A multicast network is sing Bidirectional PIM. Which two combined actions achieve high availability so that two RPs within the same network can act in a redundant manner? (Choose two)
A network security team observes phishing attacks on a user machine from a remote location. The organization has a policy of saving confidential data on two different systems using different types of authentication. What is the next step to control such events after the security team verifies all users in Zero Trust modeling?
Company XYZ has multiple production units and marketing departments across the region The current network is a mixture of point-to-point links and MPLS Layer 3 VPN service from the provider. The Info-Sec team has suggested to isolate production traffic end-to-end with an encryption over the transport network to comply with the HIPAA standard Which solution must be used in their design if Company XYZ wants a quick roll out”?
What is a connection service inside a data center that provides direct connectivity to a cloud provider?
Which two statements describe the usage of the IS-IS overload bit technique? (Choose two )
Which two factors must be considered while calculating the RTO? (Choose two )
A network attacker exploits application flaws to compromise critical systems in the organization with these objectives:
• Obtain sensitive data and export the data out of the network.
• Compromise developer and administrator credentials to potentially
What is the next step after application discovery is completed in Zero Trust networkings
Which two statements describe the hierarchical LAN design model? (Choose two)
Which actions are performed at the distribution layer of the three-layer hierarchical network design model? (Choose two)
Router R1 is a BGP speaker with one peering neighbor over link "A". When the R1 link/interface "A" fails, routing announcements are terminated, which results in the tearing down of the state for all BGP routes at each end of the link. What is this a good example of?
Company XYZ wants to prevent switch loops caused by unidirectional point-point-link condition on Rapid FVST + and MST. Which technology can be used in the design to meet this requirement?
The administrator of a small branch office wants to implement the Layer 2 network without running STP The office has some redundant paths Which mechanism can the administrator use to allow redundancy without creating Layer 2 loops?
A network design includes a long signaling delay in notifying the Layer 3 control plane that an interface has failed Which two of these actions would reduce that delay? (Choose two.)
Agile and Waterfall are two popular methods for organizing projects. What describes any Agile network design development process?
Which effect of using ingress filtering to prevent spoofed addresses on a network design is true?
Which two characteristics apply to firewall transparent mode operations in a firewall solution design? (Choose two.)
Cost is often one of the motivators for a business to migrate from a traditional network to a software- defined network. Which design decision is directly influenced by CAPEX drivers?
When consumers that leverage laaS reach 100% resource capacity, what can be used to redirect the overflow of traffic to the public cloud so there is no disruption to service?
An engineer must redesign the QoS strategy for Company XYZ The current network is experiencing many dropped packets due to oversubscription of the guaranteed bandwidth allocated by the service provider. Company XYZ wants a design with a QoS strategy that controls the traffic flow leaving the Edge router to minimize packet drops Which QoS technique can be recommended as a solution?
Company XYZ is running OSPF in their network. They have merged with another company that is running EIGRP as the routing protocol. Company XYZ now needs the two domains to talk to each other with redundancy, while maintaining a loop free environment. The solution must scale when new networks are added into the network in the near future. Which technology can be used to meet these requirements?
As network designer, which option is your main concern with regards to virtualizing multiple network zones into a single hardware device?
How many fully established neighbour relationships exist on an Ethernet with five routers running OSPF as network type broadcast?
The network designer needs to use GLOP IP address in order make them unique within their ASN, which
multicast address range will be considered?
Refer to the diagram.
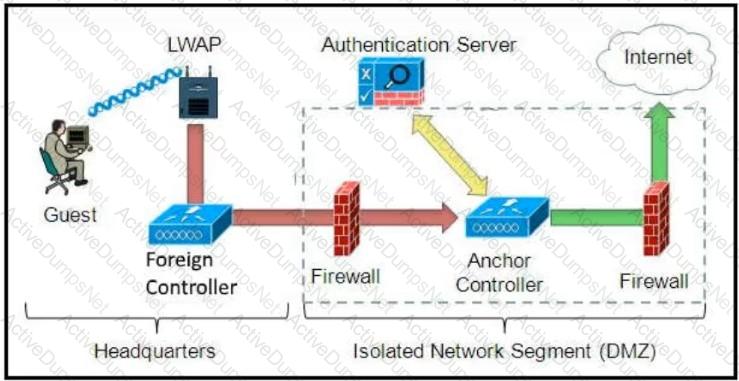
Which solution must be used to send traffic from the foreign wireless LAN controller to the anchor wireless LAN controller?
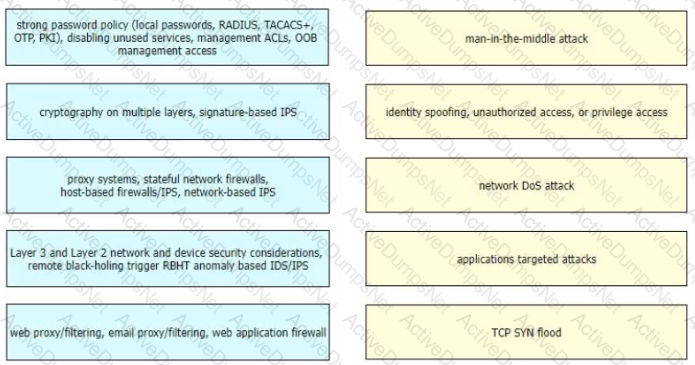
Drag and drop the correct mitigation methods from the left onto the corresponding types of attack on the right
Refer to the exhibit.
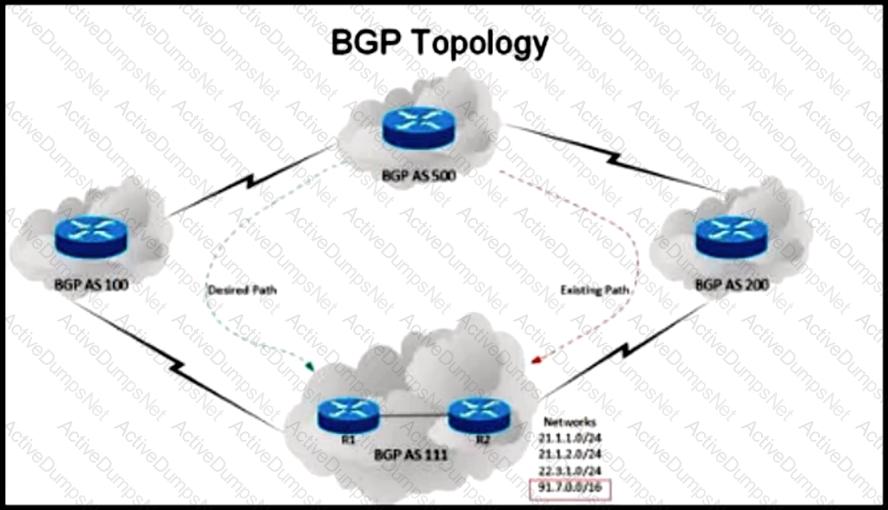
An engineer has been asked to redesign the traffic flow toward AS 111 coming from AS 500.Traffic destined to AS 111 network 91 7 0.0/16 should come in via AS 100. while traffic destined to all other networks in AS 111 should continue to use the existing path Which BGP attributes are best suited to control this inbound traffic coming from BGP AS 500 Into the 91.7.0.0/16 network?
A healthcare provider discovers that protected health information of patients was altered without patient consent. The healthcare provider is subject to HIPAA compliance and is required to protect PHI data. Which type of security safeguard should be implemented to resolve this issue?
QUESTION 69 Refer to the exhibit. AJI links are P2P Layer 3. A high availability application is synchronizing data between host A and host B. To increase chance of delivery the same data is sent twice from host A on two different NICs toward the two NICs on host B.

Which solution must be deployed in the network to ensure that any failure in the network does not trigger data loss on host B?
You have been tasked with designing a data center interconnect as part of business continuity You want to use FCoE over this DCI to support synchronous replication. Which two technologies allow for FCoE via lossless Ethernet or data center bridging? (Choose two.)
The Company XYZ network is experiencing attacks against their router. Which type of Control Plane Protection must be used on the router to protect all control plane IP traffic that is destined directly for one of the router interfaces?
For a company that offers online billing systems for their customers, which strategy ensures the RPO is kept as low as possible?
Which action must be taken before new VoIP systems are implemented on a network to ensure that the network is ready to handle the traffic?
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
Which component of the SDN architecture automatically ensures that application traffic is routed according to policies established by network administrators?
As part of a new network design documentation, you are required to explain the reason for choosing cisco FabricPath for Layer 2 loop avoidance.
Which two elements help Cisco FabricPath mitigate Layer 2 loops if they happen in the Layer 2 MP network?
(Choose two)
Which function is performed at the access layer of the three-layer hierarchical network design model?
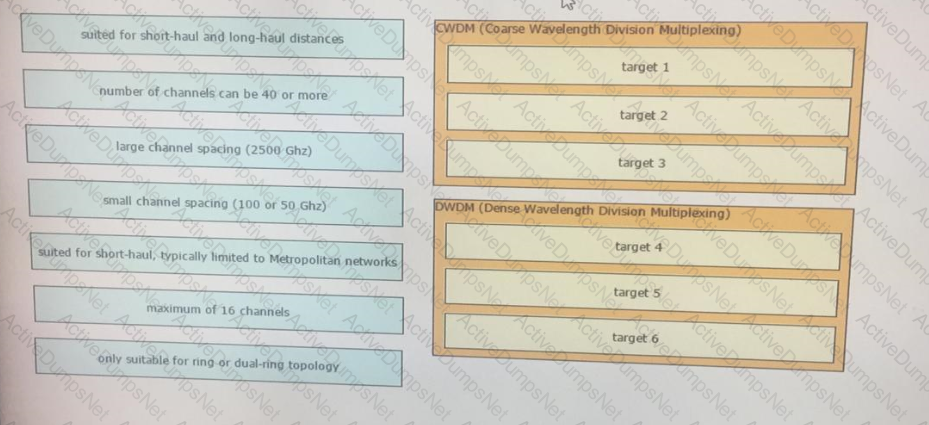
Drag and drop the optical technology design characteristics on the left to the correct optical technologies on the right. Not all options are used
Which two control plane policer designs must be considered to achieve high availability? (Choose two.)
What are two examples of components that are part of an SDN architecture? (Choose two.)
End users are moving swiftly toward a hybrid cloud model to support faster IT service delivery. To implement a hybrid cloud architecture, what are two critical requirements for broader cloud service provider and vendor interoperability in terms of cloud security and compliance? (Choose two.)
A network security team uses a purpose-built tool to actively monitor the campus network, applications, and user activity. The team also analyzes enterprise telemetry data from IPFIX data records that are received from devices in the campus network. Which action can be taken based on the augmented data?
Which methodology is the leading lifecycle approach to network design and implementation?
A network architect in an enterprise is designing a network policy for certain database applications. The goal of the policy is to allow these applications to access the internet directly, whereas other user and network applications that communicate with systems or users outside their own network must be routed through the data center. The focus is on achieving higher availability and a better user experience for the database applications, but switching between different network paths based on performance characteristics must be supported.
Which solution meets these requirements?
Company XYZ is revisiting the security design for their data center because they now have a requirement to control traffic within a subnet and implement deep packet inspection Which technology meets the updated requirements and can be incorporated into the design?
You are designing a network for a branch office. In order to improve convergence time, you are required to use the BFD feature Which four routing protocols can you use to facilitate this? (Choose four.)
Which project management methodology is characterized by a having a low client
involvement?
An enterprise requires MPLS connected branches to access cloud-based Microsoft 365 services over an SD-WAN solution. Internet access Is available only at dual regional hub sites that are connected to the MPLS network. Which connectivity method provides an optimum access method to the cloud-based services If one ISP suffers loss or latency?
Various teams in different organizations within an enterprise are preparing low-level design documents to capture network parameters using a Waterfall project model:
• hardware sizing and power consumption
• Layer 2 and layer 3 services parameters
• configuration of all control plane protocols
Input from relevant stakeholders was captured at the start of the project, and the project scope has been defined based on the parameters above. What impact will it have on documentation and project deliverables if the stakeholders ask to have changes carried out in the network before the information has been captured?
An external edge router provides connectivity from a service provider to an enterprise Which two Internet edge best practices meet compliance regulations'? (Choose two )
Company XYZ is in the process of identifying which transport mechanism(s) to use as their WAN technology. Their main two requirements are.
• a technology that could offer DPI, SLA, secure tunnels, privacy, QoS, scalability, reliability, and ease of management
• a technology that is cost-effective
Which WAN technology(ies) should be included in the design of company XYZ?
Refer to the exhibit.
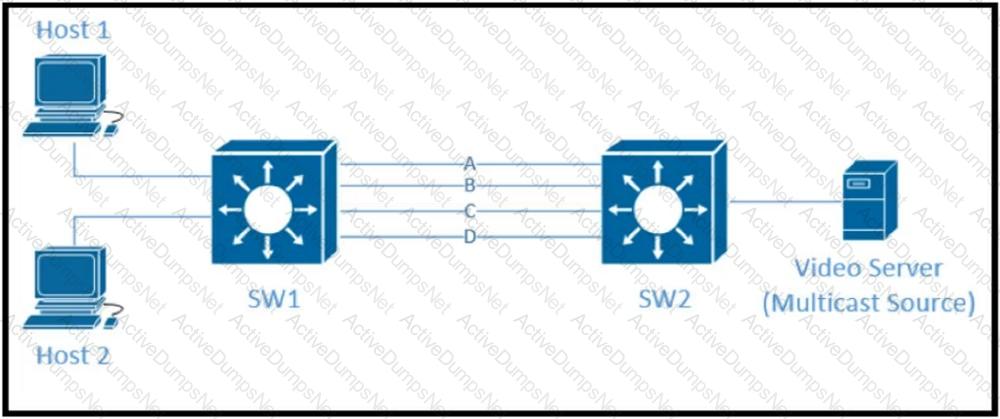
Traffic was equally balanced between Layer 3 links on core switches SW1 and SW2 before an introduction of the new video server in the network. This video server uses multicast to send video streams to hosts and now one of the links between core switches is over utilized Which design solution solves this issue?
Which two statements describe the functionality of OSPF packet-pacing timers? (Choose two )
The group-pacing timer controls the interval that is used for group and individual LSA refreshment
Which mechanism provides Layer 2 fault isolation between data centers?
A software-defined networking (SDN) controller teams network topology information by using BGP link-state sessions with the route reflectors of an MPLS-enabled network. The controller then uses the topology information to apply on-demand traffic policies to the network through a protocol that is supported from all Layer 3 routers Each policy is represented as a RIB entry in the control plane of the router Which SDN model has been implemented?
Identity and access management between multiple users and multiple applications has become a mandatory requirement for Company XYZ to fight against ever increasing cybersecurity threats. To achieve this, federated identity services have been deployed in the Company XYZ network to provide single sign-on and Multi-Factor Authentication for the applications and services. Which protocol can be used by Company XYZ to provide authentication and authorization services?
The Agile Manifesto is a document that defines the key values and principles behind the Agile philosophy and helps development teams work more efficiently and sustainably Each of the four key values is split into two sections a left-hand side and a right-hand side In other words, though there is value in the items on the right we value the items on the left more What is one of the key values of the Agile Manifesto?
Which statement about OSPF hub-and-spoke topology is true?
An architect receives a functional requirement for a NAC system from a customer security policy stating that if a corporate Wi-Fi device does not meet current AV definitions, then it cannot access the corporate network until the definitions are updated. Which component should be built into the NAC design?
You want to split an Ethernet domain in two.
Which parameter must be unique in this design to keep the two domains separated?
According to the CIA triad principles for network security design, which principle should be priority for a Zero Trust network?
A customer migrates from a traditional Layer 2 data center network into a new SDN-based spine-and-leaf VXLAN data center within the same location Its applications cannot be readdressed and the customer does not want to perform the migration in a single operation How should the legacy network and new network be connected?
Which two actions must merchants do to be compliant with the Payment Card Industry Data Security Standard? (Choose two.)
A large enterprise customer has a single router that uses two active/active 10-Mbps internet links in one of its
offices. Each link currently handles approximately 7 Mbps of traffic, which is close to the full link capacity.
When a link fails, the failure leads to significantly degraded performance of all applications. Static routing is
used. The current ISP cannot deliver additional bandwidth capacity on the existing links. The customer needs
a network design that is resistant to failure, but does not increase CAPEX. Which solution should be proposed
to the customer?
Hybrid cloud computing allows organizations to like advantage of public and private cloud models Which best practice should organizations follow to ensure data security in the private cloud?
A company requires an RPO of less than 10 seconds to ensure business continuity. Which technology should be deployed?
A business invests in SDN and develops its own SDN controller that, due to budget constraints, runs on a single controller. The controller actively places an exclusive lock on the configuration of the devices to ensure it is the only source of changes to the environment. What is the result if the controller fails?
Which Interconnectivity method offers the fastest convergence in the event of a unidirectional issue between three Layer 3 switches connected together with routed links in the same rack in a data center?
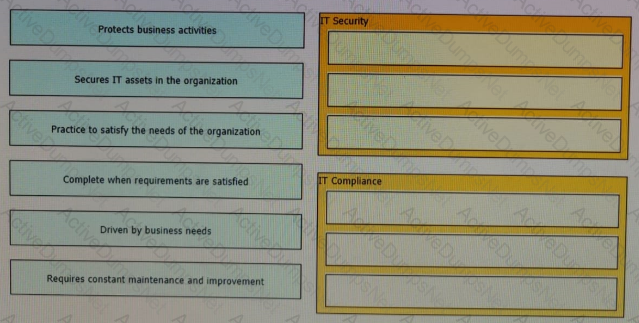
The line between security and compliance is easily blurred and is, to a large extent, a moving target Drag and drop each of the requirements on the left to the appropriate section on the right
Which encoding format does cisco ios XE software support for NETCONF?
Which two characteristics are associated with 802 1s? (Choose two)
Refer to the exhibit.
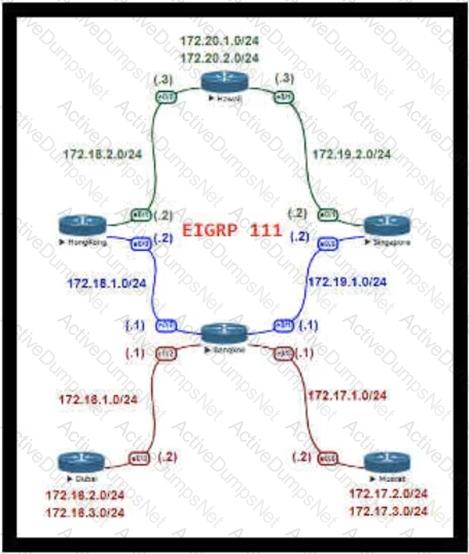
For Company XYZ Bangkok is using ECMP to reach the 172 20 2 0/24 network The company wants a design that would allow them to forward traffic from 172 16 2 0/24 toward 172 20 2 0/24 via the Singapore router as the preferred route The rest of the traffic should continue to use ECMP Which technology fulfills this design requirement?
Which tool automates network implementation activities and shortens the implementation lifecycle?
An enterprise plans to evolve from a traditional WAN network to a software-defined WAN network. The existing devices have limited capability when it comes to virtualization. As the migration is carried out, enterprise applications and services must not experience any traffic impact. Which implementation plan can be used to accommodate this during the migration phase?
Company XYZ is planning to deploy primary and secondary (disaster recovery) data center sites. Each of these sites will have redundant SAN fabrics and data protection is expected between the data center sites. The sites are 100 miles (160 km) apart and target RPO/RTO are 3 hrs and 24 hrs, respectively. Which two considerations must Company XYZ bear in mind when deploying replication in their scenario? (Choose two.)
You are designing a new Ethernet-based metro-area network for an enterprise customer to connect 50 sites within the same city OSPF will be the routing protocol used. The customer is primarily concerned with IPv4 address conservation and convergence time. Which two combined actions do you recommend? (Choose two)
Which mechanism enables small, unmanaged switches to plug into ports of access switches without risking switch loops?
An engineer is designing the QoS strategy for Company XYZ. Based on initial analysis, a lot of scavenger type of traffic is traversing the network's 20Mb Internet link toward the service provider. The new design must use a QoS technique that limits scavenger traffic to 2 Mbps, which helps avoid oversubscription of the link during times of congestion. Which QoS technique can be used to facilitate this requirement?
Which three Cisco products are used in conjunction with Red Hat to provide an NFVi solution? (Choose three.)
Which technology is an open-source infrastructure automation tool that automates repetitive tasks for users who work in networks such as cloud provisioning and intraservice orchestration?
Which design principal improves network resiliency?
A company plans to use BFD between its routers to detect a connectivity problem inside the switched network. An IPS is transparently installed between the switches. Which packets shold the IPS forward for BFD to work under all circumstances?
Company XYZ wants to secure the data plane of their network. Which two technologies can be included in the security design? (Choose two)
A business requirement is supplied to an architect from a car manufacturer stating their business model is changing to just-in-time manufacturing and a new network is required, the manufacturer does not produce all of the specific components m-house. which area should the architect focus on initially?
Scrum is a subset of Agile and is a lightweight process framework for Agile development Which role becomes the interface between the business the customers and their product-related needs on one side and the Team on the other?
Enterprise XYZ wants to implement fast convergence on their network and optimize timers for OSPF However they also want to prevent excess flooding of LSAs if there is a constantly flapping link on the network Which timers can help prevent excess flooding of LSAs for OSPF?
The cloud like the Internet is a massive network of independent resources that are designed to be fault tolerant Software components that run in the cloud have no dependencies on the underlying infrastructure which may fail at any time Which two constraints of REST are important when building cloud-based solutions'? (Choose two )
Which design consideration is valid when you contrast fabricPath and trill?
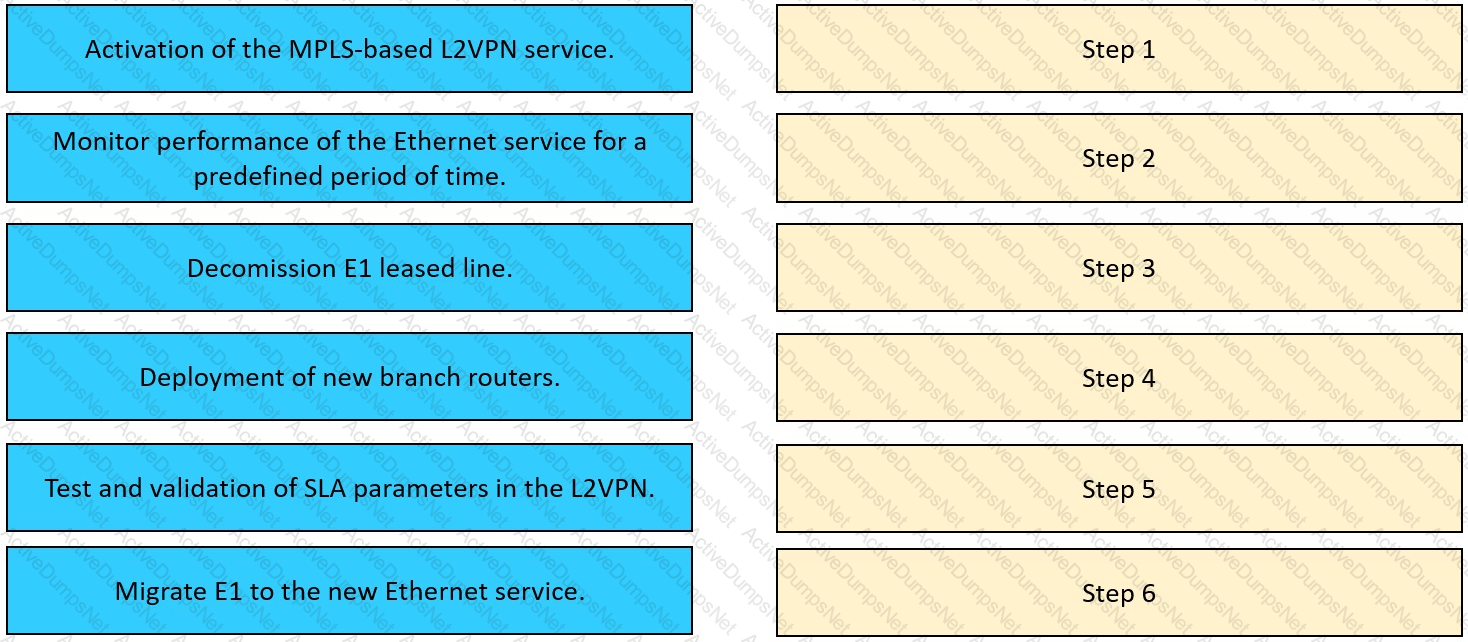
The network team in XYZ Corp wants to modernize their infrastructure and is evaluating an implementation and migration plan to allow integration MPLS-based, Layer 2 Ethernet services managed by a service provider to connect branches and remote offices. To decrease OpEx and improve
response times when network components fail, XYZ Corp decided to acquire and deploy new routers. The network currently is operated over E1 leased lines (2 Mbps) with a managed CE service provided by the telco.
Drag and drop the implementation steps from the left onto the corresponding targets on the right in the correct order.
Which two possible drawbacks should you consider when introducing Network Functions Virtualization in a network design? (Choose two)
You are designing the QoS policy for a company that is running many TCP-based applications. The company is experiencing tail drops for these applications. The company wants to use a congestion avoidance technique for these applications. Which QoS strategy can be used to fulfill the requirement?
What advantage of placing the IS-IS layer 2 flooding domain boundary at the core Layer in a three-layer hierarchical network is true?
As part of workspace digitization, a large enterprise has migrated all their users to Desktop as a Sen/ice (DaaS), by hosting the backend system in their on-premises data center. Some of the branches have started to experience disconnections to the DaaS at periodic intervals, however, local users in the data center and head office do not experience this behavior. Which technology can be used to mitigate this issue?
Refer to the exhibit.
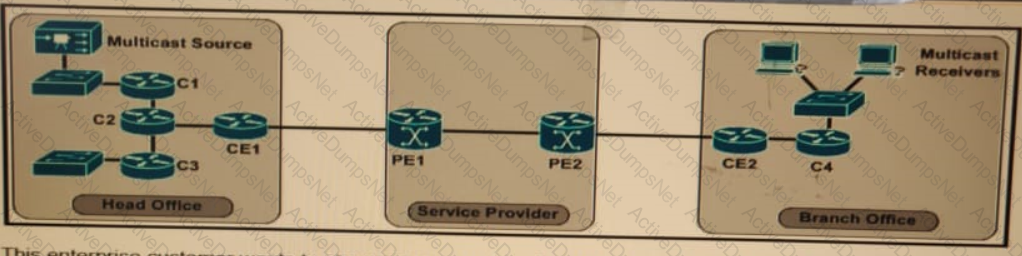
The enterprise customer wants to stream one-way video from their head office to eight branch offices using multicast. Their current service provider provides a Layer3 VPN solution and manages the CE routers, but they do not currently support multicast. Which solution quickly allows this multicast traffic to go through while allowing for future scalability?
Creating a network that functions as a strategic part of the business rather than simply being a cost center, starts with a good understanding of business requirements and processes What specific type of knowledge helps to create high-level LAN WAN. and data center designs that support and enable the business?
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
The network designer needs to use GLOP IP addresses in order to make them unique within their ASN Which multicast address range should be used?
A European national bank considers migrating its on-premises systems to a private cloud offering in a non-European location to significantly reduce IT costs. What is a primary factor prior to migration?
Which two data plane hardening techniques are true? (Choose two)
Which main IoT migration aspect should be reviewed for a manufacturing plant?
Which feature is supported by NETCONF but is not supported by SNMP?
Company XYZ wants to use the FCAPS ISO standard for network management design. The focus of the design should be to monitor and keep track of any performance issues by continuously collecting and analyzing statistical information to monitor, correct, and optimize any reduced responsiveness across the network. Which layer accomplishes this design requirement?
A customer asks you to perform a high level review of their upcoming WAN refresh for remote sites The review is specially focused on their retail store operations consisting of 500+ locations connected via mutlipoint IPsec VPN solution. Which routing protocol would be valid but would also be the most restrictive for the expansion of this deployment model?
A network architect must redesign a service provider edge, where multiservice and multitenant PEs are currently present. Which design feature should be minimized in the new design to achieve reliability?
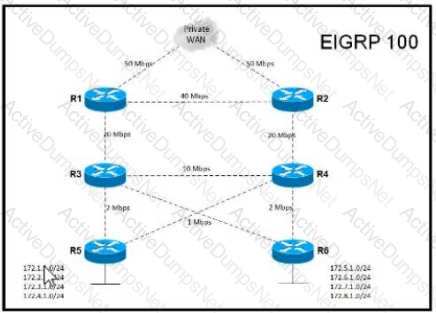
Refer to the exhibit Company XYZ is a large enterprise network where the WAN traffic utilizes most of the link. The IT team in the company often reports Stuck-In-Active problems The company is set to acquire another company that will also be running EIGRP and which will connect to the Company XYZ R3 and R4 routers This acquisition could make the issue worse Which design solution solves this problem?
A private cloud is accessed over the private IT network infrastructure that is potentially vulnerable to violations, data leaks, and man-in- the-middle attacks. The security team is evaluating the following solutions to address the challenges:
•Encrypt data at rest and in transition.
•Use strong identity and access management (IAM) capabilities.
•Communicate the inherent data security risks to your customers and end-users.
Assuming that adoption of a hybrid cloud model is likely to occur within the next 12 months, which two solutions can also help provide protection in a hybrid cloud environment? (Choose two.)
Which solution component helps to achieve rapid migration to the cloud for SaaS and public cloud leveraging SD-WAN capabilities?
Company XYZ has a multicast domain that spans across multiple autonomous systems. The company wants to choose a technology that provides simplified and controlled approach to interconnecting the multicast domains. Which technology is the best fit for this purpose?
Which two features control multicast traffic in a VLAN environment? (Choose two)
What are two examples of business goals to be considered when a network design is built? (Choose two.)
Which type of interface are OpenFlow and OpFlex?
Which parameter is the most important factor to consider when deciding service placement in a cloud solution?
The Company XYZ network requires OSPF dead neighbor detection in a subsecond manner However the company network does not support BFD Which other feature can be used to fulfill the design requirement?
A multinational enterprise integrates a cloud solution with these objectives
• Achieve seamless connectivity across different countries and regions
• Extend data center and private clouds into public clouds and provider-hosted clouds
What are two outcomes of deploying data centers and fabrics that interconnect different cloud networks? (Choose two.)
In an OSPF network with routers connected together with Ethernet cabling, which topology typically takes the longest to converge?