Which of the following appliances provides users with an extended footprint that allows connections from multiple devices within a designated WLAN?
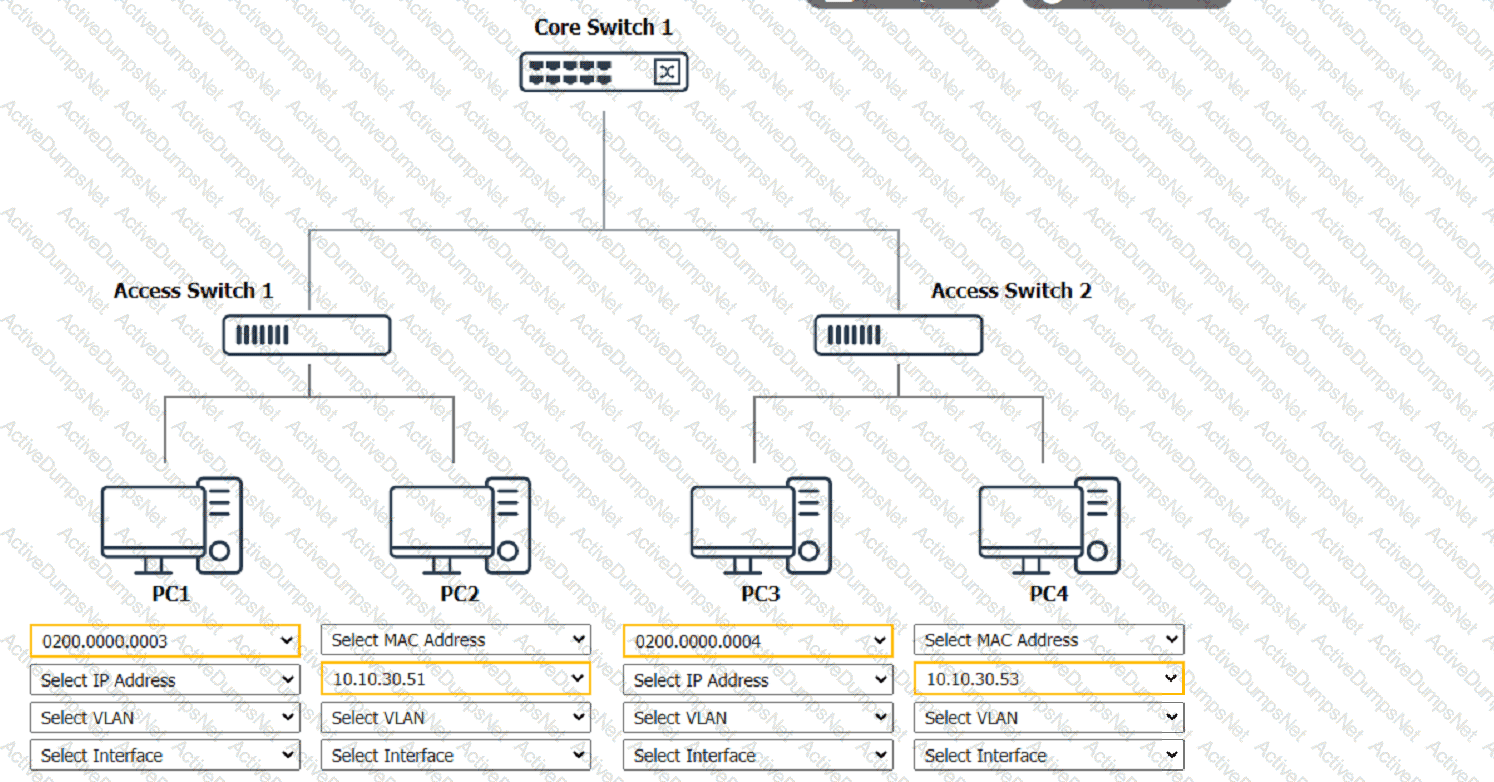
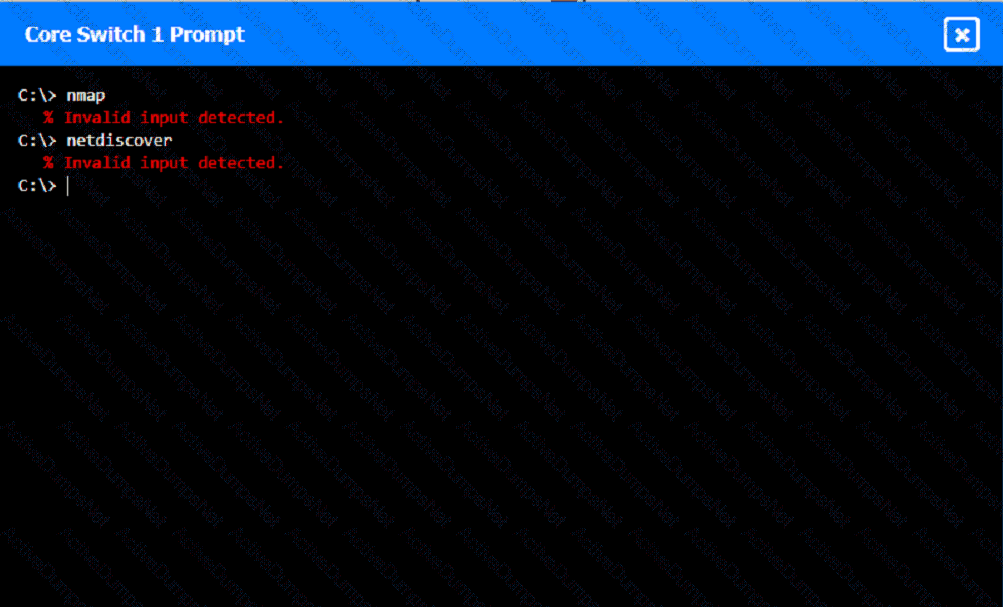
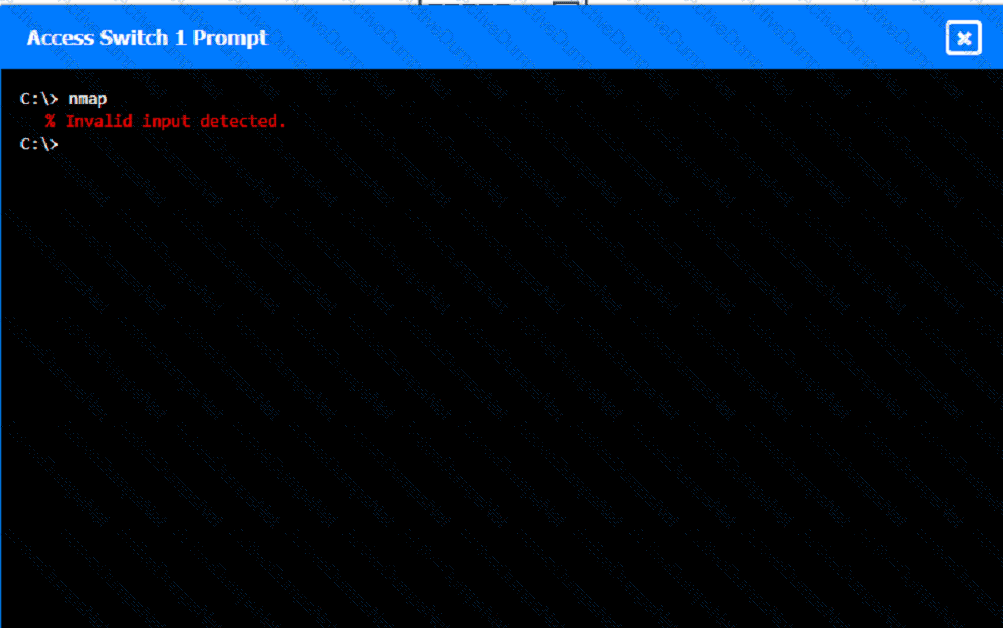
A network technician was recently onboarded to a company. A manager has
tasked the technician with documenting the network and has provided the technician With partial information from previous documentation.
Instructions:
Click on each switch to perform a network discovery by entering commands into the terminal. Fill in the missing information using drop-down menus provided.
A network engineer is testing a website to ensure it is compatible with IPv6. After attempting to ping the website by its IPv6 address, the engineer determines that the DNS has not been set up properly. Which of the following should the network engineer complete to resolve this issue?
A network manager wants to implement a SIEM system to correlate system events. Which of the following protocols should the network manager verify?
A group of users cannot connect to network resources. The technician runs ipconfig from one user's device and is able to ping the gateway shown from the command. Which of the following is most likely preventing the users from accessing network resources?
Which of the following could provide a lightweight and private connection to a remote box?
Which of the following routing protocols is most commonly used to interconnect WANs?
A technician is troubleshooting a user's laptop that is unable to connect to a corporate server. The technician thinks the issue pertains to routing. Which of the following commands should the technician use to identify the issue?
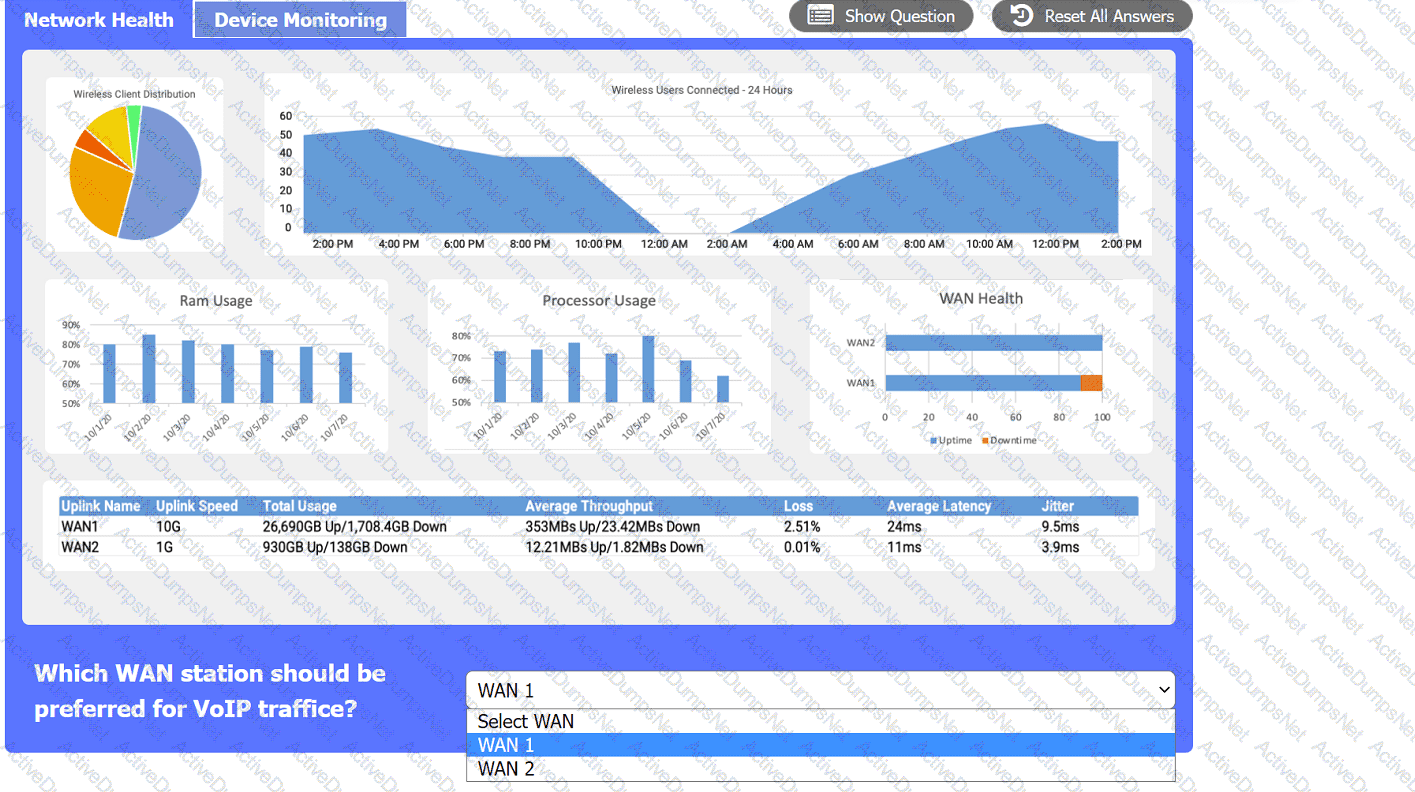
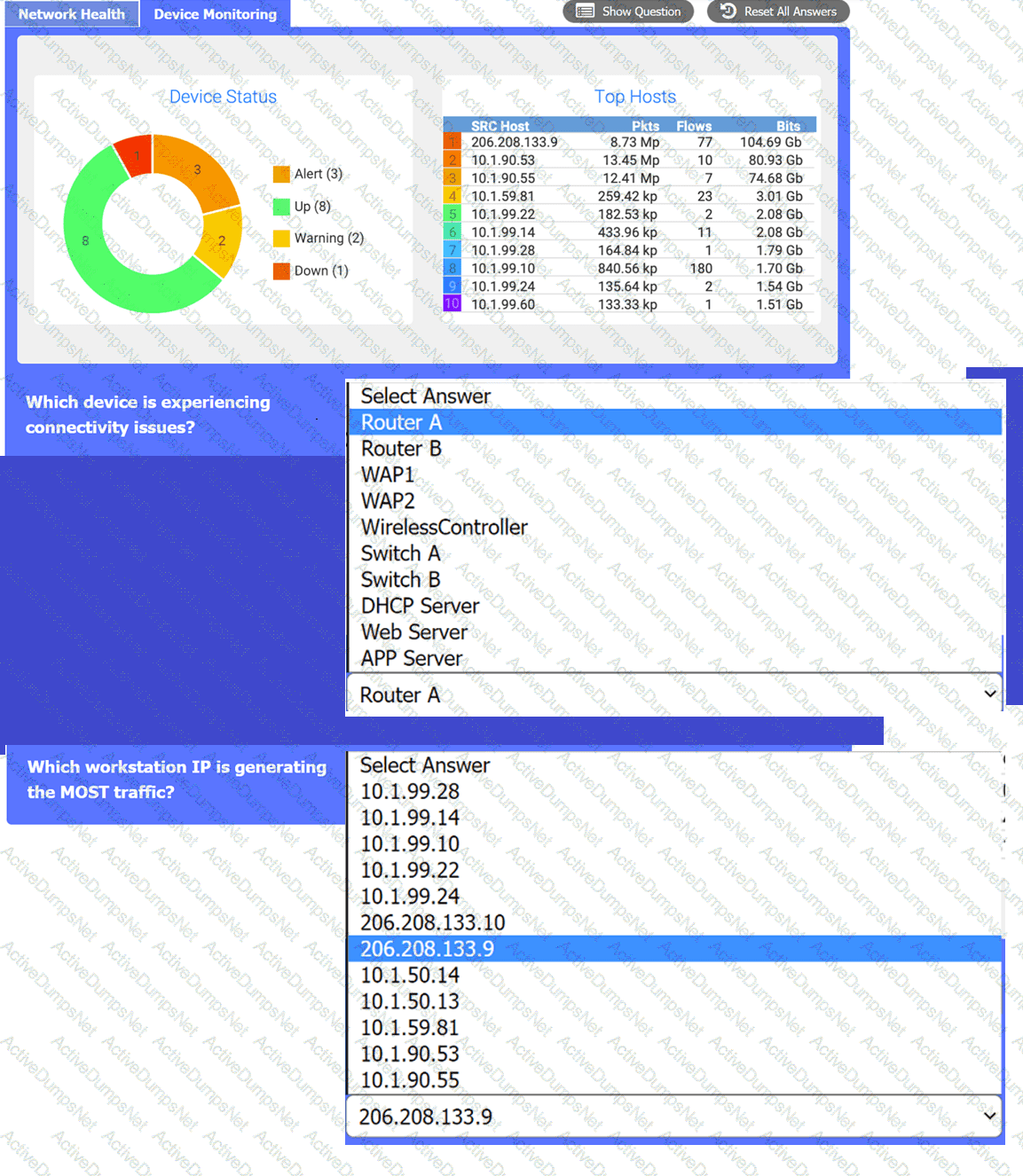
After a recent power outage, users are reporting performance issues accessing the application servers. Wireless users are also reporting intermittent Internet issues.
INSTRUCTIONS
Click on each tab at the top of the screen. Select a widget to view information, then
use the drop-down menus to answer the associated questions. If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Which of the following technologies is thebest choicetolisten for requests and distribute user trafficacross web servers?
An organization requires the ability to send encrypted email messages to a partner from an email server that is hosted on premises. The organization prefers to use the standard default ports when creating firewall rules. Which of the following ports should be open to satisfy the requirements?
A network technician needs to install patch cords from the UTP patch panel to the access switch for a newly occupied set of offices. The patch panel is not labeled for easy jack identification. Which of the following tools provides the easiest way to identify the appropriate patch panel port?
A secure communication link needs to beconfigured between data centers via the internet. The data centers are located in different regions. Which of the following is thebest protocolfor the network administrator to use?
Which of the following is the most likely reason an insurance brokerage would enforce VPN usage?
To reduce costs and increase mobility, a Chief Technology Officer (CTO) wants to adopt cloud services for the organization and its affiliates. To reduce the impact for users, the CTO wants key services to run from the on-site data center and enterprise services to run in the cloud. Which of the following deployment models is the best choice for the organization?
Users at a satellite office are experiencing issues when using videoconferencing. Which of the following should a technician focus on first to rectify these issues?
A network engineer is now in charge of all SNMP management in the organization. The engineer must use a SNMP version that does not utilize plaintext data. Which of the following is the minimum version of SNMP that supports this requirement?
A user is unable to navigate to a website because the provided URL is not resolving to the correct IP address. Other users are able to navigate to the intended website without issue. Which of the following is most likely causing this issue?
Which of the following fiber connector types is the most likely to be used on a network interface card?
Which of the following routing protocols needs to have an autonomous system set in order to establish communication with neighbor devices?
A network administrator configured a router interface as 10.0.0.95 255.255.255.240. The administrator discovers that the router is not routing packets to a web server with IP 10.0.0.81/28. Which of the following is the best explanation?
While troubleshooting a VoIP handset connection, a technician's laptop is able to successfully connect to network resources using the same port. The technician needs to identify the port on the switch. Which of the following should the technician use to determine the switch and port?
Anetwork technicianis troubleshooting afaulty NICandtests the theory. Which of the following should the techniciando next?
Which of the following should be used toobtain remote accessto anetwork appliance that has failed to start up properly?
A Chief Executive Officer (CEO) of a company purchases a new phone that will be used while traveling to different countries. The CEO needs to be able to place outgoing calls and receive incoming calls on the phone using a SIM card. Which of the following cellular technologies does the CEO's phone need?
Which of the following steps in the troubleshooting methodology includes checking logs for recent changes?
Which of the following allows for theinterception of trafficbetween the source and destination?
Which of the following attacks would most likely cause duplicate IP addresses in a network?
A company receives a cease-and-desist order from its ISP regarding prohibited torrent activity. Which of the following should be implemented to comply with the cease-and-desist order?
While troubleshooting connectivity issues, a junior network administrator is given explicit instructions to test the host's TCP/IP stack first. Which of the following commands should the network administrator run?
Before using a guest network, an administrator requires users to accept the terms of use Which of the following is the best way to accomplish this goal?
Which of the following is used to describe the average duration of an outage for a specific service?
Which of the following must be implemented to securely connect a company's headquarters with a branch location?
A network administrator is connecting two Layer 2 switches in a network. These switches must transfer data in multiple networks. Which of the following would fulfill this requirement?
Which of the following IP transmission types encrypts all of the transmitted data?
Which of the following attacks utilizes a network packet that contains multiple network tags?
A network technician is troubleshooting network latency and has determined the issue to be occuring two network switches( Switch10 and Switch11). Symptoms reported included poor video performance and slow file copying. Given the following informtion:
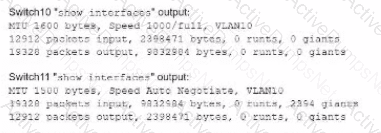
Which of the following should the technician most likely do to resolve the issue?
In an environment with one router, which of the following will allow a network engineer to communicate between VLANs without purchasing additional hardware?
After a company installed a new IPS, the network is experiencing speed degradation. A network administrator is troubleshooting the issue and runs a speed test. The results from the different network locations are as follows:
LocationSpeed DownSpeed Up
Wireless laptop4.8 Mbps47.1 Mbps
Wired desktop5.2 Mbps49.3 Mbps
Firewall48.8 Mbps49.5 Mbps
Which of the following is the most likely issue?
A network administrator is troubleshooting issues with aDHCP serverat a university. More students have recently arrived on campus, and the users areunable to obtain an IP address. Which of the following should the administrator do to address the issue?
Which of the following routing protocols uses an autonomous system number?
A network administrator is in the process of installing 35 PoE security cameras. After the administrator installed and tested the new cables, the administrator installed the cameras. However, a small number of the cameras do not work. Which of the following is the most reason?
A network administrator is developing a method of device monitoring with the following requirements:
•Allows for explicit, by user, privilege management
•Includes centralized logging of changes
•Offers widely accessible remote management
•Provides support of service accounts
Which of the following will most closely meet these requirements?
Which of the following allows a remote user to connect to the network?
Which of the following will allow secure, remote access to internal applications?
Which of the followingconnector typeswould most likely be used to connect to anexternal antenna?
A network administrator deployedwireless networkingin the office area. When users visit theoutdoor patioand try todownload emails with large attachments or stream training videos, they noticebuffering issues. Which of the following is themost likely cause?
A company's marketing team created a new application and would like to create a DNS record for newapplication.comptia.org that always resolves to the same address as www.comptia.org. Which of the following records should the administrator use?
Which of the following network cables involves bounding light off of protective cladding?
A network administrator needs to divide 192.168.1.0/24 into two equal halves. Which of the following subnet masks should the administrator use?
Which of the following are environmental factors that should be considered when installing equipment in a building? (Select two).
Which of the followingportscreates asecure connectionto adirectory service?
Which of the following facilities is the best example of a warm site in the event of information system disruption?
Which of the following does a full-tunnel VPN provide?
Which of the following panels would be best to facilitate a central termination point for all network cables on the floor of a company building?
A network engineer configures the network settings in a new server as follows:
IP address = 192.163.1.15
Subnet mask = 255.255.255.0
Gateway = 192.163.1.255
The server can reach other hosts on the same subnet successfully, but it cannot reach hosts on different subnets. Which of the following is most likely configured incorrectly?
A company recently converted most of the officelaptops to connect wirelesslyto the corporate network. After ahigh-traffic malware attack, narrowing the event to a specific user wasdifficultbecause of thewireless configuration.
Which of the following actions should the company take?
Which of the following steps of the troubleshooting methodology would most likely include checking through each level of the OSI model after the problem has been identified?
Which of the following is most likely responsible for the security and handling of personal data in Europe?
Which of the followingservicesruns onport 636?
A network administrator needs to change where the outside DNS records are hosted. Which of the following records should the administrator change the registrar to accomplish this task?
A network technician is examining the configuration on an access port and notices more than one VLAN has been set. Which of the following best describes how the port is configured?
A systems administrator is configuring a new device to be added to the network. The administrator is planning to perform device hardening prior to connecting the device. Which of the following should the administrator do first?
Early in the morning, an administrator installs a new DHCP server. In the afternoon, some users report they are experiencing network outages. Which of the following is the most likely issue?
Following a fire in a data center, the cabling was replaced. Soon after, an administrator notices network issues. Which of the following are the most likely causes of the network issues? (Select two).
Users usually useRDPto connect to aterminal serverwith hostnameTS19that points to10.0.100.19. However, usersrecently have been unable to connecttoTS19. The technicianpings 10.0.100.19and gets anunreachable error. Which of the following is themost likely cause?
A user's home mesh wireless network is experiencing latency issues. A technician has:
•Performed a speed test.
•Rebooted the devices.
•Performed a site survey.
•Performed a wireless packet capture.
The technician reviews the following information:
The technician notices in the packet capture that frames were retransmitted. Which of the following is the most likely cause of the user's network issue?
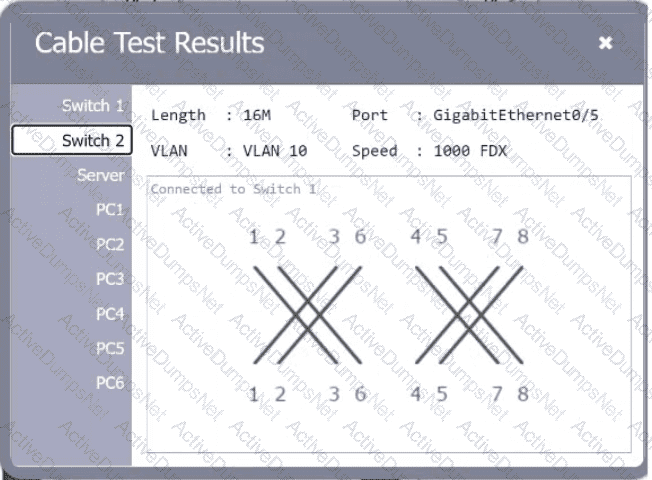
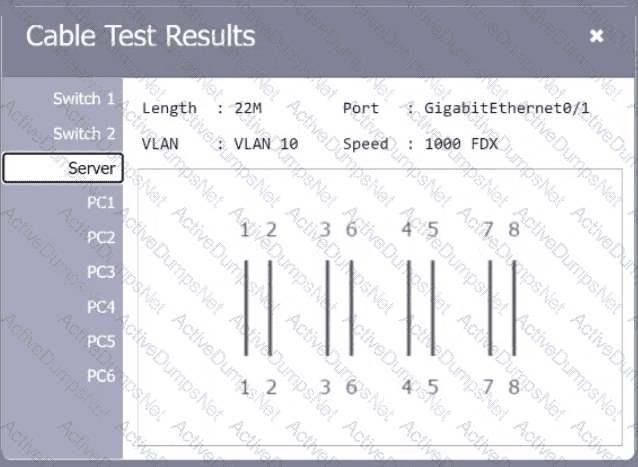
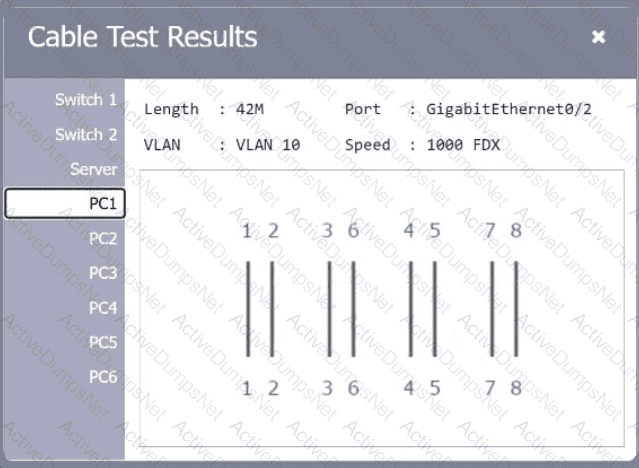
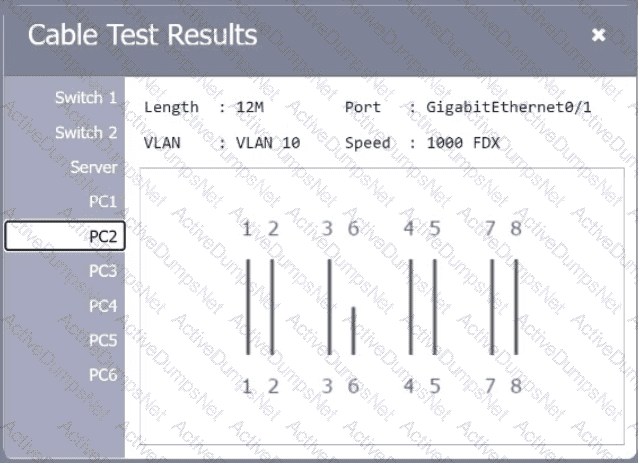
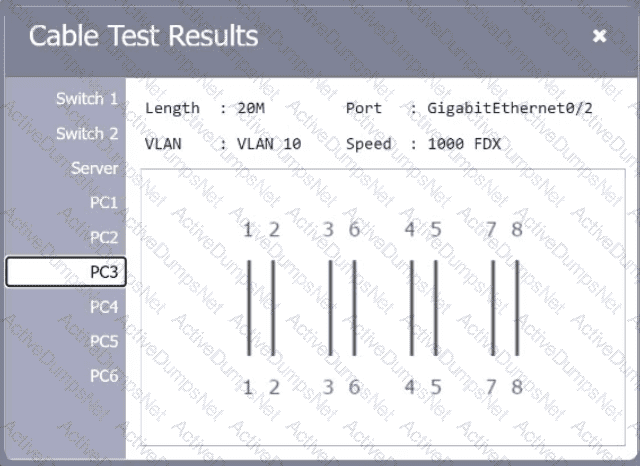
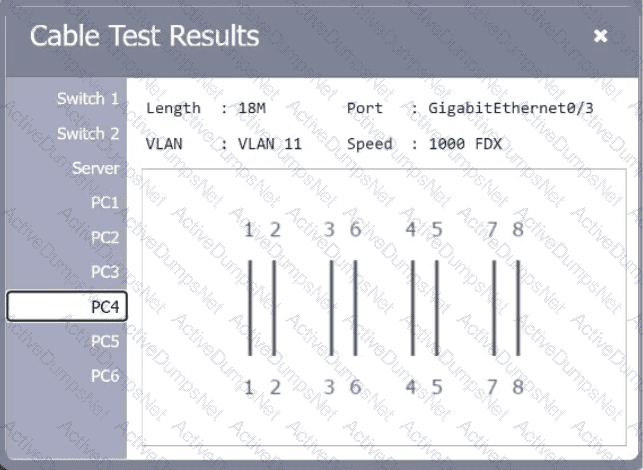
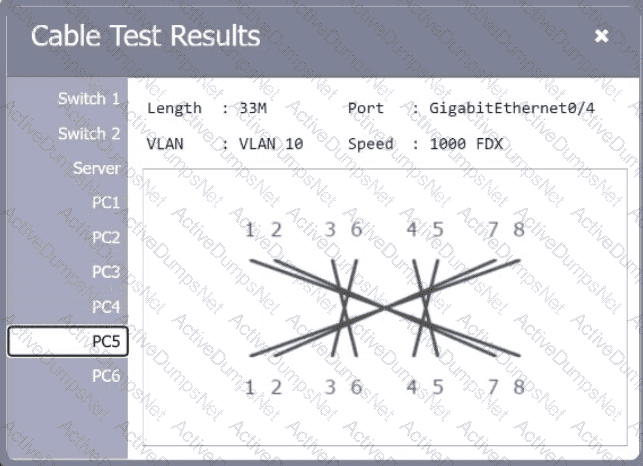
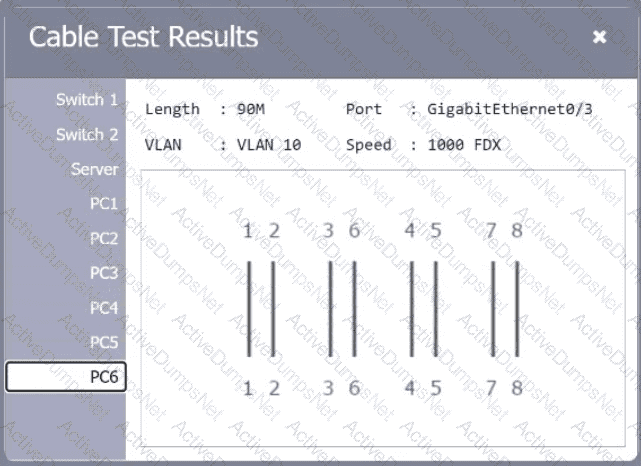
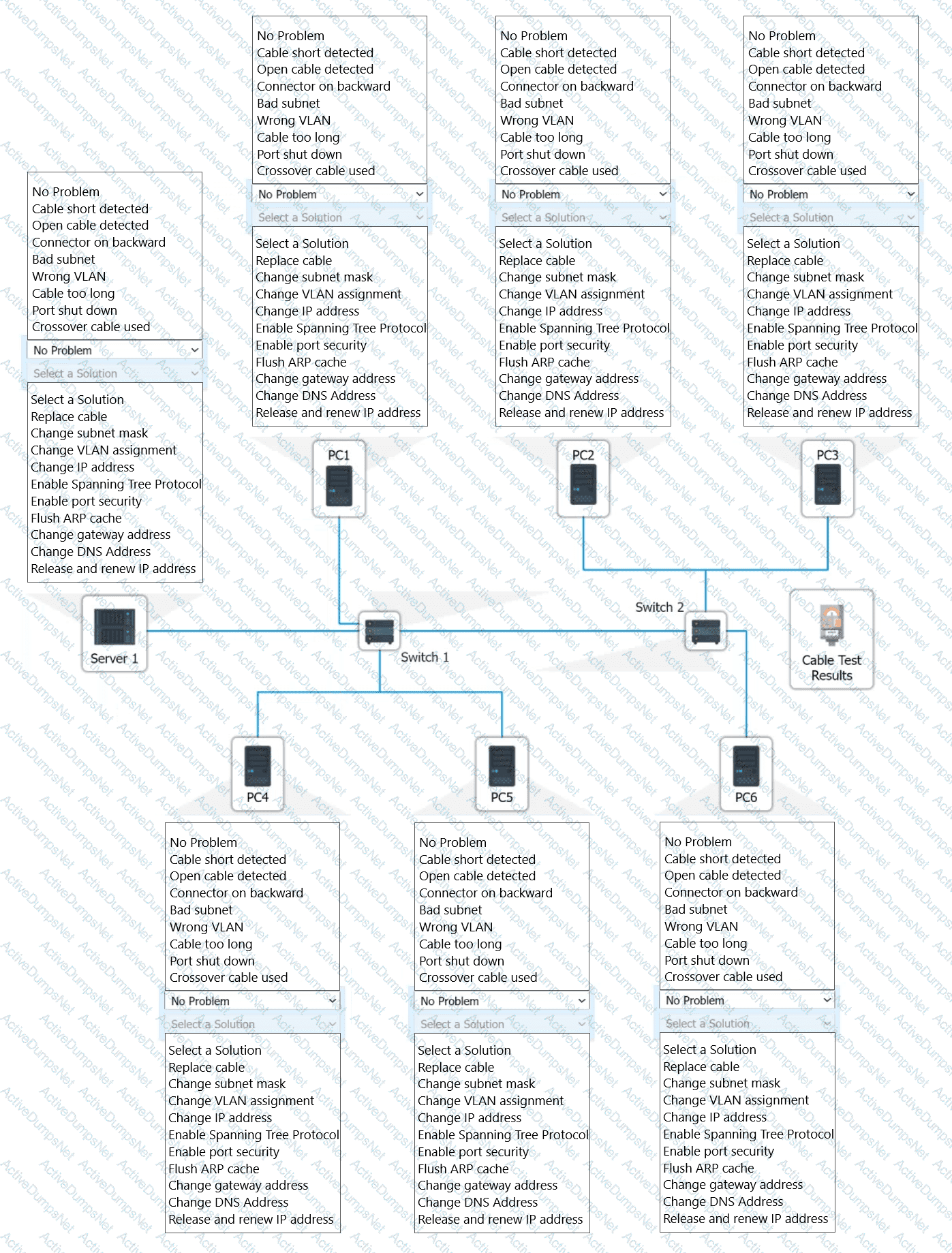
A network technician needs to resolve some issues with a customer's SOHO network. The
customer reports that some of the PCs are not connecting to the network, while others
appear to be working as intended.
INSTRUCTIONS
Troubleshoot all the network components.
Review the cable test results first, then diagnose by clicking on the appropriate PC,
server, and Layer 2 switch.
Identify any components with a problem and recommend a solution to correct each
problem.
If at any time you would like to bring back
the initial state of the simulation, please
click the Reset All button.

A user connects to a corporate VPN via a web browser and is able to use TLS to access the internal financial system to input a time card. Which of the following best describes how the VPN is being used?
A network administrator wants to increase network security by preventing client devices from communicating directly with each other on the same subnet. Which of the following technologies should be implemented?
After changes were made to a firewall, users are no longer able to access a web server. A network administrator wants to ensure that ports 80 and 443 on the web server are still accessible from the user IP space. Which of the following commands is best suited to perfom this testing?
Network administrators are using the Telnet protocol to administer network devices that are on the 192.168.1.0/24 subnet. Which of the following tools should the administrator use to best identify the devices?
As part of an attack, a threat actor purposefully overflows the content-addressable memory (CAM) table on a switch. Which of the following types of attacks is this scenario an example of?
A network engineer configures a new switch and connects it to an existing switch for expansion and redundancy. Users immediately lose connectivity to the network. The network engineer notes the following spanning tree information from both switches:
Switch 1
Port State Cost
1 Forward 2
2 Forward 2
Switch 2
Port State Cost
1 Forward 2
2 Forward 2
Which of the following best describes the issue?
Adata center interconnectusing aVXLANwas recently implemented. A network engineer observesslow performance and fragmentationon the interconnect. Which of the following technologies willresolve the issue?
A company has observedincreased user traffictogambling websitesand wants tolimit this behavioron work computers. Which of the following should the companymost likely implement?
A network administrator installed anew VLANto the network after a company added an additional floor to the office. Users areunable to obtain an IP addresson the new VLAN, but ports on existing VLANs are working properly. Which of the following configurations should the administrator update?
Which of the following is the most closely associated with segmenting compute resources within a single cloud account?
Which of the following best explains the role of confidentiality with regard to data at rest?
A network administrator needs to add 255 useable IP addresses to the network. A /24 is currently in use. Which of the following prefixes would fulfill this need?
A technician is troubleshooting a computer issue for a user who works in a new annex of an office building. The user is reporting slow speeds and intermittent connectivity. The computer is connected via a Cat 6 cable to a distribution switch that is 492ft (150m) away. Which of the following should the technician implement to correct the issue?