What is a key first step in developing a critical path method schedule?
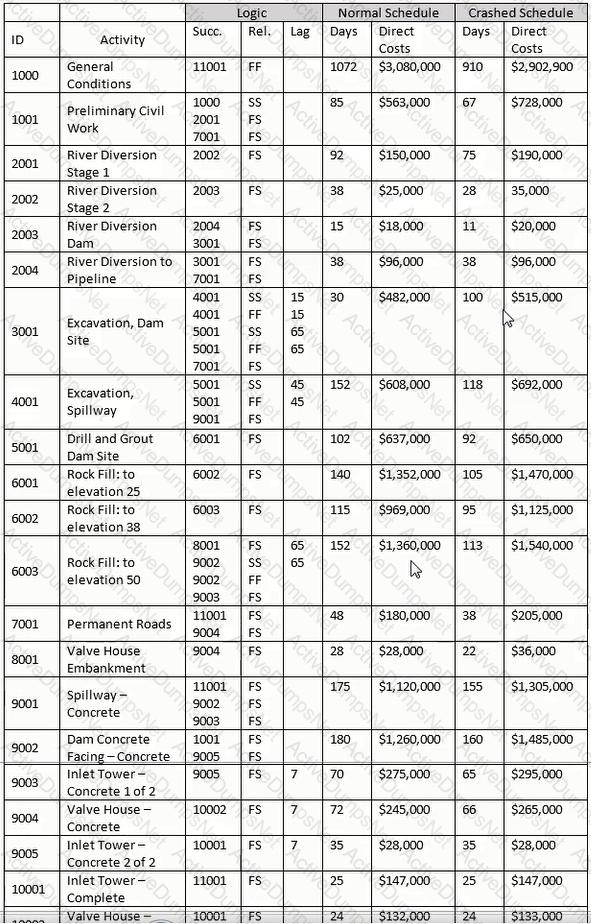
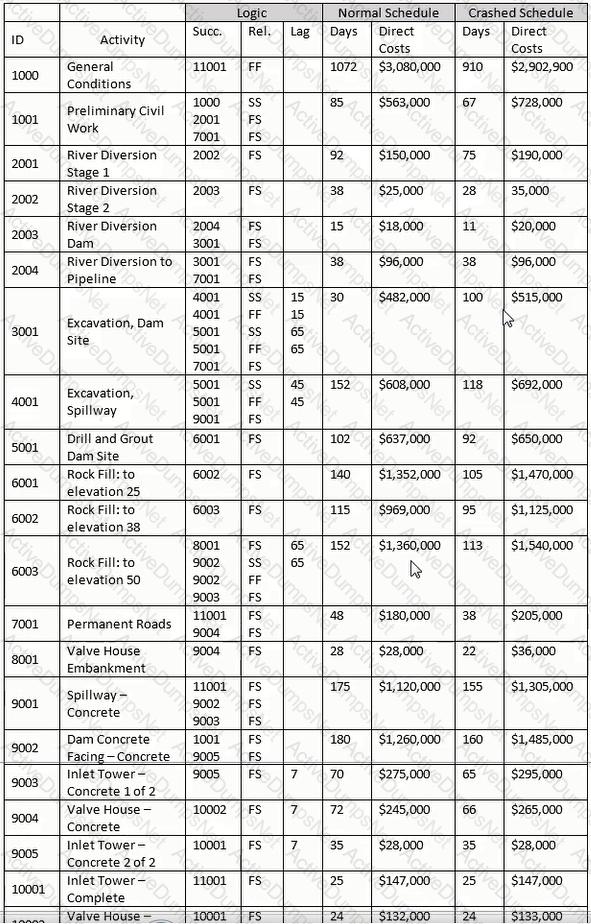
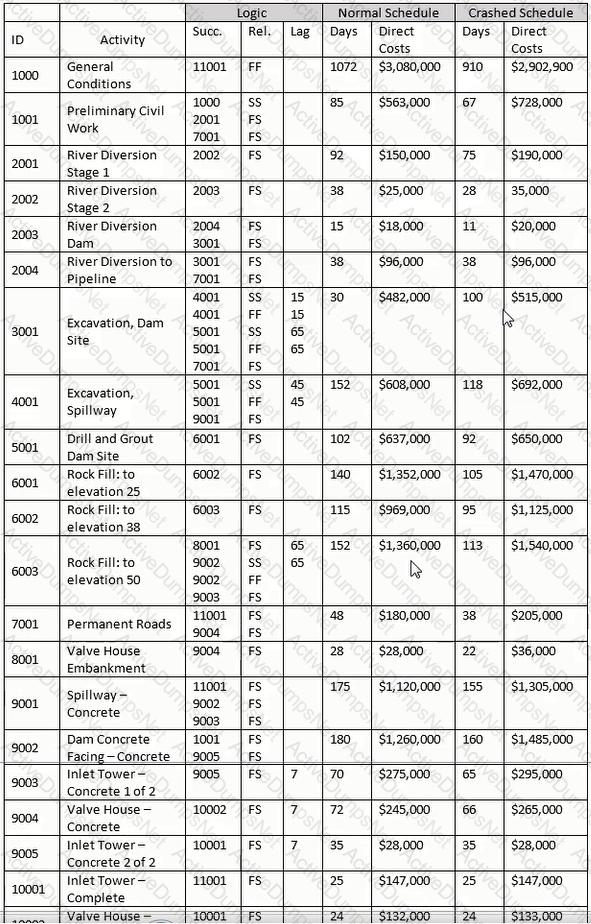
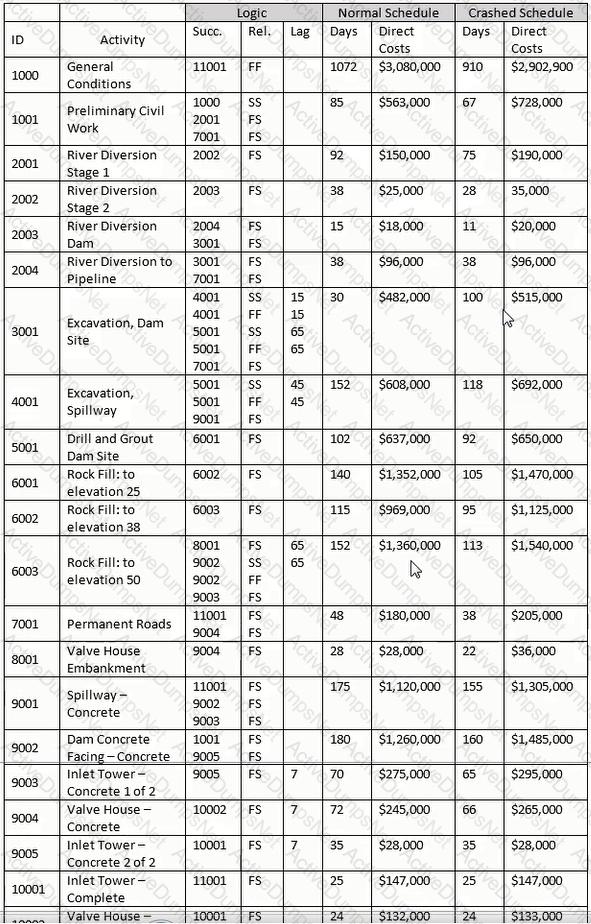
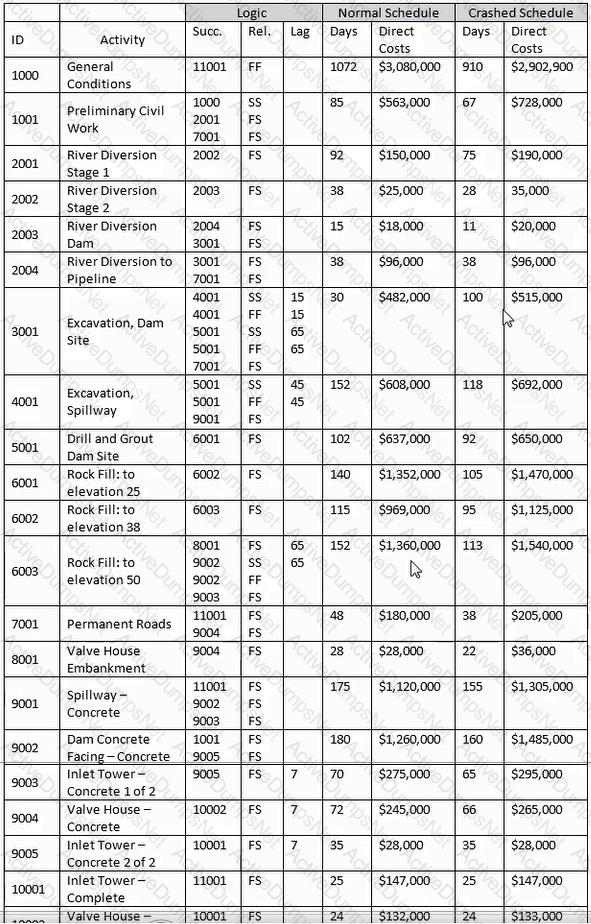
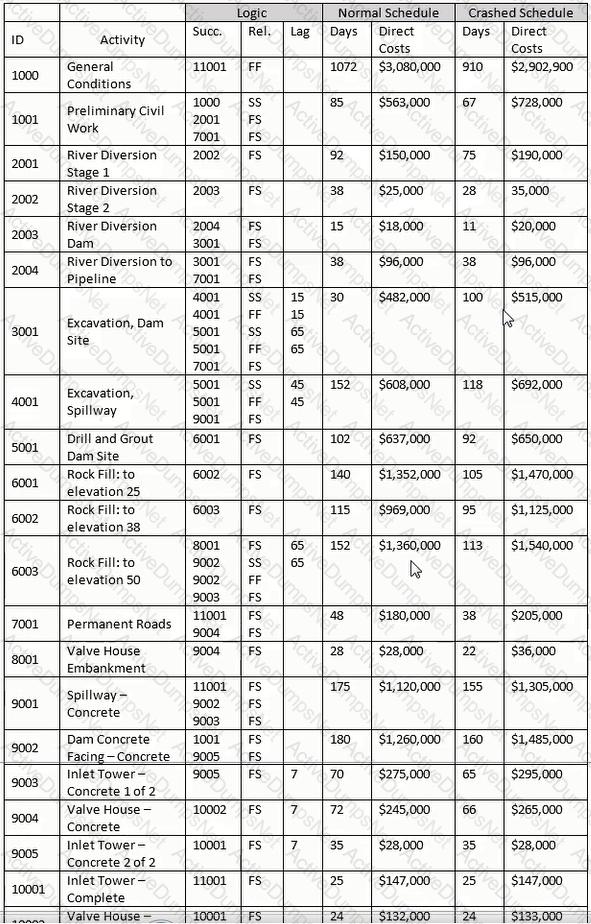
Using the "normal" schedule, and assuming you are billing on the last day of the month for previous month and for appropriate partial months, how many invoices will you have for this project?
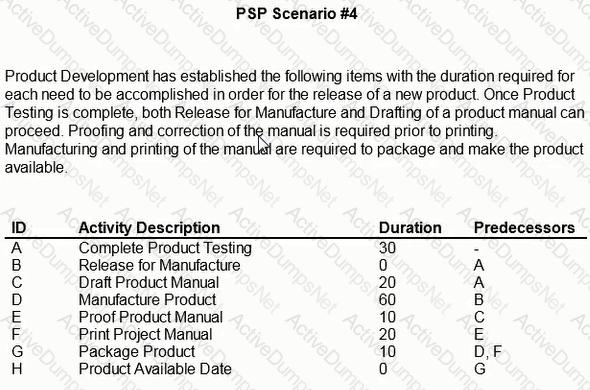
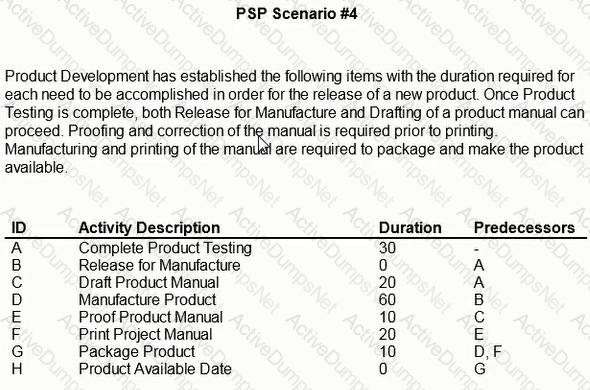
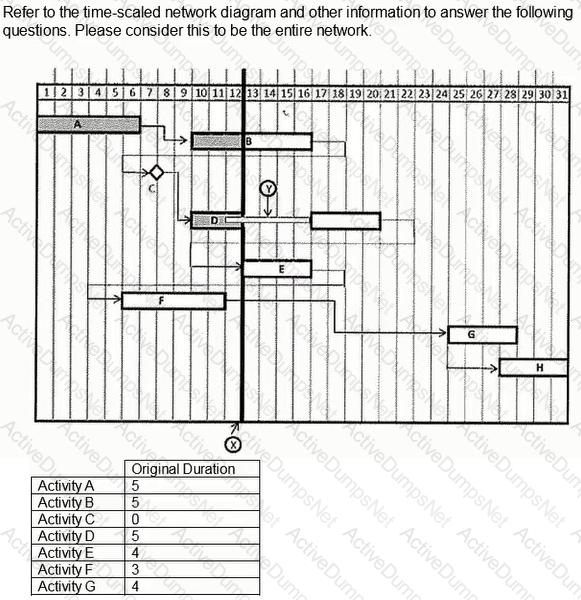
Due to a testing delay, release of the product for manufacture is delayed by 5 workdays and the product manual misses its print window at the printer. If the printer is delayed by 10 workdays, what is the delay to produce release?
Is activity 7001 pictured correctly in the precedence diagram?
During proofing of the product manual, a problem was discovered requiring 15 days additional time to affect a correction. How can the date of availability be maintained?
What is the workweek period for this project?
Which of the following is NOT true?
Using the crashed schedule, if you start Activity 2002 on 12 August 2021. what is the finish date for Activity 2002?
All the following describe the critical path of a schedule EXCEPT:
Using the normal schedule, what is the owner's total cost of the project?
Theoretically construct a summary activity for activities 2001 through 2004. Using the "normal" schedule, what is the cost of the hammock?
What changes to logic would eliminate Activity B from the critical path?
The addition of which of the following relationships would cause a logic loop?
Theoretically construct a summary activity for activities 6001 through 6003. Identify the governing predecessor and successor activities for the hammock:
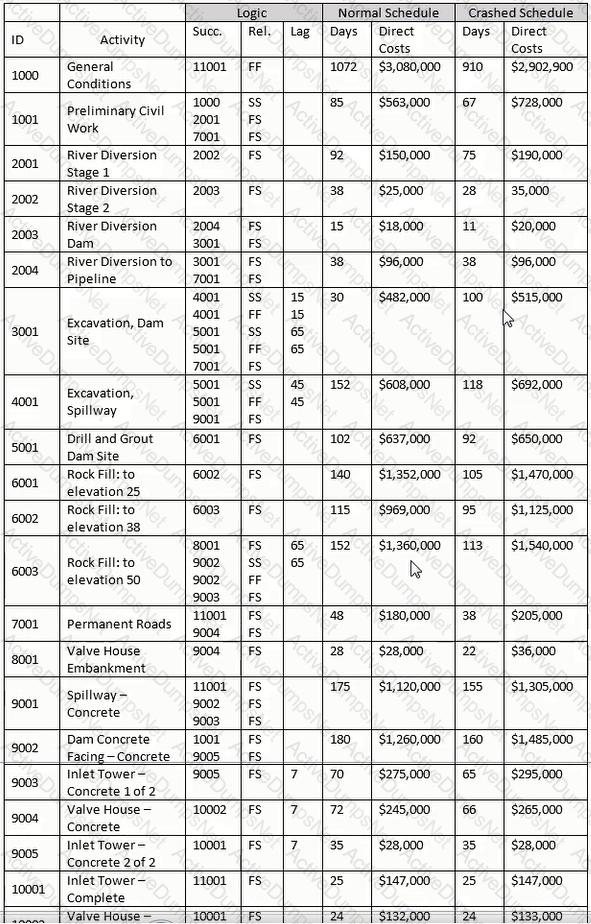
Using the "normal" schedule, given Activity 3001 and the relationship with Activity 4001, what is indicated?
How many workdays occur from the start of the Product Testing to the Product Available milestone?
Who will receive the most benefit from a master schedule of the Spring Highway project?
Management has determined the need to release the product 20 days earlier than planned. What tasks need to be expedited?
Determine the correct formula and date for the late start for the Activity 11001:
If someone wanted to constrain a project's end date so that any project slippage would cause negative float, they would do so by using
Estimate to complete (ETC) is __________________.
Which of the following is NOT a tool or technique used to perform scope planning?
What is the primary difference between the arrow diagramming method (ADM) and the precedence diagramming method (PDM)?
If no time extensions are granted and all actual delays are as described above, what will the total float calculation be at the end of the project?
Activity durations are normally estimated in an intuitive and subjective way. All of the following will improve duration accuracy EXCEPT
Considering the information provided for the project, what is the factor that most influences the successful crashing of the schedule?
Which of the following parties is NOT a stakeholder of the Spring Highway project?
How much Total Float does drafting the product manual have?
Assumptions made during the planning stage should be_____________.
In analyzing a logical chain of activities in a critical path method (CPM) schedule, what do differing total float values within that chain typically indicate?
Using the normal schedule, what is the early finish date and total float of Activity 10002?
What is the result of a forward pass calculation?
A good change management plan___________.
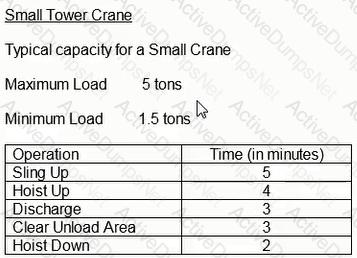
Assuming that you had only one crane capable of 30 lifts per day, 3 column pours requiring 28 lifts each, plus associated assorted work requiring an additional 150 lifts, what is the minimum planned working duration for this work?
Select the most appropriate explanation for use of a winter/wet weather seasonal calendar for use in this project?
What is the actual duration as of the status date or data date of Activity B?
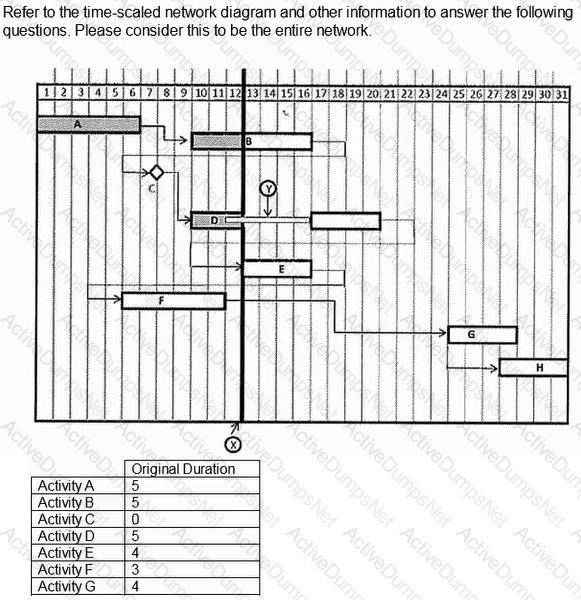
What is the relationship depicted between Activity G and Activity H?
Determine the correct formula and date for the late finish for Activity 9004.
Resource planning must take all of the following into account except for:
What day would Activity C complete if the duration of Activity A was reduced by five days?
Which letter of the alphabet best approximates the graphical shape of a project's cumulative cost baseline, or budgeted cost of work scheduled?
Which of the following types of delay will NOT result in a time extension and additional compensation for a contractor?
How could the structural steel drawing delay have been prevented?
SUBCO is a potential concrete bridge contractor based in a metropolitan area 300 miles away from your project. They have offered to supply manpower and equipment t BILCO at a per diem rate of $3,000 above their direct labor and equipment rates. In doing a cost benefit analysis, which of the following is NOT a consideration?
If a cost estimate assumes that 240 hours will be expended on a given activity, and the projected crew size expected to perform that activity is 5 personnel working and 8-hour workday, what is the calculated duration for the activity?
In a "crashed" schedule, which is a chain of activities that precede activity 2004?
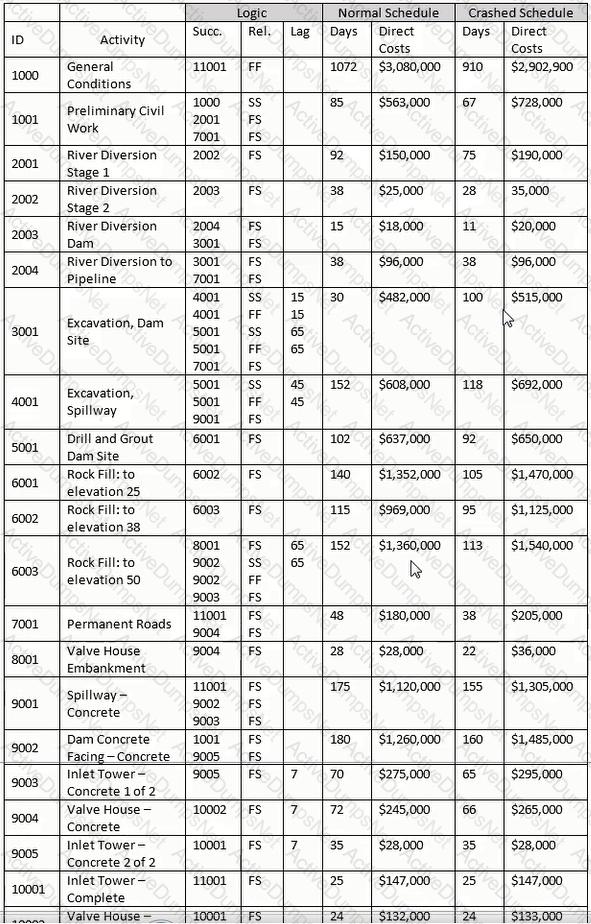
If a new hammock activity covering activities 6001 through 6003 is developed, what are governing predecessor and successor activities?
In an earned value-based system, a schedule performance index of less than one for the project indicates the project is: