An administrator discovers a Bash script file has the following permissions set in octal notation;
777
Which of the following is the MOST appropriate command to ensure only the root user can modify and execute the script?
Which of the following concepts refers to prioritizing a connection that had previously worked successfully?
A server administrator is building a pair of new storage servers. The servers will replicate; therefore, no redundancy is required, but usable capacity
must be maximized. Which of the following RAID levels should the server administrator implement?
Which of the following script types uses commands That start with sec-?
A security analyst completed a port scan of the corporate production-server network. Results of the scan were then provided to a systems administrator for immediate action. The following table represents the requested changes:
The systems administrator created local firewall rules to block the ports indicated above. Immediately, the service desk began receiving calls about the internet being down. The systems administrator then reversed the changes, and the internet became available again. Which of the following ports on DNSSrv must remain open when the firewall rules are reapplied?
Which of the following concepts is in use when dual power supplies are connected to different power sources?
A technician has moved a data drive from a new Windows server to an orderWindows server. The hardware recognizes the drive, but the data is not visible to the OS. Which of the following is the MOST Likely cause of the issue?
A systems administrator is attempting to install a package on a server. After downloading the package from the internet and trying to launch it, the installation is blocked by the antivirus on the server. Which of the following must be completed before launching the installation package again?
A server administrator receives the following output when trying to ping a local host:
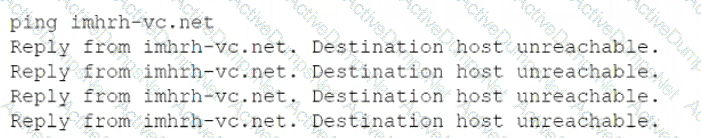
Which of the following is MOST likely the issue?
A server administrator just installed a new physical server and needs to harden the applications on the server. Which of the following best describes a method of application hardening?
A technician is configuring a point-to-point heartbeat connection between two servers using IP addressing. Which of the following is the most efficient
subnet mask for this connection?
A security administrator ran a port scanning tool against a virtual server that is hosting a secure website. A list of open ports was provided as documentation. The management team has requested that non-essential ports be disabled on the firewall. Which of the following ports must remain open?
A server administrator made a change in a server's BIOS in an attempt to fix an issue with the OS not turning on. However, the change did not successfully correct the issue. Which of the following should the server administrator do NEXT?
A technician is able to copy a Me to a temporary folder on another partition but is unable to copy it to a network share or a USB flash drive. Which of the following is MOST likely preventing the file from being copied to certain locations?
A company is implementing a check-in desk to heighten physical security. Which of the following access controls would be the most appropriate to facilitate this implementation?
An application needs 10GB of RAID 1 for log files, 20GB of RAID 5 for data files, and 20GB of RAID 5 for the operating system. All disks will be 10GB in capacity. Which of the following is the MINIMUM number of disks needed for this application?
Which of the following backup types copies changed data from a server and then combines the backups on the backup target?
A company's servers are all displaying the wrong time. The server administrator confirms the time source is correct. Which of the following is MOST likely preventing the servers from obtaining the correct time?
Which of the following BEST describes overprovisioning in a virtual server environment?
Users report they ate unable to access an application after a recent third-party patch update. The physical server that is hosting the application keeps crashing on reboot. Although the update was installed directly from the manufacturer's support website as recommended it has now been recalled and removed from the website as the update unintentionally installed unauthorized software after a reboot. Which of the following steps should the administrator perform to restore access to the application while minimizing downtime? (Select TWO)
A technician is troubleshooting a server issue. The technician has determined several possible causes of the issue and has identified various solutions. Which of the following should the technician do next?
An administrator has been asked to increase the storage capacity of a stand-alone file server but no further expansion slots are available. Whichof the following would be the FASTEST solution to implement with no downtime?
Which of the following cloud models is BEST described as running workloads on resources that are owned by the company and hosted in a company-owned data center, as well as on rented servers in another company's data center?
Which of the following asset management documents is used to identify the location of a serves within a data center?
A backup application is copying only changed files each time it runs. During a restore, however, only a single file is used. Which of the following backup methods does this describe?
A junior administrator needs to configure a single RAID 5 volume out of four 200GB drives attached to the server using the maximum possible capacity. Upon completion, the server reports that all drives were used, and the approximate volume size is 400GB. Which of the following BEST describes the result of this configuration?
Which of the following licensing models was created by software companies in response to the increasing density of processors?
Users are able to connect to the wireless network, but they are unable to access the internet. The network administrator verifies connectivity to all network devices, and there are no ISP outages. The server administrator removes the old address leases from the active leases pool, which allows users to access the internet. Which of the following is most likely causing the internet issue?
A new application server has been configured in the cloud to provide access to all clients within the network. On-site users are able to access all resources, but remote users are reporting issues connecting to the new application. The server administrator verifies that all users are configured with the appropriate group memberships. Which of the following is MOST likely causing the issue?
An administrate is helping to replicate a large amount of data between two Windows servers. The administrator is unsure how much data has already been transferred. Which of the following will BEST ensure all the data is copied consistently?
An administrator is troubleshooting a failed NIC in an application server. The server uses DHCP to get all IP configurations, and the server must use a
specific IP address. The administrator replaces the NIC, but then the server begins to receive a different and incorrect IP address. Which of the following will enable the server to get the proper IP address?
The network's IDS is giving multiple alerts that unauthorized traffic from a critical application server is being sent to a known-bad public IP address.
One of the alerts contains the following information:
Exploit Alert
Attempted User Privilege Gain
2/2/07-3: 09:09 10.1.200.32
--> 208.206.12.9:80
This server application is part of a cluster in which two other servers are also servicing clients. The server administrator has verified the other servers are not sending out traffic to that public IP address. The IP address subnet of the application servers is 10.1.200.0/26. Which of the following should the administrator perform to ensure only authorized traffic is being sent from the application server and downtime is minimized? (Select two).
A technician is attempting to log in to a Linux server as root but cannot remember the administrator password. Which of the following is the LEAST destructive method of resetting the administrator password?
A server administrator is implementing an authentication policy that will require users to use a token during login. Which of the following types of authentication is the administrator implementing?
An organization stores backup tapes of its servers at cold sites. The organization wants to ensure the tapes are properly maintained and usable during a DR scenario. Which of the following actions should the organization perform?
An administrator gave Ann modify permissions to a shared folder called DATA, which is located on the company server. Other users need read access to the files in this folder. The current configuration is as follows:
The administrator has determined Ann cannot write anything to the DATA folder using the network. Which of the following would be the best practice to set up Ann's permissions correctly, exposing only the minimum rights required?
A technician has received tickets responding a server is responding slowly during business hours. Which of the following should the technician implement so the team will be informed of this behavior in real time?
Which of the following licensing models allows the greatest number of concurrent Windows VMS to run on a host for the lowest cost?
A technician needs to install a Type 1 hypervisor on a server. The server has SD card slots, a SAS controller, and a SATA controller, and it is attached to a NAS. On which of the following drive types should the technician install the hypervisor?
While running a local network security scan an administrator discovers communication between clients and one of the web servers is happening in cleartext. Company policy requires all communication lo be encrypted. Which of the following ports should be closed to stop the deartext communication?
An administrator is installing a new file server that has four drive bays available. Which of the following RAID types would provide the MOST storage as well as disk redundancy?
A Linux server was recently updated. Now, the server stops during the boot process with a blank screen and an£s> prompt. When of the following is the MOST likely cause of this issue?
A Linux server was recently updated. Now, the server stops during the boot process with a blank screen and an f prompt. Which of the following is the most likely cause of this issue?
An administrator has been asked to disable CPU hyperthreading on a server to satisfy a licensing issue. Which of the following best describes how the administrator will likely perform this action?
An administrator is alerted to a hardware failure in a mission-critical server. The alert states that two drives have failed. The administrator notes the drives are in different RAID 1 arrays, and both are hot-swappable. Which of the following steps will be the MOST efficient?
A systems administrator has several different types of hard drives. The administrator is setting up a MAS that will allow end users to see all the drives within the NAS. Which of the following storage types should the administrator use?
Which of the following is a system that scans outgoing email for account numbers, sensitive phrases, and other forms of Pll?
A user logs in to a Linux server and attempts to run the following command:
sudo emacs /root/file
However the user gets the following message:
User userid is not allowed to execute Temacs' on this server. Which of the following would BEST allow the user to find out which commands can be used?
A technician is setting up a small office that consists of five Windows 10 computers. The technician has been asked to use a simple IP configuration without manually adding any IP addresses. Which of the following will the technician MOST likely use for the IP address assignment?
A server administrator must respond to tickets within a certain amount of time. The server administrator needs to adhere to the:
Which of the following techniques can be configured on a server for network redundancy?
A server administrator mounted a new hard disk on a Linux system with a mount point of /newdisk. It was later determined that users were unable to create directories or files on the new mount point. Which of the following commands would successfully mount the drive with the required parameters?
Which of the following are measures that should be taken when a data breach occurs? (Select TWO).
Which of the following will correctly map a script to a home directory for a user based on username?
A technician is installing a variety of servers in a rack. Which of the following is the BEST course of action for the technician to take while loading the rack?
A server administrator is using remote access to update a server. The administrator notices numerous error messages when using YUM to update the applications on a server. Which of the following should the administrator check FIRST?
A technician has received multiple reports of issues with a server. The server occasionally has a BSOD, powers off unexpectedly, and has fans that run continuously. Which of the following BEST represents what the technician should investigate during troubleshooting?
A datacenter in a remote location lost power. The power has since been restored, but one ol the servers has not come back online. After some investigation, the server is found to still be powered off. Which of the following is the BEST method to power on the server remotely?
Which of the following actions should a server administrator take once a new backup scheme has been configured?
Which of the following would a systems administrator implement to ensure all web traffic is secure?
A technician is checking a server rack. Upon entering the room, the technician notices the tans on a particular server in the rack are running at high speeds. This is the only server in the rack that is experiencing this behavior. The ambient temperature in the room appears to be normal. Which of the following is the MOST likely reason why the fans in that server are operating at full speed?
A server administrator wants to run a performance monitor for optimal system utilization. Which of the following metrics can the administrator use for monitoring? (Choose two.)
A technician is trying to determine the reason why a Linux server is not communicating on a network. The returned network configuration is as follows:
eth0: flags=4163<UP, BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 127.0.0.1 network 255.255.0.0 broadcast 127.0.0.1
Which of the following BEST describes what is happening?
A server administrator is completing an OS installation for a new server. The administrator patches the server with the latest vendor-suggested software, configures DHCP, and verifies all network cables are properly connected in the IDF, but there is no network connectivity. Which of the following is the MOST likely reason for the lack of connectivity?
A server room with many racks of servers is managed remotely with occasional on-site support. Which of the following would be the MOST cost-effective option to administer and troubleshoot network problems locally on the servers?
Which of the following can be BEST described as the amount of time a company can afford to be down during recovery from an outage?
A server administrator needs to check remotely for unnecessary running services across 12 servers. Which of the following tools should the administrator use?
A system administrator has been alerted to a zero-day vulnerability that is impacting a service enabled on a server OS. Which of the following would work BEST to limit an attacker from exploiting this vulnerability?
Due to a recent application migration, a company’s current storage solution does not meet the necessary requirements tor hosting data without impacting performance when the data is accessed in real time by multiple users. Which of the following is the BEST solution for this Issue?
Which of the following policies would be BEST to deter a brute-force login attack?
Users have noticed a server is performing below Baseline expectations. While diagnosing me server, an administrator discovers disk drive performance has degraded. The administrator checks the diagnostics on the RAID controller and sees the battery on me controller has gone bad. Which of the following is causing the poor performance on the RAID array?
A server technician notices a server is very low on disk space. Upon inspecting the disk utilization, the technician discovers server logs are taxing up a large amount of space. There is no central log server. Which of the following would help free up disk space?
Winch of the following is a type of replication in which all files are replicated, all the time?
A very old PC is running a critical, proprietary application in MS-DOS. Administrators are concerned about the stability of this computer. Installation media has been lost, and the vendor is out of business. Which of the following would be the BEST course of action to preserve business continuity?
A server is performing slowly, and users are reporting issues connecting to the application on that server. Upon investigation, the server administrator notices several unauthorizedservices running on that server that are successfully communicating to an external site. Which of the following are MOST likely causing the issue?
(Choose two.)
A technician is deploying a single server to monitor and record me security cameras at a remote site, which of the following architecture types should be used to minimize cost?
A company stores extremely sensitive data on an alt-gapped system. Which of the following can Be Implemented to increase security against a potential insider threat?
A server technician installs a new NIC on a server and configures the NIC for IP connectivity. The technician then tests the connection using thepingcommand. Given the following partial output of thepingandipconfigcommands:
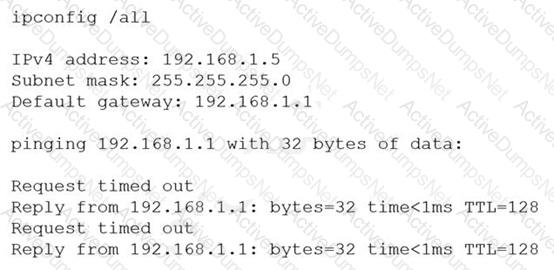
Which of the following caused the issue?
After configuring IP networking on a newly commissioned server, a server administrator installs a straight- through network cable from the patch panel to the switch. The administrator then returns to the server to test network connectivity using the ping command. The partial output of the ping and ipconfig commands are displayed below:
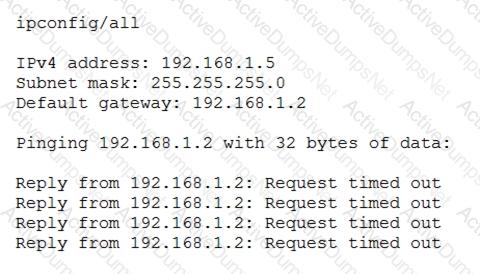
The administrator returns to the switch and notices an amber link light on the port where the server is connected. Which of the following is the MOST likely reason for the lack of network connectivity?
A technician is working on a Linux server. The customer has reported that files in the home directory are missing. The /etc/ f stab file has the following entry:
nfsserver:/home /home nfs defaults 0 0
However, a df -h /home command returns the following information:
/dev/sda2 10G 1G 9G 10% /home
Which of the following should the technician attempt FIRST to resolve the issue?
Which of the following documents would be useful when trying to restore IT infrastructure operations after a non-planned interruption?
A server administrator is experiencing difficulty configuring MySQL on a Linux server. The administrator issues the getenforce command and receives the following output:
># Enforcing
Which of the following commands should the administrator issue to configure MySQL successfully?
A server administrator receives a report that Ann, a new user, is unable to save a file to her home directory on a server. The administrator checks Ann’s home directory permissions and discovers the following:
dr-xr-xr-- /home/Ann
Which of the following commands should the administrator use to resolve the issue without granting unnecessary permissions?
An administrator is configuring a server to communicate with a new storage array. To do so, the administrator enters the WWPN of the new array in the server’s storage configuration. Which of the following technologies is the new connection using?
A server that recently received hardware upgrades has begun to experience random BSOD conditions. Which of the following are likely causes of the issue? (Choose two.)
A storage administrator is investigating an issue with a failed hard drive. A technician replaced the drive in the storage array; however, there is still an issue with the logical volume. Which of the following best describes the NEXT step that should be completed to restore the volume?
A company has implemented a requirement to encrypt all the hard drives on its servers as part of a data loss prevention strategy. Which of the following should the company also perform as a data loss prevention method?
Which of the following tools will analyze network logs in real time to report on suspicious log events?
When configuring networking on a VM, which of the following methods would allow multiple VMs to share the same host IP address?
A server administrator is deploying a new server that has two hard drives on which to install the OS. Which of the following RAID configurations should be used to provide redundancy for the OS?
A technician is connecting a server’s secondary NIC to a separate network. The technician connects the cable to the switch but then does not see any link lights on the NIC. The technician confirms there is nothing wrong on the network or with the physical connection. Which of the following should the technician perform NEXT?
A technician has several possible solutions to a reported server issue. Which of the following BEST represents how the technician should proceed with troubleshooting?
A server administrator has configured a web server. Which of the following does the administrator need to install to make the website trusted?
Users ate experiencing issues when trying to access resources on multiple servers. The servers are virtual and run on an ESX server. A systems administrator is investigating but is unable to connect to any of the virtual servers. When the administrator connects to the host, a purple screen with while letters appears. Which of the following troubleshooting steps should the administrator perform FIRST?
A user cannot save large files to a directory on a Linux server that was accepting smaller files a few minutes ago. Which of the following commands should a technician use to identify the issue?
A technician is unable to access a server’s package repository internally or externally. Which of the following are the MOST likely reasons? (Choose two.)
A technician is connecting a Linux server to a share on a NAS. Which of the following is the MOST appropriate native protocol to use for this task?
A server technician is installing a Windows server OS on a physical server. The specifications for the installation call for a 4TB data volume. To ensure the partition is available to the OS, the technician must verify the:
An administrator connects a server to an external gigabit switch, but the server can only get a speed of 100Mbps. Which of the following is the most likely cause of this issue?
A technician replaces a single faulted disk in the following array RAID 10, Four 15K SAS HDD The technician replaces it from a disk in spare parts, and the array rebuilds the data in a few minutes. After the array rebuild is complete, the system reports the IOPS on the disk array have dropped by almost 60% Which of the following should the technician investigate first?
Which of the following security risks provides unauthorized access to an application?
A technician receives reports that a file server is performing slower than usual after a power failure. While investigating the issue, the technician discovers the write cache was disabled. The technician checks a server configuration document and confirms the cache was previously enabled. Which of the following events most likely caused this change?
An administrator receives an alert that one of the virtual servers has suddenly crashed. The administrator confirms the data center does not have any power failures and then connects to the remote console of the crashed server After connecting to the server console, which of the following should the administrator complete first?
An administrator is troubleshooting connectivity to a remote server. The goal is to remotely connect to the server to make configuration changes. To further troubleshoot, a port scan revealed the ports on the
server as follows:
Port 22: Closed
Port 23: Open
Port 990: Closed
Which of the following next steps should the administrator take?
Reboot the workstation and then the server.
Which of the following should a server administrator configure to ensure access to motherboard software is restricted?
A certain application initially uses 1TB of drive space, but this is expected to double each year for the next two years. Which of the following is the minimum number of 1TB drives that are needed in a RAID 5 configuration?
A server administrator is installing a new server with multiple NICs on it. The Chief Information Officer has asked the administrator to ensure the new server will have the least amount of network downtime but a good amount of network speed. Which of the following best describes what the administrator should implement on the new server?
A Windows server has experienced a BSOD, and the administrator needs to monitor thereboot. The server is in a datacenter with no OOB management. Which of the following tools should the administrator use to complete this task?
A junior administrator reported that the website used for anti-malware updates is not working. The senior administrator then discovered all requests to the anti-malware site are being redirected to a malicious site. Which of the following tools should the senior administrator check first to identify the potential cause of the issue?
Which of the following symbols is used to write a text description per line within a PowerShell script?
A technician is tasked with upgrading 24 hosts simultaneously with a Type 1 hypervisor. Which of the following protocols should the technician use for this upgrade?
A corporation is implementing a cloud model that must meet security and privacy requirements for application development and testing. The company would like to use its own hardware to save money. Which of the following cloud models should be deployed?
Which of the following would protect data in transit?
A bad actor leaves a USB drive with malicious code on it in a company's parking lot. Which of the following describes this scenario?
A technician is configuring a server with eight available drive bays. The technician wants a combination of the most redundancy and the maximum available storage. Which of the following RAID levels should the technician use?
An administrator restores several database files without error while participating in a mock disaster recovery exercise. Later, the administrator reports that the restored databases are
corrupt and cannot be used. Which of the following would best describe what caused this issue?
A server technician is installing application updates on a Linux server. When the technician tries to install a MySQL update, the GUI displays the following error message: AVC denial. Which of the following should the technician do for the MySQL update to install?
A technician is sizing a new server and, for service reasons, needs as many hot-swappable components as possible. Which of the following server components can most commonly be replaced without downtime? (Select three).
An administrator notices a server is offline. Upon checking the console, the administrator discovers the server is stuck at:
Configuring Memory.............
After a reboot, the server still exhibits the same behavior. The administrator is able to log in to the OOB remote management but is unable to log in to the server. Which of the following is the most likely cause of this issue?
An administrator is unable to get server updates from a WSUS server. However, the administrator was able to patch the server successfully last month. Which of the following should the administrator check first?
A storage administrator is configuring a new array to provide storage to a virtual cluster. The array has a built-in backup agent to allow data that is stored on the array to be backed up. The storage administrator wants the virtual cluster to use a file-based storage protocol so the backup agent can just back up the files that change and not the whole data store. Which of the following storage protocols should the administrator use?
Three new servers that use similar types of resources need to be set up, installed with the same OS, and ready within a short time frame. Which of the following installation types would most likely be used?
A server administrator is setting up a disk with enforcement policies on how much data each home share can hold. The amount of data that is redundant on the
server must also be minimized. Which of the following should the administrator perform on the server? (Select two).
A startup company needs to set up an initial disaster recovery site. The site must be cost-effective and deployed quickly. Which of the following sites should the company set up?
A technician is investigating a server's configuration to secure it from physical threats. The technician checks the BIOS and sees the following boot order:
USB Drive CDROM Drive Network Adapter RAID Controller
Additionally, the server's host OS is stored on mirrored drives. Which of the following should the technician do to secure the server?
Following a recent power outage, a server on a server farm has been running slowly. A technician receives a ticket with a request to check for anything out of the ordinary. The technician sees an orange light on the front console of the server, indicating an error. Which of the following should the technician check next?
A user can successfully connect to a database server from a home office but is unable to access it from a hotel room. Which of the following authentication methods is most likely
configured?
A security administrator ran a port scanning tool against a virtual server that is hosting a secure website. A list of open ports was provided as documentation. The management team has requested that non-
essential ports be disabled on the firewall. Which of the following ports must remain open?
Several mobile users are reporting intermittent performance issues when attempting to access network shares on the file server. After some investigation, the server administrator notices the server resources are running at maximum capacity, even during non-peak usage times. A recent port scan of the network identified this server as having too many unnecessary ports open to the public. Which of the following is the most likely cause of the performance issues?
A senior administrator was notified that a junior administrator installed software on a server that should not have new software installed on it. The senior administrator decides to restrict the server via a Group Policy. Which of the following can be used to elevate the permissions?
An administrator is tasked with building an environment consisting of four servers that can each serve the same website. Which of the following concepts is described?
A datacenter has ten 40U racks in a hot/cold aisle configuration. The room has adequate air conditioning, but servers located near the top of the racks are shutting down due to issues with heat. Which of the following should be used to reduce issues with heat?
An administrator is upgrading a group of legacy blade servers to the latest version of the hypervisor. After restarting the server, the upgrade is interrupted. The hypervisor is not available, and the update is not successful. Which of the following should the administrator do next to accomplish this upgrade?
A server administrator implemented a new backup solution and needs to configure backup methods for remote sites. These remote sites have low bandwidth and backups must not
interfere with the network during normal business hours. Which of the following methods can be used to meet these requirements? (Select two).
An employee who was dismissed did not return company-issued equipment. Which of the following is the most important information the IT department needs to give to the legal department?
An administrator is installing a new server and OS. After installing the OS, the administrator logs in and wants to quickly check the network configuration. Which of the following is the best command to use to
accomplish this task?
Several new components have been added to a mission-critical server, and corporate policy states all new components must meet server hardening requirements. Which of the following should be applied?
A systems administrator is performing a routine update to a server. The administrator applies the update, restarts the server, and then conducts routine testing that reveals the critical functionality provided by the server is unavailable. Event logs indicate a core service is failing to start. The service is configured to start automatically, and rolling back the update does not correct the issue. Which of the following is most likely causing the service failure?
An administrator is troubleshooting a server that is rebooting and crashing. The administrator notices that the server is making sounds that are louder than usual. Upon closer inspection, the administrator
discovers that the noises are coming from the front of the chassis. Which of the following is the most likely reason for this behavior?
A systems administrator is installing Windows on an 8TB drive and would like to create a single 8TB partition on the disk. Which of the following options should the administrator use?
A server administrator is reviewing the following specifications:
VM01 Host:
CPU: 2 Physical, 4 Cores
RAM: 16GB
Storage: 16TB
Server 1 on VM01:
CPU: 1 virtual socket, 1 core per socket
RAM: 4GB
Storage: 8TB
Server 2 on VM01:
CPU: 2 virtual sockets, 2 cores per socket
RAM: 8GB
Storage: 10TB
Which of the following is described given these specifications?
Which of the following is an architectural reinforcement that is used to attempt to conceal the exterior of an organization?
A technician is installing an OS on ten servers. Which of the following media installation types would allow for the fastest installation time?
A college is planning for disaster recovery and needs to have access at all times to student data, which contains PII (Personally Identifiable Information). Which of the following would be the most appropriate for the college?
A technician wants to duplicate a physical server to a remote private cloud for disaster recovery purposes. Which of the following techniques would best accomplish this goal?
After a technician upgrades the firmware on a database server that is connected to two external storage arrays, the server prompts the technician to configure RAID. The technician knows the server had several configured RAID sets and thinks the firmware upgrade cleared the RAID configurations. Which of the following should the technician do to troubleshoot this issue?
A company created a new DR plan. The management team would like to begin performing a review of this plan without endangering company data and with a minimal time commitment. Which of the following testing methods would best allow for this type of review?