
Welcome to emergency mode! After logging in, type "journalctl -xb" to viewsystem logs, "systemct1 reboot" to reboot, "systemct1 default" to try again to boot into default mode.
Give root password for maintenance
(or type Control-D to continue}
Which of the following files will need to be modified for this server to be able to boot again?
A Linux systems administrator is configuring a new filesystem that needs the capability to be mounted persistently across reboots. Which of the following commands will accomplish this task? (Choose two.)
A systems administrator is tasked with mounting a USB drive on a system. The USB drive has a single partition, and it has been mapped by the system to the device /dev/sdb. Which of the following commands will mount the USB to /media/usb?
One leg of an LVM-mirrored volume failed due to the underlying physical volume, and a systems administrator is troubleshooting the issue. The following output has been provided:
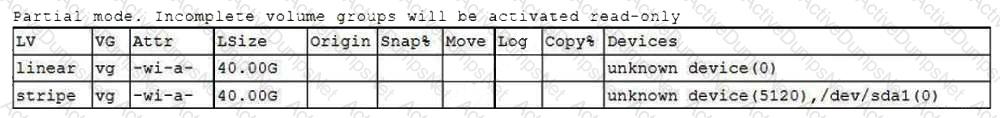
Given this scenario, which of the following should the administrator do to recover this volume?
A systems administrator created a new Docker image called test. After building the image, the administrator forgot to version the release. Which of the following will allow the administrator to assign the v1 version to the image?
A systems administrator is notified that the mysqld process stopped unexpectedly. The systems administrator issues the following command:
sudo grep –i -r ‘out of memory’ /var/log
The output of the command shows the following:
kernel: Out of memory: Kill process 9112 (mysqld) score 511 or sacrifice child.
Which of the following commands should the systems administrator execute NEXT to troubleshoot this issue? (Select two).
A systems administrator pressed Ctrl+Z after starting a program using the command line, and the shell prompt was presented. In order to go back to the program, which of the following commands can the administrator use?
A systems administrator is installing various software packages using a pack-age manager. Which of the following commands would the administrator use on the Linux server to install the package?
A systems administrator has been unable to terminate a process. Which of the following should the administrator use to forcibly stop the process?
A systems administrator is tasked with setting up key-based SSH authentication. In which of the following locations should the administrator place the public keys for the server?
A Linux administrator copied a Git repository locally, created a feature branch, and committed some changes to the feature branch. Which of the following Git actions should the Linux administrator use to publish the changes to the main branch of the remote repository?
A Linux engineer needs to download a ZIP file and wants to set the nice of value to -10 for this new process. Which of the following commands will help to accomplish the task?
A junior developer is unable to access an application server and receives the following output:
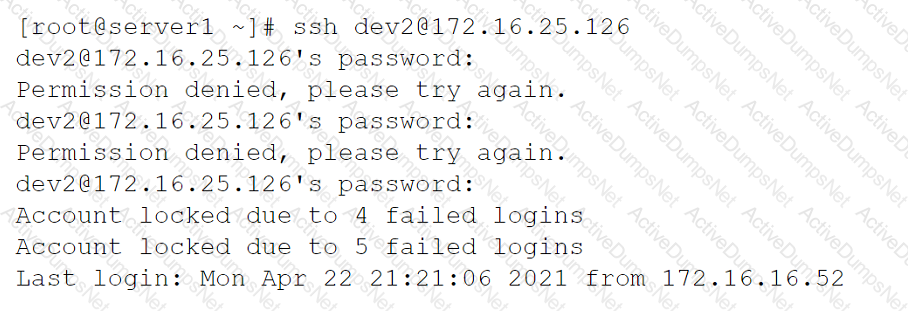
The systems administrator investigates the issue and receives the following output:
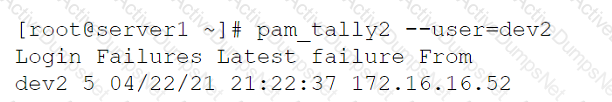
Which of the following commands will help unlock the account?
Which of the following tools is BEST suited to orchestrate a large number of containers across many different servers?
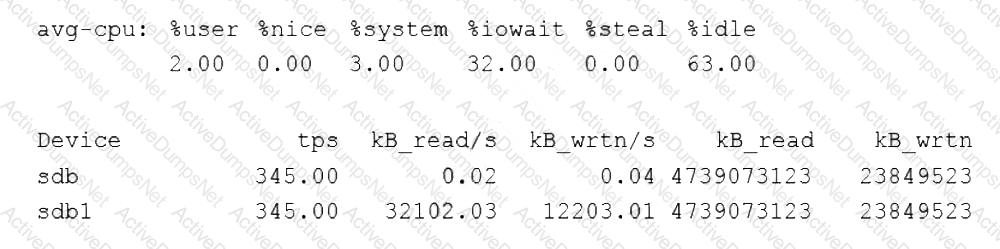
A Linux administrator was notified that a virtual server has an I/O bottleneck. The Linux administrator analyzes the following output:
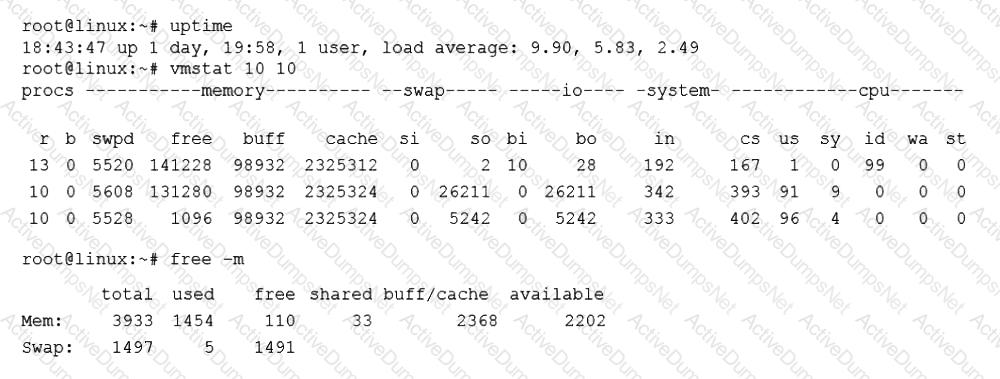
Given there is a single CPU in the sever, which of the following is causing the slowness?
A Linux administrator is providing a new Nginx image from the registry to local cache. Which of the following commands would allow this to happen?
A systems administrator received a notification that a system is performing slowly. When running the top command, the systems administrator can see the following values:
Which of the following commands will the administrator most likely run NEXT?
A systems administrator is tasked with creating an Ansible playbook to automate the installation of patches on several Linux systems. In which of the following languages should the playbook be written?
During a security scan, the password of an SSH key file appeared to be too weak and was cracked. Which of the following commands would allow a user to choose a stronger password and set it on the existing SSH key file?
A systems administrator needs to verify whether the built container has the app.go file in its root directory. Which of the following can the administrator use to verify the root directory has this file?
User1 is a member of the accounting group. Members of this group need to be able to execute but not make changes to a script maintained by User2. The script should not be accessible to other users or groups. Which of the following will give proper access to the script?
A Linux administrator rebooted a server. Users then reported some of their files were missing. After doing some troubleshooting, the administrator found one of the filesystems was missing. The filesystem was not listed in /etc/f stab and might have been mounted manually by someone prior to reboot. Which of the following would prevent this issue from reoccurring in the future?
Which of the following directories is the mount point in a UEFI system?
A Linux administrator needs to determine whether a hostname is in the DNS. Which of the following would supply the information that is needed?
A senior Linux administrator has created several scripts that will be used to install common system applications. These scripts are published to a reposito-ry to share with the systems team. A junior Linux administrator needs to re-trieve the scripts and make them available on a local workstation. Which of the following Git commands should the junior Linux administrator use to accom-plish this task?
A Linux systems administrator needs to copy files and directories from Server A to Server B. Which of the following commands can be used for this purpose? (Select TWO)
What is the main objective when using Application Control?
A Linux administrator needs to connect securely to a remote server in order to install application software. Which of the following commands would allow this connection?
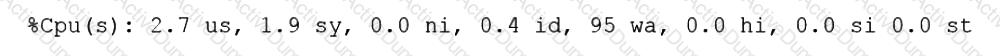
A Linux systems administrator is troubleshooting an I/O latency on a single CPU server. The administrator runs a top command and receives the following output:
%Cpu(s): 0.2 us, 33.1 sy, 0.0 ni, 0.0 id, 52.4 wa, 0.0 hi, 0.2 si, 0.0 st
Which of the following is correct based on the output received from the exe-cuted command?
A systems administrator is receiving tickets from users who cannot reach the application app that should be listening on port 9443/tcp on a Linux server.
To troubleshoot the issue, the systems administrator runs netstat and receives the following output:
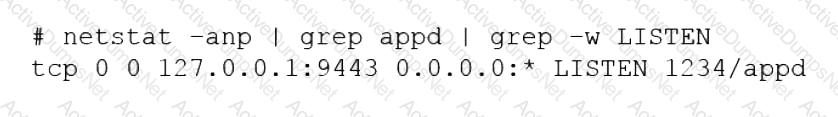
Based on the information above, which of the following is causing the issue?
A systems administrator is checking the system logs. The administrator wants to look at the last 20 lines of a log. Which of the following will execute the command?
A Linux system fails to start and delivers the following error message:
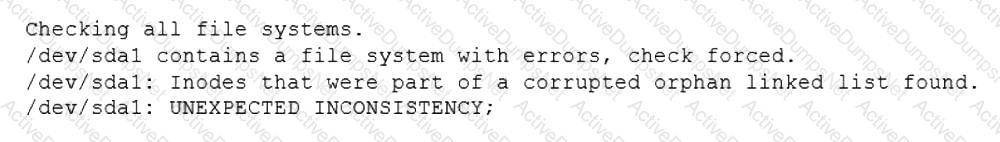
Which of the following commands can be used to address this issue?
A Linux systems administrator needs to persistently enable IPv4 forwarding in one of the Linux systems. Which of the following commands can be used together to accomplish this task? (Choose two.)
Several users reported that they were unable to write data to the /oracle1 directory. The following output has been provided:
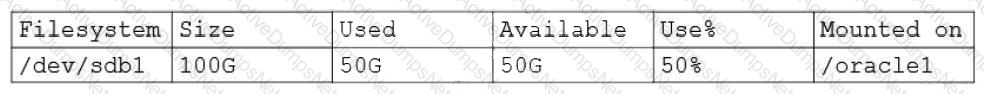
Which of the following commands should the administrator use to diagnose the issue?
An administrator attempts to rename a file on a server but receives the following error.
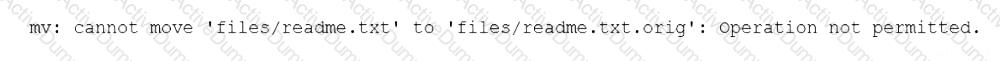
The administrator then runs a few commands and obtains the following output:
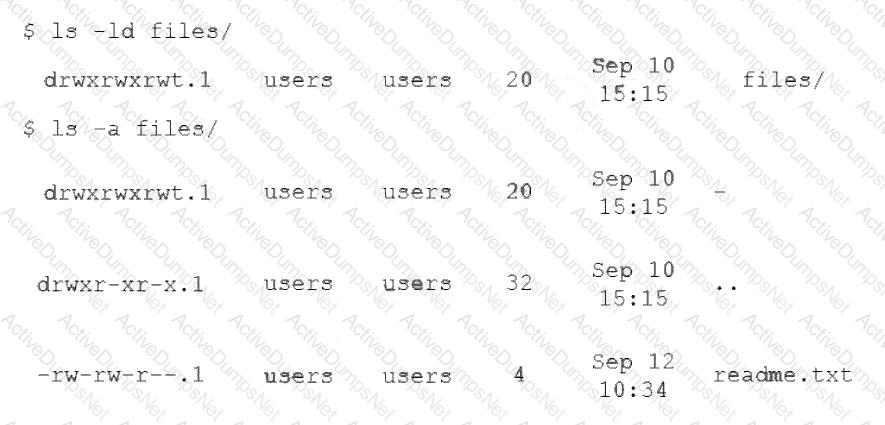
Which of the following commands should the administrator run NEXT to allow the file to be renamed by any user?
An administrator installed an application from source into /opt/operations1/ and has received numerous reports that users are not able to access the application without having to use the full path /opt/operations1/bin/*. Which of the following commands should be used to resolve this issue?
A systems administrator made some changes in the ~/.bashrc file and added an alias command. When the administrator tried to use the alias command, it did not work. Which of the following should be executed FIRST?
Which of the following is a function of a bootloader?
Which of the following files holds the system configuration for journal when running systemd?
A systems administrator made some unapproved changes prior to leaving the company. The newly hired administrator has been tasked with revealing the system to a compliant state. Which of the following commands will list and remove the correspondent packages?
A Linux engineer has been notified about the possible deletion of logs from the file /opt/app/logs. The engineer needs to ensure the log file can only be written into without removing previous entries.
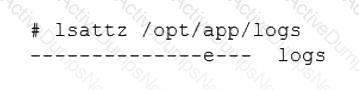
Which of the following commands would be BEST to use to accomplish this task?
A Linux administrator created the directory /project/access2all. By creating this directory, the administrator is trying to avoid the deletion or modification of files from non-owners. Which of the following will accomplish this goal?
A Linux administrator cloned an existing Linux server and built a new server from that clone. The administrator encountered the following error after booting the cloned server:
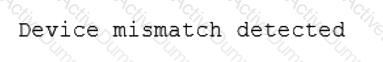
The administrator performed the commands listed below to further troubleshoot and mount the missing filesystem:
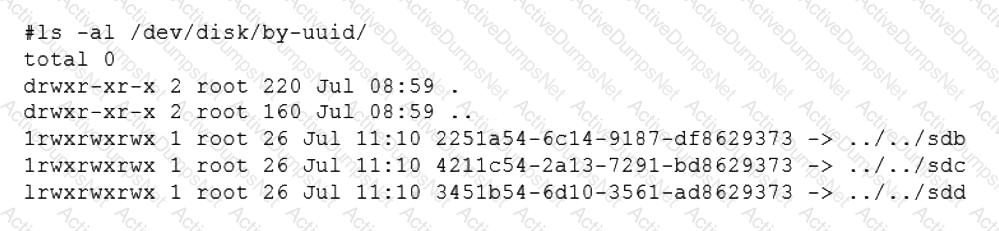
Which of the following should administrator use to resolve the device mismatch issue and mount the disk?
A systems administrator is tasked with preventing logins from accounts other than root, while the file /etc/nologin exists. Which of the following PAM modules will accomplish this task?
A Linux engineer set up two local DNS servers (10.10.10.10 and 10.10.10.20) and was testing email connectivity to the local mail server using the mail command on a local machine when the following error appeared:
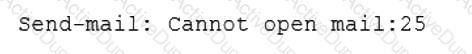
The local machine DNS settings are:
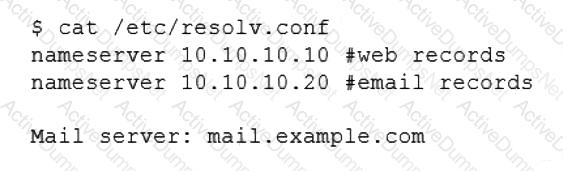
Which of the following commands could the engineer use to query the DNS server to get mail server information?
A Linux administrator needs to redirect all HTTP traffic temporarily to the new proxy server 192.0.2.25 on port 3128. Which of the following commands will accomplish this task?
A systems administrator requires that all files that are created by the user named web have read-only permissions by the owner. Which of the following commands will satisfy this requirement?
A systems administrator wants to be sure the sudo rules just added to /etc/sudoers are valid. Which of the following commands can be used for this task?
A systems administrator wants to test the route between IP address 10.0.2.15 and IP address 192.168.1.40. Which of the following commands will accomplish this task?
A junior administrator is setting up a new Linux server that is intended to be used as a router at a remote site. Which of the following parameters will accomplish this goal?
Which of the following tools is commonly used for creating CI/CD pipelines?
A Linux administrator needs to remove software from the server. Which of the following RPM options should be used?
A Linux administrator recently downloaded a software package that is currently in a compressed file. Which of the following commands will extract the files?
An administrator is trying to diagnose a performance issue and is reviewing the following output:
System Properties:
CPU: 4 vCPU
Memory: 40GB
Disk maximum IOPS: 690
Disk maximum throughput: 44Mbps | 44000Kbps
Based on the above output, which of the following BEST describes the root cause?
To harden one of the servers, an administrator needs to remove the possibility of remote administrative login via the SSH service. Which of the following should the administrator do?
A systems administrator needs to clone the partition /dev/sdc1 to /dev/sdd1. Which of the following commands will accomplish this task?
A Linux administrator is creating a primary partition on the replacement hard drive for an application server. Which of the following commands should the administrator issue to verify the device name of this partition?
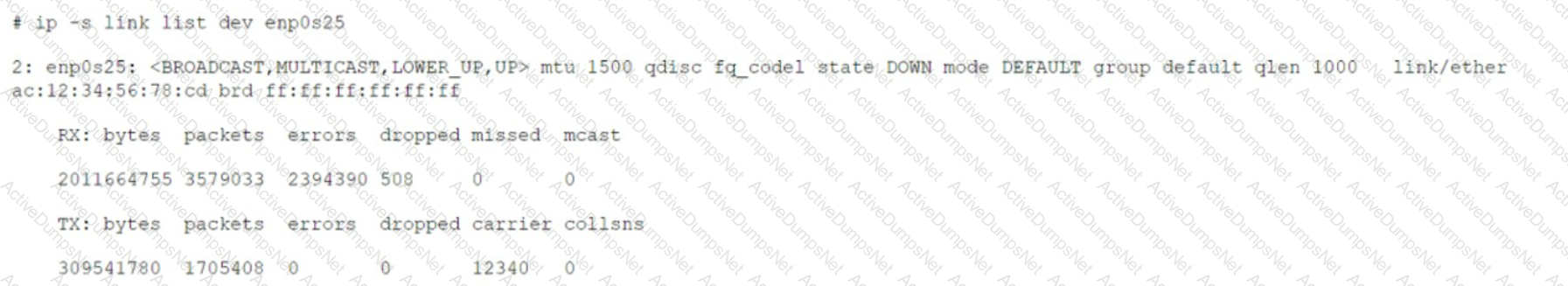
A systems administrator is troubleshooting connectivity issues and trying to find out why a Linux server is not able to reach other servers on the same subnet it is connected to. When listing link parameters, the following is presented:
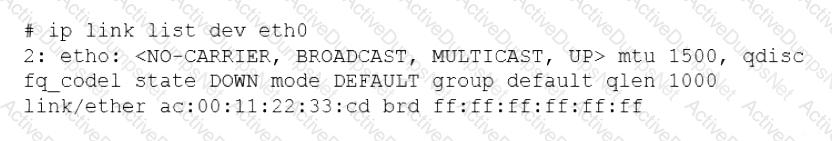
Based on the output above, which of following is the MOST probable cause of the issue?
A Linux administrator wants to find out whether files from the wget package have been altered since they were installed. Which of the following commands will provide the correct information?
A Linux system is getting an error indicating the root filesystem is full. Which of the following commands should be used by the systems administrator to resolve this issue? (Choose three.)
A junior Linux administrator is tasked with installing an application. The installation guide states the application should only be installed in a run level 5 environment.
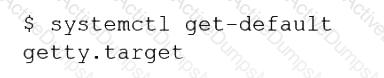
Which of the following commands would ensure the server is set to runlevel 5?
A Linux administrator is troubleshooting an issue in which an application service failed to start on a Linux server. The administrator runs a few commands and gets the following outputs:
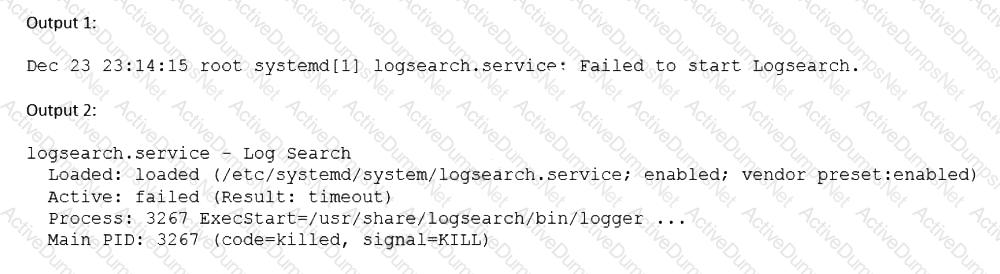
Based on the above outputs, which of the following is the MOST likely action the administrator should take to resolve this issue?
A Linux administrator was asked to run a container with the httpd server inside. This container should be exposed at port 443 of a Linux host machine while it internally listens on port 8443. Which of the following commands will accomplish this task?
A junior systems administrator has just generated public and private authentication keys for passwordless login. Which of the following files will be moved to the remote servers?
A user is asking the systems administrator for assistance with writing a script to verify whether a file exists. Given the following:
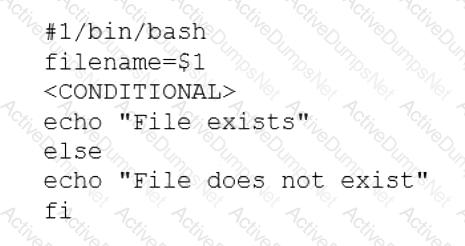
Which of the following commands should replace the
A Linux administrator wants to set the SUID of a file named dev_team.text with 744 access rights. Which of the following commands will achieve this goal?
A systems engineer is adding a new 1GB XFS filesystem that should be temporarily mounted under /ops/app. Which of the following is the correct list of commands to achieve this goal?
A cloud engineer is asked to copy the file deployment.yaml from a container to the host where the container is running. Which of the following commands can accomplish this task?
A Linux administrator needs to analyze a failing application that is running inside a container. Which of the following commands allows the Linux administrator to enter the running container and analyze the logs that are stored inside?
A systems administrator needs to check if the service systemd-resolved.service is running without any errors. Which of the following commands will show this information?